Attivo Networks ADSecure Solution
Recognized in the Category:
Photo Gallery
|

|
Attivo Networks ADSecure Solution

Additional Info
| Company | Attivo Networks |
| Company size | 100 - 499 employees |
| Website | https://attivonetworks.com/ |
NOMINATION HIGHLIGHTS
The ADSecure solution is truly a revolutionary way to protect against successful Active Directory attacks, without interfering with production AD operations, requiring logs, or complex rights and permissions management. Additionally, one of the best things about deployment is that you don’t have to touch or alter production Active Directory controllers for it to work. Implementation is exceptionally straightforward with the majority of the setup time spent on strategy for how in-depth you want to make the fake ADSecure environment and information.
ADSecure is a new product that can be easily installed as an add-on license to the ThreatDefend ® Platform or deployed as a standalone product.
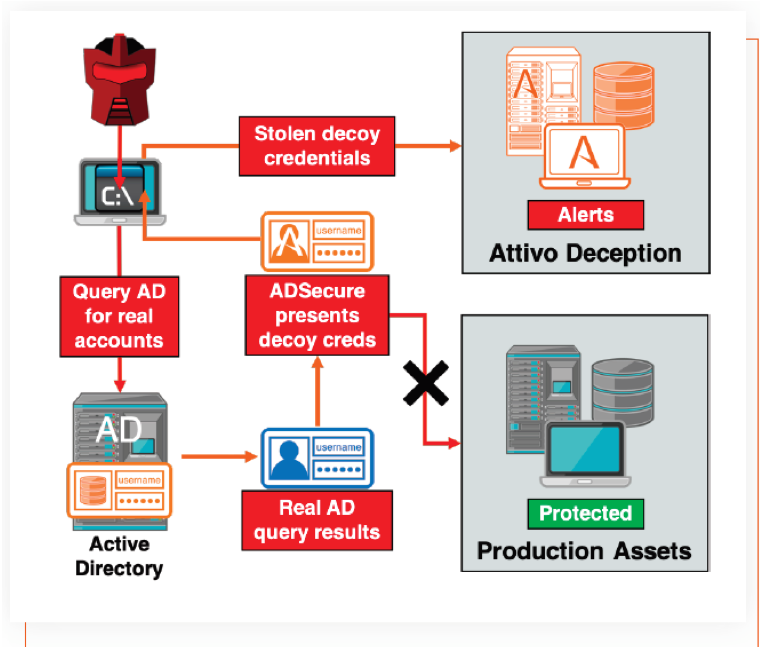
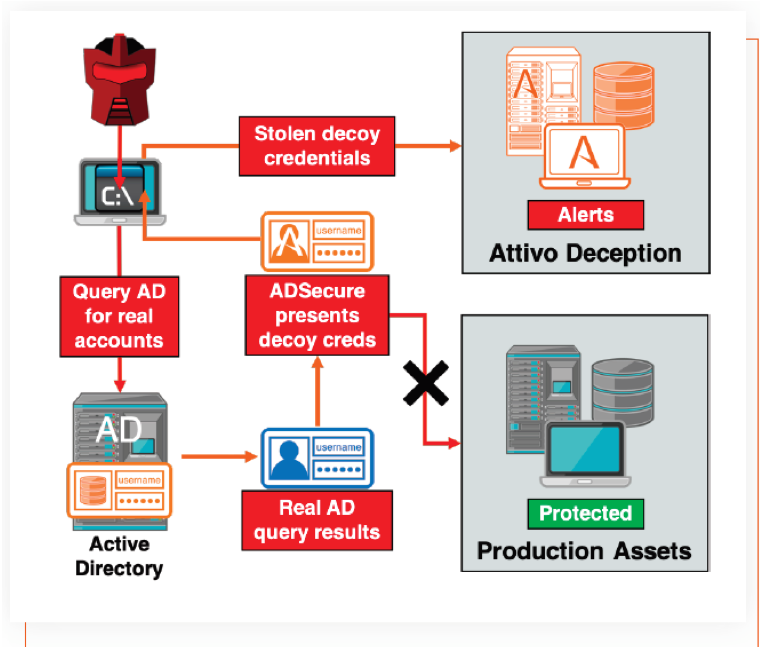
How it works
• The module detects unauthorized attack queries.
• It hides the high-value real credentials and system data from the attacker AD queries
• It returns deceptive alternative content, misdirecting attackers, creating an altered reality for the attacker, and making them unable to trust their tools
• The deceptive content directs attackers into the decoy environment
• The deception environment safely monitors the attacks for adversary intelligence
This method of prevention is an invaluable deterrent as attackers can no longer trust what they see or the tools they rely on. We pressure-tested the solution during beta and demonstrated the ability to reliably detect attackers early (within their first 20 commands) and to be able to engage the Red Team unknowingly for over 2 days.
How we are different
• Inherently, there is no ideal way to secure Active Directory environments. The Attivo ADSecure solution dramatically reduces risk by hiding real AD objects and returning fake data to an attacker, which, if used, diverts the attacker to a decoy environment.
• There is no need to touch or alter production AD to make this solution work, eliminating concerns that typically come with securing AD.
• Defenders can gather adversary intelligence as the queries and activities are redirected into the ADSecure decoy environment. They now gain the ability to collect and take action on company-centric threat intelligence.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

