Abnormal Security
Photo Gallery
 |

 |
Abnormal Security


Additional Info
| Company | Abnormal Security Cloud Email Security Platform |
| Website | http://www.abnormalsecurity.com |
| Company size (employees) | 50 to 99 |
| Type of solution | Cloud/SaaS |
Overview
As the primary communication channel for business, email continues to be the biggest attack vector for threat actors. Despite extensive investment into email security, business email compromise (BEC) continues to plague organizations, amounting to over $26B in losses annually, according to the FBI. This represents more than 50% of financial loss due to cybercrime.
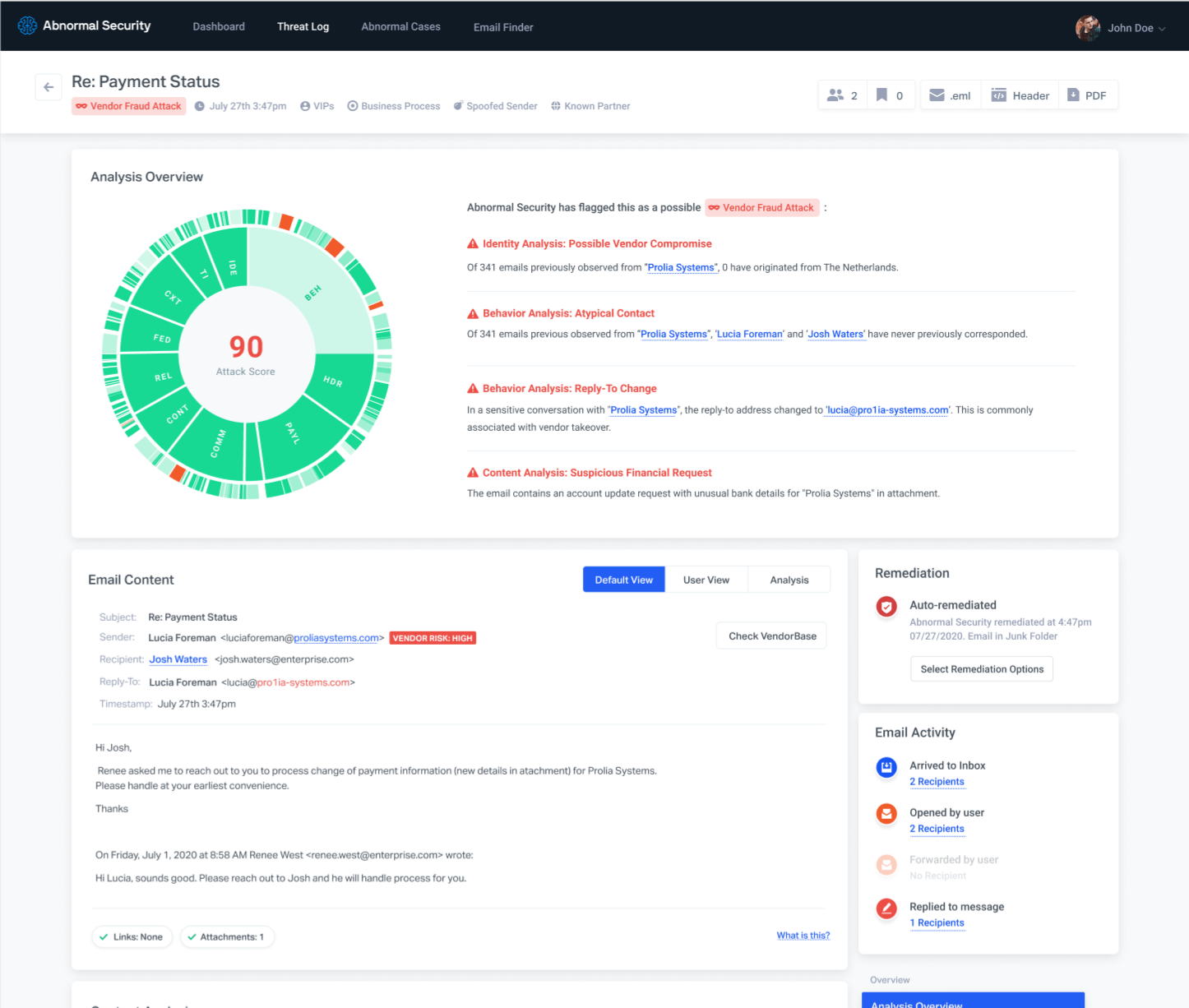
The Abnormal Security cloud email security platform protects organizations from the most sophisticated, socially-engineered email attacks ranging from targeted phishing, BEC and invoice fraud, using AI and machine learning. The company’s unique behavioral approach is highly complementary to existing threat intelligence-based technologies (email gateways such as Microsoft EOP/ATP or 3rd-party SEGs) and focuses specifically on stopping the single biggest threat today: socially engineered email attacks.
Abnormal Security’s platform is easy to deploy, integrating via Office 365’s native APIs in seconds. The AI-powered analysis requires no configuration or tuning and begins delivering results in just 24 hours.
The platform is complementary to the entire security stack. The API-technology architecture enables Abnormal Security to co-exist and complement existing email security solutions such as Microsoft EOP/ATP (or 3rd party SEGs) — with no configuration changes required to the existing security stack ( it is common for 3rd party SEGs to require Microsoft filtering be disabled for compatibility).
Abnormal Security also provides out-of-the-box integrations to SIEM and SOAR tools to dove-tail into current operational processes. The platform integrates to the “Abuse mailbox” to triage end-user reported attacks. This eliminates the bulk of the emails which are non-malicious, saving security analysts time and enabling them to focus on actual threats and incidents.
Abnormal Security develops an inside-out understanding of its people, organizational processes and the extended supply chain in order to stop targeted email attacks and detect compromised accounts that traditional email security solutions miss.
How we are different
Abnormal Security stops socially-engineered attacks with AI-powered detection. Our behavioral analysis techniques detect what threat intelligence-based approaches cannot. Proactive removal of malicious emails from the inbox means organizations can rely less on the ability of end-users to recognize these attacks. This effectiveness has led to Abnormal Security’s rapid adoption by the Fortune 500, as large enterprises scramble to find security controls to tackle the challenges of sophisticated, highly-targeted social engineering attacks such as BEC that existing solutions cannot address.
Supply-chain visibility and real-time risk analysis with VendorBase: Abnormal’s global, federated graph of the supply chain is continually analyzed and scored for risk. Abnormal’s self-learning platform analyzes communications to map organization's supply chain, which is referenced against VendorBase to quickly identify attacks such as invoice fraud which originate from both impersonated or compromised vendor accounts.
Unlike traditional email security solutions, Abnormal has the following technical differentiators:
- Cloud-native API-architecture: Seamless one-click API integration takes seconds and enables access to not only email, but more sources of data than any other email security solution today. This also enables visibility and protection to internal email traffic.
-Self-configuring and self-tuning: AI-powered detection requires no configuration and begins working almost immediately after integration, stopping attacks that traditional email security solutions are missing today.
- Explainable AI: Abnormal surfaces human-understandable evidence for every detection so analysts can be assured of the accuracy and precision of the platform.



