Endpoint Protector 4
Photo Gallery
 |
 |
Endpoint Protector 4

Additional Info
| Company | CoSoSys |
| Website | https://www.endpointprotector.com/ |
| Company size (employees) | 50 - 99 |
| Type of solution | Hybrid |
Overview
Endpoint Protector 4 is a Data Loss Prevention (DLP) solution that protects companies’ sensitive data from threats caused by unintentional data leaks or malicious data theft. As a dedicated DLP product, Endpoint Protector 4 covers all major exit channels like e-mail, cloud file sharing applications, portable storage devices and others. The compatibility with Windows, Mac OS X, and Linux computers is the most advanced one available on the market, with granular policies and in-depth scanning and remediation techniques. Endpoint Protector 4 supports businesses in becoming compliant with industry regulations like HIPAA, PCI DSS, SOX, GLBA, and others, and preventing data breaches in order to preserve the company image, its Intellectual Property and employee records safe.
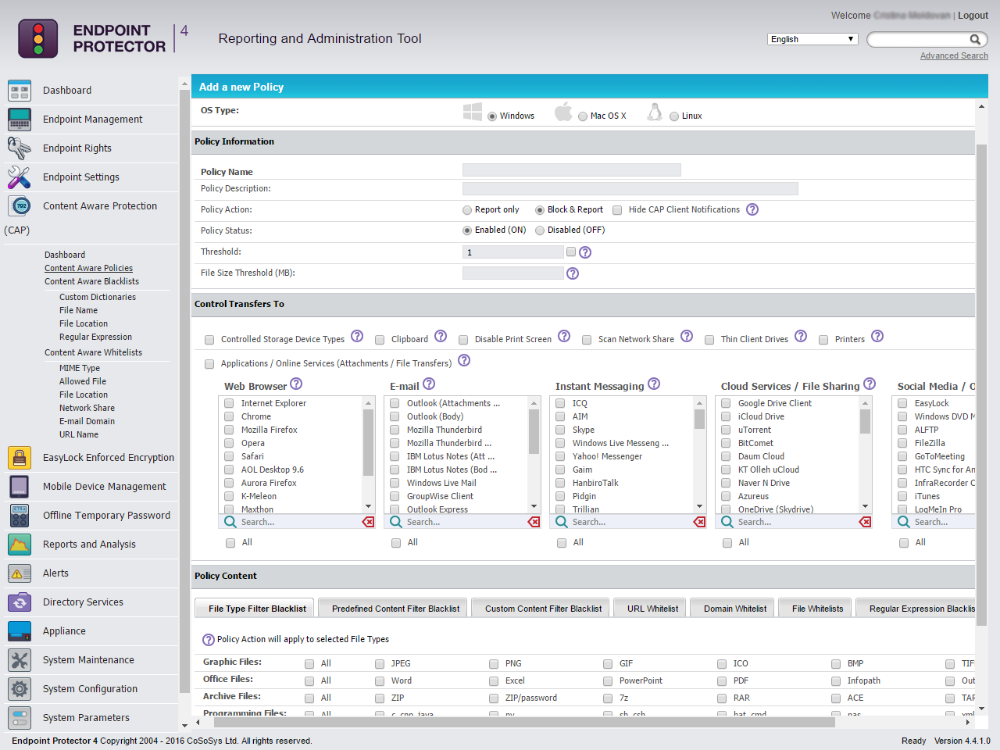
With the Content-Aware DLP features, organizations can create policies based on predefined content and keywords or file type, they can monitor and block unauthorized data transfers between departments if necessary and outside the network, and receive detailed tracking logs that can be used for audit and further decision making. Logs can be exported to SIEM solutions, so all your security events and records can be centralized in your enterprise tool.
The Device Control module within Endpoint Protector DLP allows organizations to scan and block sensitive data transfers to portable storage devices, or to block their usage. Additionally, our EasyLock software enforces encryption on removable USB storage devices, making sure data can only be saved on encrypted devices.
Endpoint Protector 4 is offered as Virtual and Hardware Appliance, and also as an EC2 Instance on Amazon Web Services, being up and running in 30 minutes due to the out-of-the-box implementation format.
How we are different
• Endpoint Protector 4 is a leading cross-platform Data Loss Prevention for Windows, Mac OS X, and Linux making DLP easy and affordable. While most of our competitors focus on DLP solutions for Windows, or provide limited features for Mac OS X, Endpoint Protector 4 offers advanced features for all platforms. When it comes to releasing DLP for Mac OS X and Linux we are pioneers, covering Mac OS X 10.4+ and several Linux distributions – Ubuntu, openSUSE, RedHat and more.
• We offer the most diverse implementation formats to cover all organizations’ infrastructures – Virtual Appliance, EC2 Instance on Amazon Web Services, and Hardware Appliance. Endpoint Protector is busting the myth of Data Loss Prevention being complicated and difficult to implement through the delivery formats and the intuitive interface.
• USB Enforced Encryption for Windows and Mac OS X with EasyLock, used in correlation with Endpoint Protector 4, sanctions the use of only encrypted USB devices, remotely managing and pushing USB encryption on USB storage devices. The solution is easily accessible and manageable from the Endpoint Protector 4 administration console.



