Attivo Networks IDEntitleX
Recognized in the Category:
Photo Gallery
 |

 |
Attivo Networks IDEntitleX

Additional Info
| Company | Attivo Networks |
| Company size | 100 - 499 employees |
| Website | https://www.attivonetworks.com |
NOMINATION HIGHLIGHTS
The sheer volume of human, non-human identities, and managed services is leaving cloud security professionals overwhelmed and often blind to the extent of exposures. Attivo’s IDEntitleX Cloud Infrastructure Entitlement Management (CIEM) solution provides extensive visibility into cloud identities and their entitlements for attack surface reduction.
This cutting-edge solution reduces risk with a unified view of identities and exposures across the organization to address provisioning challenges while maintaining operational effectiveness. The offering uniquely includes multi-cloud support for AWS and Azure and provides detailed entitlement visibility for users, applications, virtual machines, containers, serverless functions, storage buckets, and other objects attackers target.
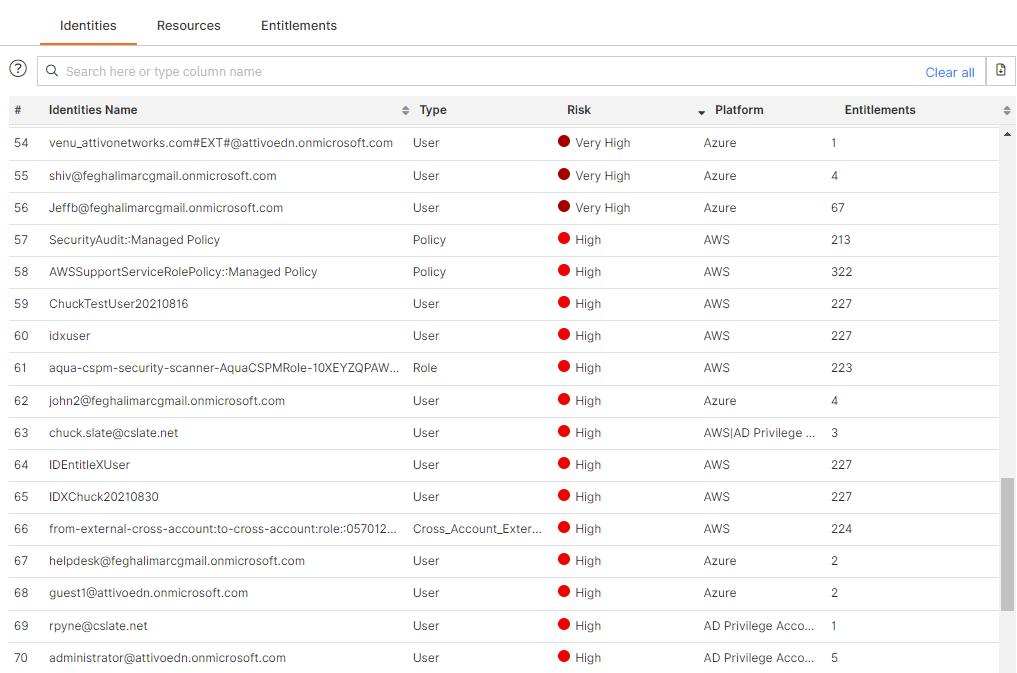
The IDEntitleX solution is the only CIEM solution that provides end-to-end visibility for identities and entitlements from an easy-to-use dashboard that seamlessly integrates data and clarifies findings:
• Scales to discover all identities, resources, and entitlements
• Supports multiple clouds in a consistent fashion
• Tracks changes to entitlements over time
• Provides end-to-end visibility, analysis, and protection: from endpoint to Active Directory to the cloud. (Other CIEM players are limited to visibility for the cloud itself, whereas IDEntitleX also provides visibility for the environments that are used as vectors into the cloud.)
• Visualizes access and risk from multiple points of view: identities, entitlements, and resources alike
• Enables clear and straightforward action to mitigate risk
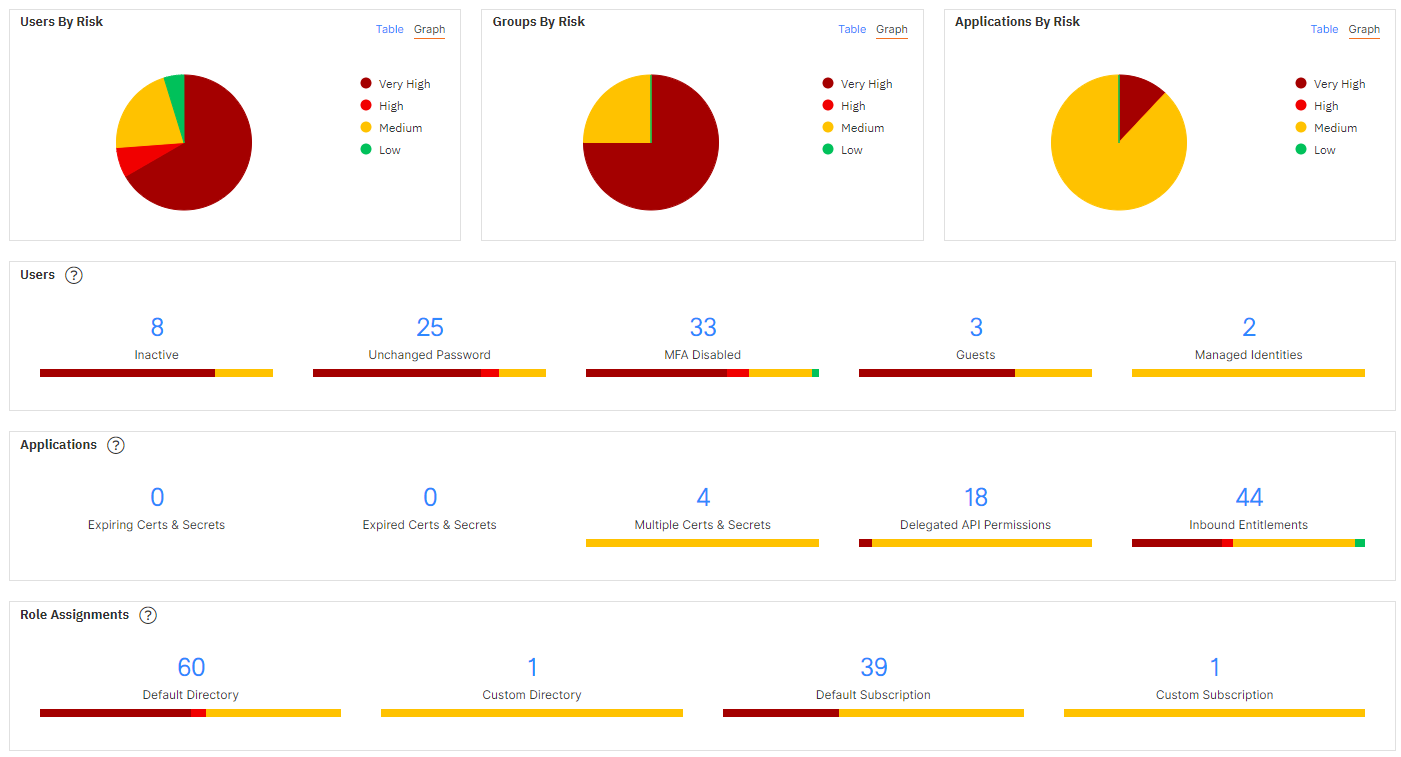
The UI provides viewing of information by identities, resources, and entitlements:
• Recent entitlement changes
• New entitlement assignments
• Password policy drift: inactive users, users with unchanged passwords and unrotated access keys, and users with MFA disabled
• Applications with expiring or expired certificates and secrets, and applications assigned delegated API permissions
• Outbound entitlements – Access an identity has to other objects
• Inbound entitlements – Access other objects have to a resource
Benefits include:
• Entitlement policy management
• Change monitoring and analysis
• Security posture analysis
• Account and entitlements discovery
• Entitlement visualization
• Cross-cloud entitlement correlation
How we are different
• With the IDEntitleX solution, organizations can analyze the complex web of enterprise identities to gain insight and proactively monitor a least-privilege approach to their security policies. The unified view of identities and exposures that security teams obtain from the solution helps them validate entitlement provisioning and reduce permission sprawl. Attivo Networks built the solution to extend its identity security platform and to protect organizations as they undergo rapid cloud transformation. The benefits include visibility into the entitlements granted to users, applications, virtual machines, containers, serverless functions, storage buckets, and other objects that attackers typically target.
• Through a single Attivo management console, security teams can use the IDEntitleX solution to gain insights and view cloud, endpoint, and Active Directory entitlements in one place. For example, IDEntitleX can show from a single dashboard a user’s entitlements to an AWS S3 bucket, an Azure key vault, and an AD container, as well as any endpoints that are caching their credentials.
• The Attivo Networks IDEntitleX solution has gained recognition from industry analysts, including Rik Turner, principal analyst at Omdia, who said: “In today’s heady atmosphere of accelerated app delivery, security is all too often remaining an afterthought. The rapid enterprise adoption of cloud computing has revealed a latent threat of ‘permission sprawl.’ This challenge is driving an emerging technology segment that prioritizes visibility and reduces the attack surface for identities and entitlements in the cloud. With the introduction of the IDEntitleX solution, Attivo Networks is well-positioned to emerge as a major player in the CPM or CIEM market.”

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



