The Three Laws of Cyber Security and SOFTWARE Control Server
Photo Gallery
 |

 |
The Three Laws of Cyber Security and SOFTWARE Control Server

Additional Info
| Company | Mr. Jiri Napravnik |
| Website | http://rule.salamandr.cz |
| Company size (employees) | 1 |
Overview
Three laws of Cyber security
Software development is an exact science which can be described accurately.
Despite this ICT security has been for months if not years going round in circles. There are new security programs that react to things which have happened in the past. The situation has worsened and has spread to equipment which could be the target of attacks. These attacks are no longer focused on Pcs but further targets are smart phones, SCADA/PLC systems, IoT.
Software development is an exact science. In the area of development and
testing of software, it is necessary to describe the procedures and functions clearly. It is necessary to describe the output of SW modules or the whole application. By using clear descriptions it is possible to test in an easy manner. Today computer viruses are based on that their authors know the route how to connect the virus to existing files. This route has been known since the times of MS-DOS.
The second route is that virus authors find a one off way how run an infected computer because they may know a zero day weakness in the program or they abuse the trust of the user. Weakpoints in computer programs have been, are and will be. We should also take into account the inexperience and possibly the naivity of the average user.
Where is the problem?
When we want to defend ourselves against computer viruses we have to protect others files (operating systems, drivers and other applications) so that any virus cannot modify them. When we prevent the system from running unknown and unsafe files therefore we remove the location where computer viruses and fraudsters can cause damage.
This is a very simple solution. This solution will be beneficial for everybody.
How we are different
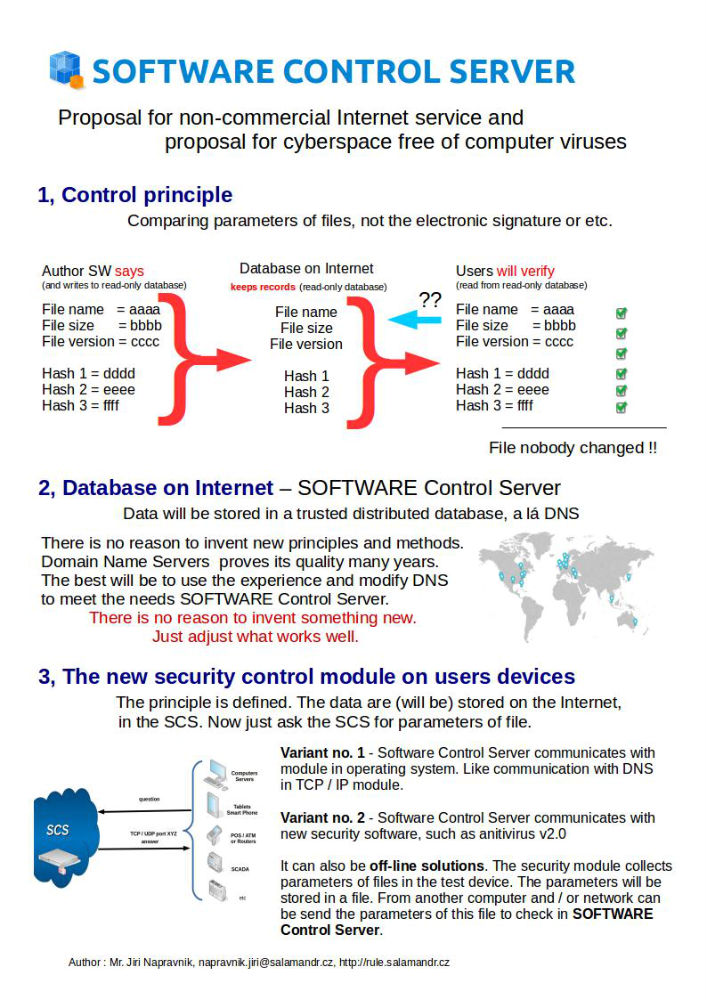
Three laws of Cyber security and non-commercial Internet services SOFTWARE Control Server
Software development is an exact discipline in which can be functions and procedures described accurately.
Software development is an exact science. In the area of development and testing of software, it is possible to describe the procedures and functions clearly.
In an environment based on a clear description of the tasks can be implemented a clear control.
The Three Laws of Cyber Security is not a commercial product. This is a proposal for new general rules and a proposal to think about a new security service over the Internet.
--
When we want to defend ourselves against computer viruses we have to protect others files (operating systems, drivers and other applications) so that any virus cannot modify them. When we prevent the system from running unknown and unsafe files therefore we remove the location where computer viruses and fraudsters can cause damage.
This solution will be beneficial for everybody. The average user will not live in fear that his/her computer is infected, system administrators will have less conerns with the strange behaviour of user equipment and servers and companies which are focused on ICT Security will be able to concentrate on real security threats and evaluting who and when did what.
Solution?
Law no. 1 - The checksum of the file on the user's device must be always
the same as the checksum of the same file by the author SW.
Law no. 2 – The network shall enable checksum verification
Law no. 3 - The operating system has to verify the checksum before starting an application and before using unverified system files.

