Acceptto Continuous Behavioral Authentication
Recognized in the Category:
Photo Gallery
 |
 |
Acceptto Continuous Behavioral Authentication
Additional Info
| Company | Acceptto |
| Company size | 10 - 49 employees |
| Website | http://www.acceptto.com |
NOMINATION HIGHLIGHTS
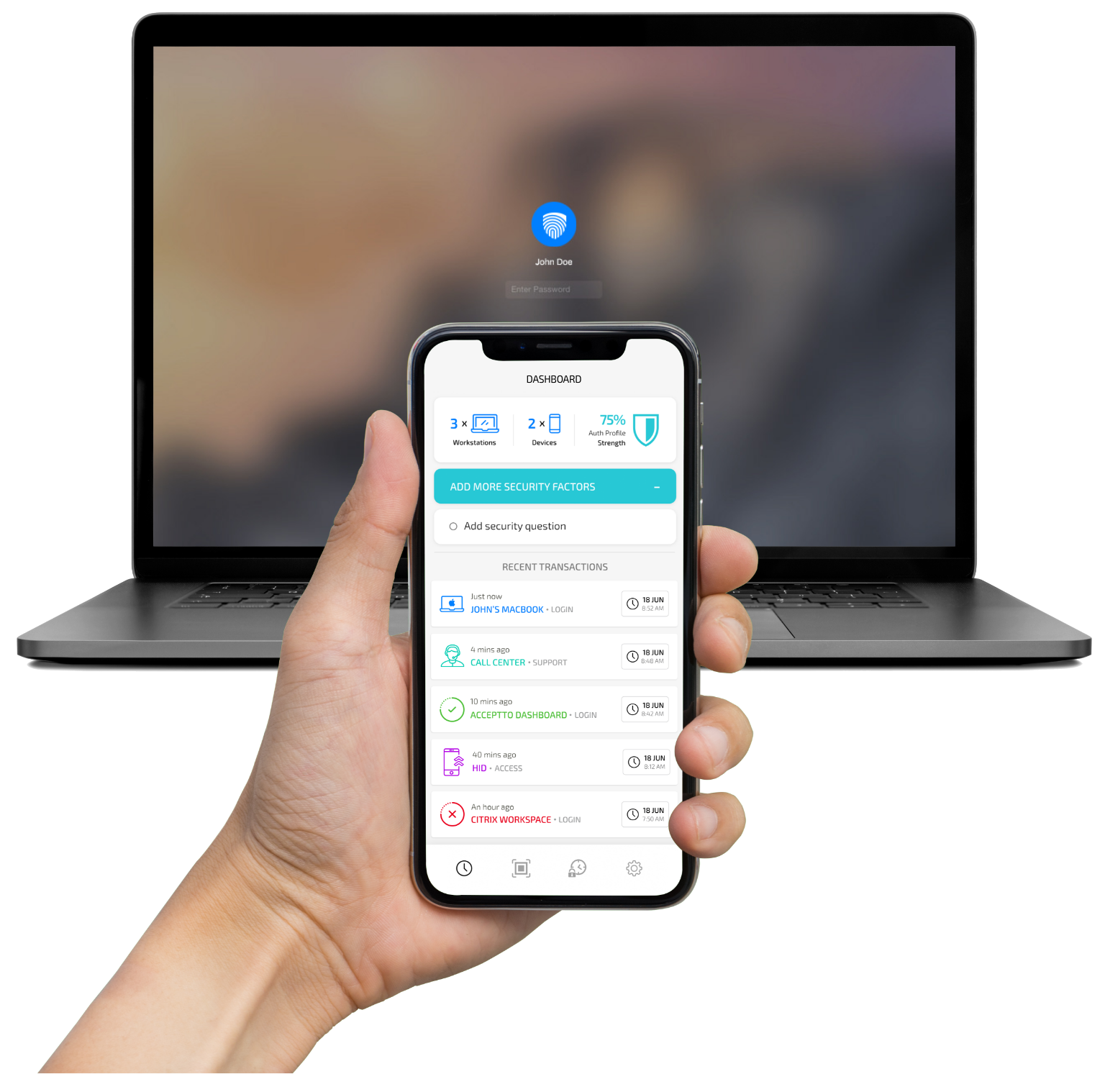
Unlike many solutions that treat authentication as a single event with “start” and an “end” and a binary “yes” or “no,” Acceptto’s Continuous Behavioral Authentication™ analyzes & verifies user identity and behavior by inferring contextual data to deliver a higher-level platform trust through pre-auth intelligence, during risked based context authorization and most importantly, post-authorization anomaly detection and continuous authentication.
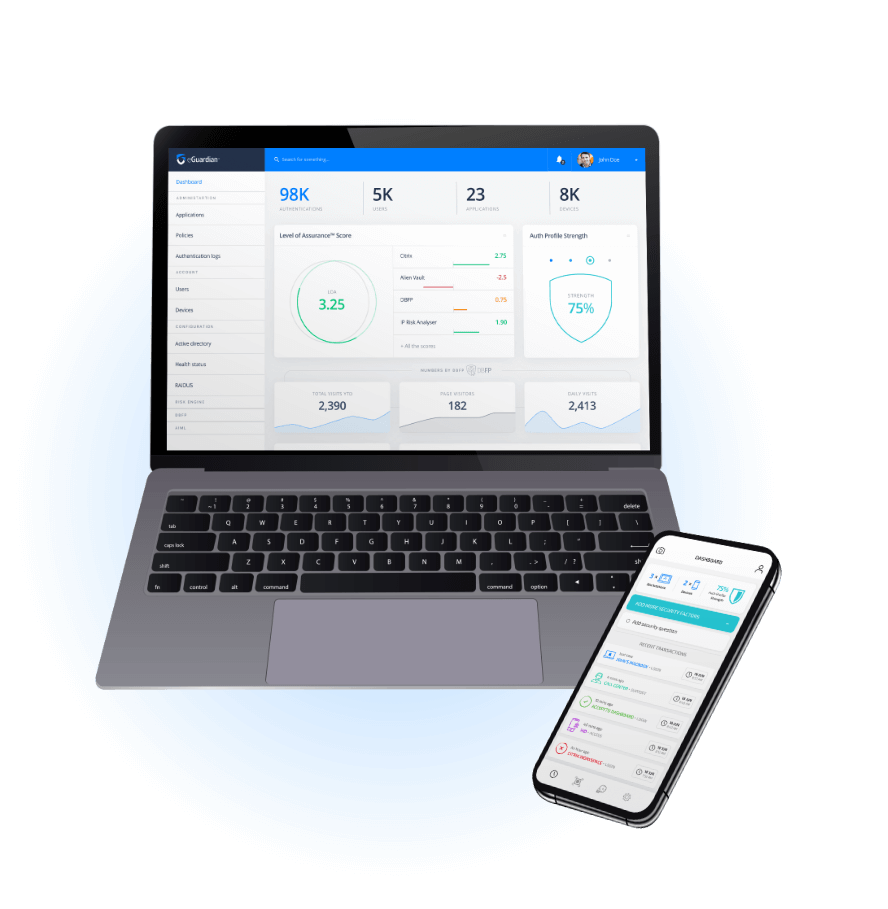
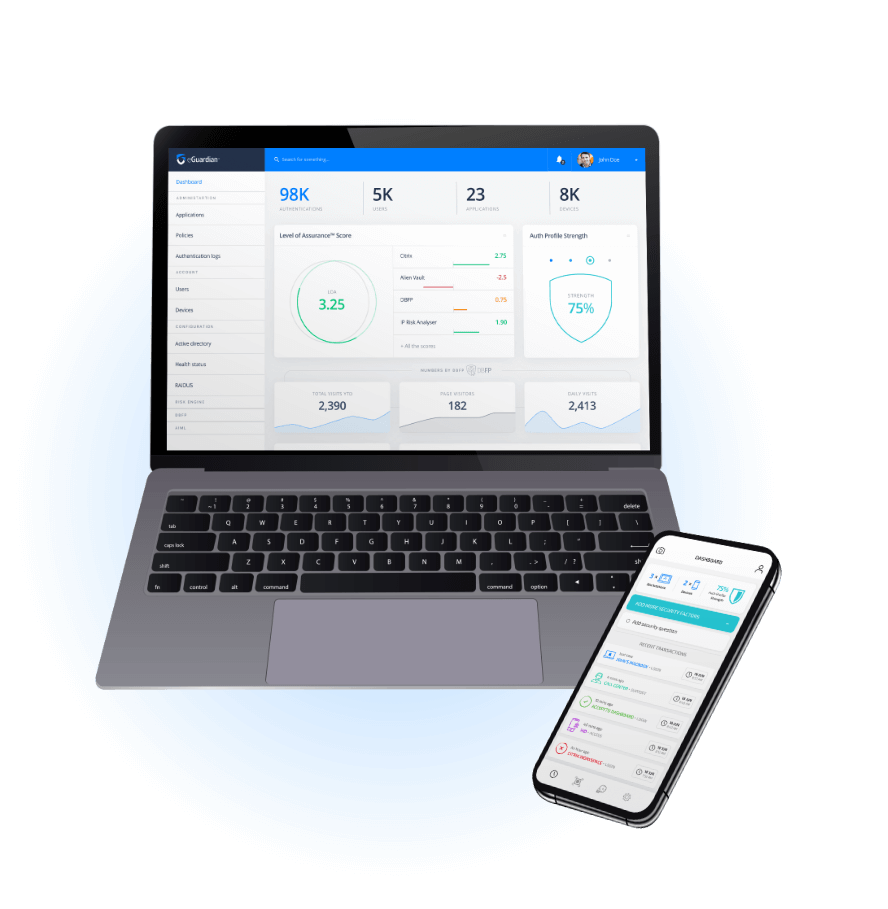
At the core of the Continuous Behavioral Authentication™ platform is eGuardian®, the intelligent engine that drives the convergence of physical identity and digital user DNA towards the creation of a resilient immutable identity. The It’sMe™ single sign-on (SSO) solution for web, mobile and enterprise applications, relieves users from the challenges of passwords, eliminates password reuse and resets, and neutralizes account takeovers. With Continuous Behavioral Authentication™, we can say goodbye to the password – forever!
Acceptto’s expert systems and behavioral modeling eliminates the reliance on weak and outdated controls to continuously analyze behaviors and definitively verifies legitimate user identity. Our transformative technology mitigates identity impersonation and access fraud while reducing friction for legitimate users, both within the enterprise and for consumers, providing our clients and partners with a better user experience, while saving money – due to the elimination of passwords.
How we are different
1. It is the first solution to secure customers and workforce identity with end-to-end risk-based Continuous Behavioral AuthenticationTM - without a password!
2. Our advanced and aggressive cybersecurity technologies never sleep. Acceptto’s continuous threat protection powered by artificial intelligence and machine learning (AIML) detects abnormal user behavior, eliminating cyberthreats, even post-authorization.
3.Acceptto is now FIDO and Citrix Ready certified, making it easier for companies and users to easily and effectively integrate into a more secure authorization process.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



