Photo Gallery

|


|
Attivo ThreatDefend: Cloud Serverless Solution


Additional Info
| Company | ATTIVO NETWORKS |
| Company size | 100 - 499 employees |
| Website | https://attivonetworks.com/ |
NOMINATION HIGHLIGHTS
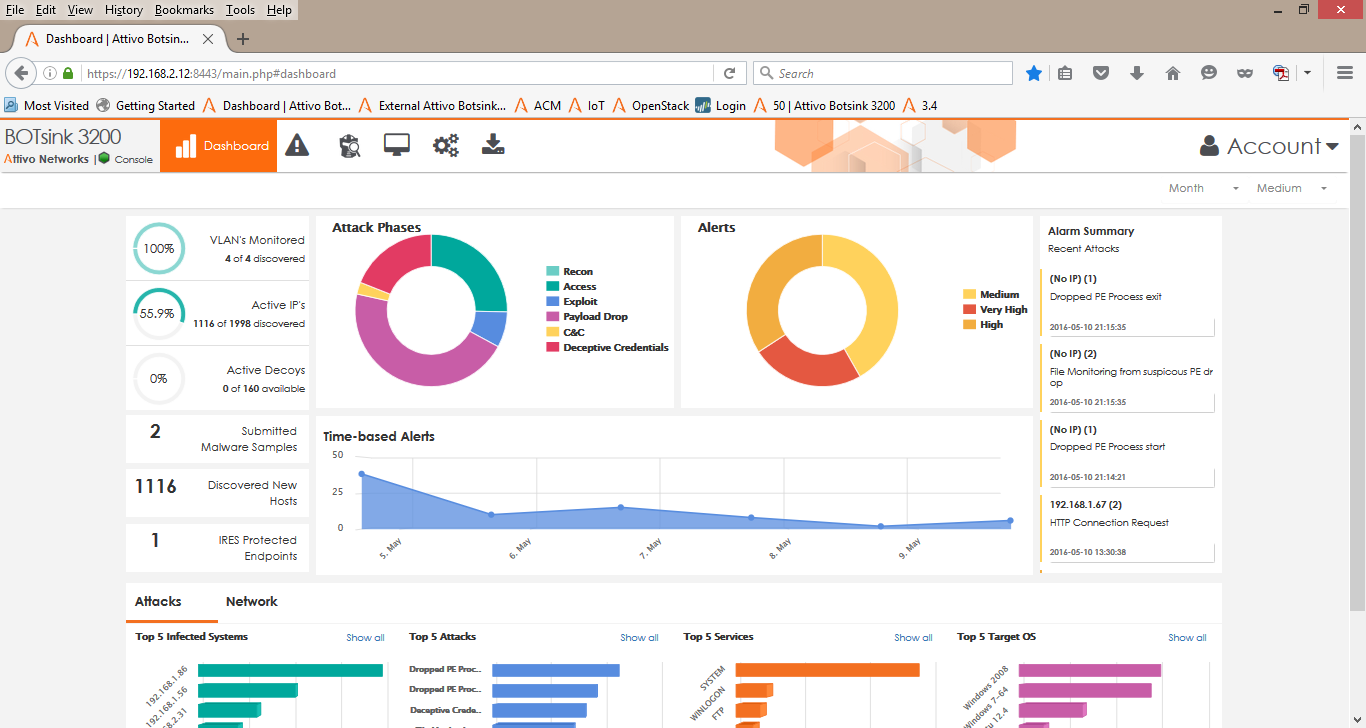
Serverless functions offer organizations economic, flexible, and rapid code deployment in cloud environments, but are difficult to secure with traditional security solutions and rely on the controls built into the cloud environment. With misconfigured access controls, improperly secured code, and lack of visibility into cloud activity, organizations suffer from security gaps that attackers exploit to compromise the serverless environment. The ThreatDefend Platform offers unique deception capabilities to detect attackers that infiltrate cloud environments to target serverless functions.
The ThreatDefend platform creates a deception environment that mirrors production systems and is composed of network decoys, deception credentials, fake applications, and false data to detect attackers early in the attack cycle as they attempt to conduct reconnaissance, steal credentials, and move laterally. The platform deploys on-premises or in the cloud with little operational or management effort and provides a full fabric of deception that blankets the enterprise to detect in-network attackers, provides unparalleled visibility into suspicious or malicious activity, and collect intelligence to improve defenses.
As part of the deception fabric, the platform creates a cloud-native deception environment of decoy servers that offer deceptive back-end services and credentials that point to them. These credentials deploy in serverless functions and lead attackers that steal them to exploit the available services to the decoys for engagement without impacting production functionality. The platform can also create deceptive serverless functions tied to decoy back-end services. As attackers conduct reconnaissance on the available functions to target, these decoy functions appear on the list for the attacker to exploit, providing early detection while misdirecting the attack to non-production functions. These overlapping deception features secure the serverless environment from unauthorized attacker activity while providing early detection of the attack.
How we are different
• The ThreatDefend Cloud Serverless solution provides early and accurate detection for serverless environments which are inherently difficult to secure with traditional security solutions and rely on the controls built into the cloud environment.
• The platform deploys on-premises or in the cloud with little operational or management effort and provides a full fabric of deception that blankets the enterprise to detect in-network attackers, provides unparalleled visibility into suspicious or malicious activity, and collect intelligence to improve defenses.
• Misdirects attackers away from production serverless functions into decoy functions that collect intelligence on their activities to better defend the environment.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

