Photo Gallery
|

|
Abnormal Security

Additional Info
| Company size | 50 - 99 employees |
| World Region | North America |
| Website | https://abnormalsecurity.com |
NOMINATION HIGHLIGHTS
Socially-engineered email attacks cost organizations $26 billion in loss since 2016, according to the FBI. CEO Evan Reiser and CTO Sanjay Jeyakumar theorized they could use similar behavioral modeling techniques they used at Twitter on advertising to detect and stop these attacks. They partnered with engineers and data scientists from Amazon, Google, Twitter and Pinterest and security veterans from Proofpoint, Palo Alto Networks, FireEye and Duo Security to form Abnormal Security.
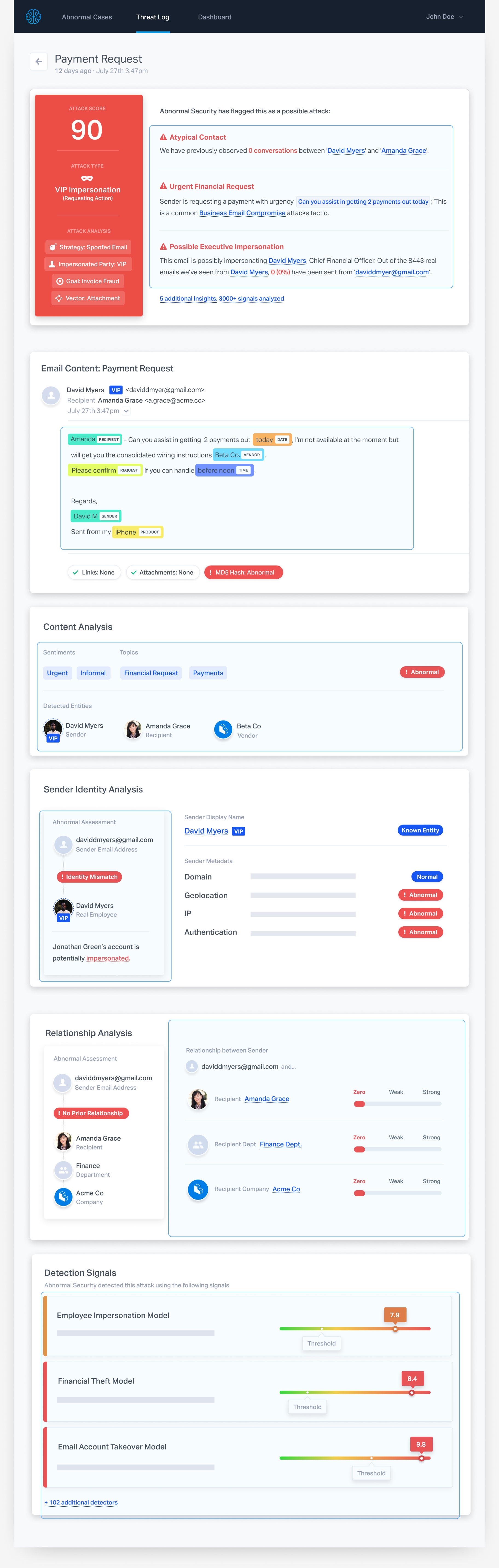
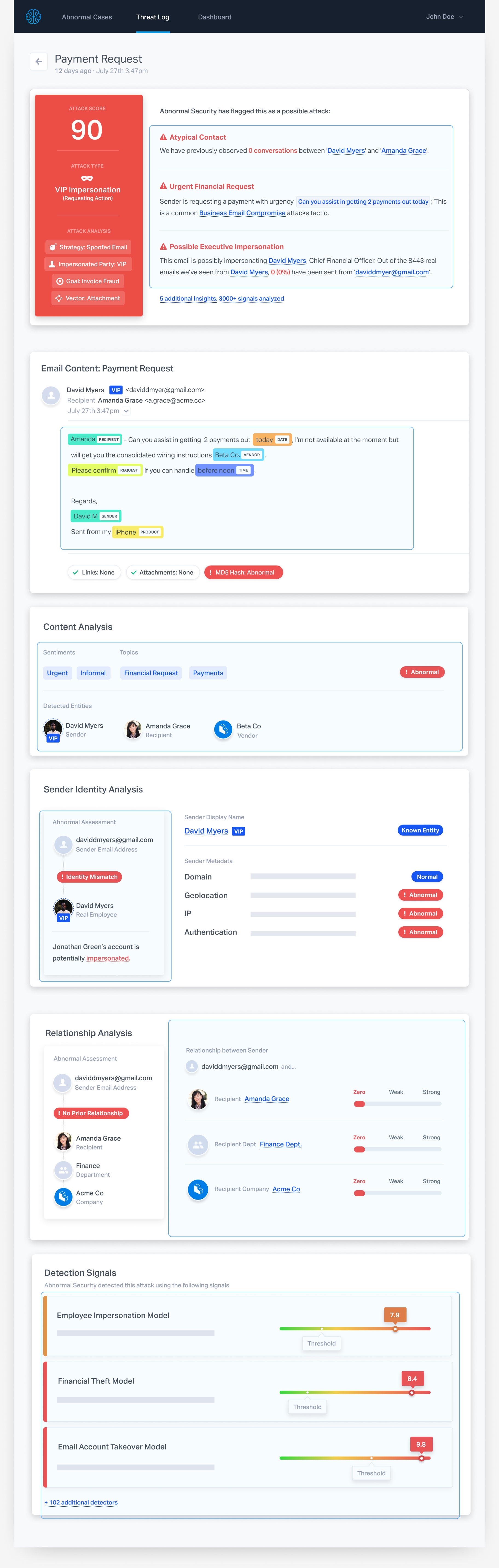
The Abnormal Cloud Email Security Platform protects enterprises from targeted email attacks that lead to executive impersonation, account takeover, financial damage, and organizational mistrust. The heart of the platform, Abnormal Behavior Technology (ABX), is responsible for stopping these attacks. ABX uses a rich set of organization-specific data to uniquely drive the Abnormal Identity Model, the Abnormal Relationship Graph, and Abnormal Content Analysis:
– The Abnormal Identity Model builds profiles of employees and third parties such as vendors and customers using hundreds of attributes extracted from dozens of data sources.
– The Abnormal Relationship Graph understands the strength of relationships by evaluating the cadence, topics and tone of communication, in addition to the frequency.
– Abnormal Content Analysis uses a variety of techniques such as computer vision and natural language processing to understand the context and meaning of communications.
ABX then combines these models with machine learning and reviews more than 1,000 signals, heuristics and sub-models to deliver automated insights and an explanation of each attack through an intuitive dashboard.
Unlike secure email gateways with re-configurations that lead to delivery interruptions, Abnormal Security integrates via Office 365 and G Suite API’s with just one click and requires no configuration.
Abnormal Security reduces the ongoing costs for organizations to manage threats by alleviating the workload of IT teams who focused on reviewing potential phishing emails, providing email security-related training and patching legacy equipment.
How we are different
- Abnormal Security goes beyond known threats, modeling the identity of both employees and external senders, creating relationship graphs, and analyzing email content to stop targeted socially-engineered attacks that traditional email gateways miss. According to Abnormal Security research, more than 70 percent of BEC attacks identified through Abnormal Security platform customer deployments were not initially blocked by security email gateway solutions.
- Unlike legacy secure email gateways that require mail routing changes, Abnormal integrates via Office 365 and G Suite API’s with just one click, requires no configuration and takes just five minutes for an IT admin to install.
- Abnormal Security saves businesses money not only by stopping fraudulent email attacks, but also by alleviating the workload of IT teams who traditionally focused on reviewing potential phishing emails, providing email security-related training and patching and provisioning legacy equipment.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

