Behavioral Intelligence Platform
Photo Gallery
 |

 |
Behavioral Intelligence Platform


Additional Info
| Company | E8 Security |
| Website | http://e8security.com/ |
| Company size (employees) | 50 |
| Type of solution | Hybrid |
Overview
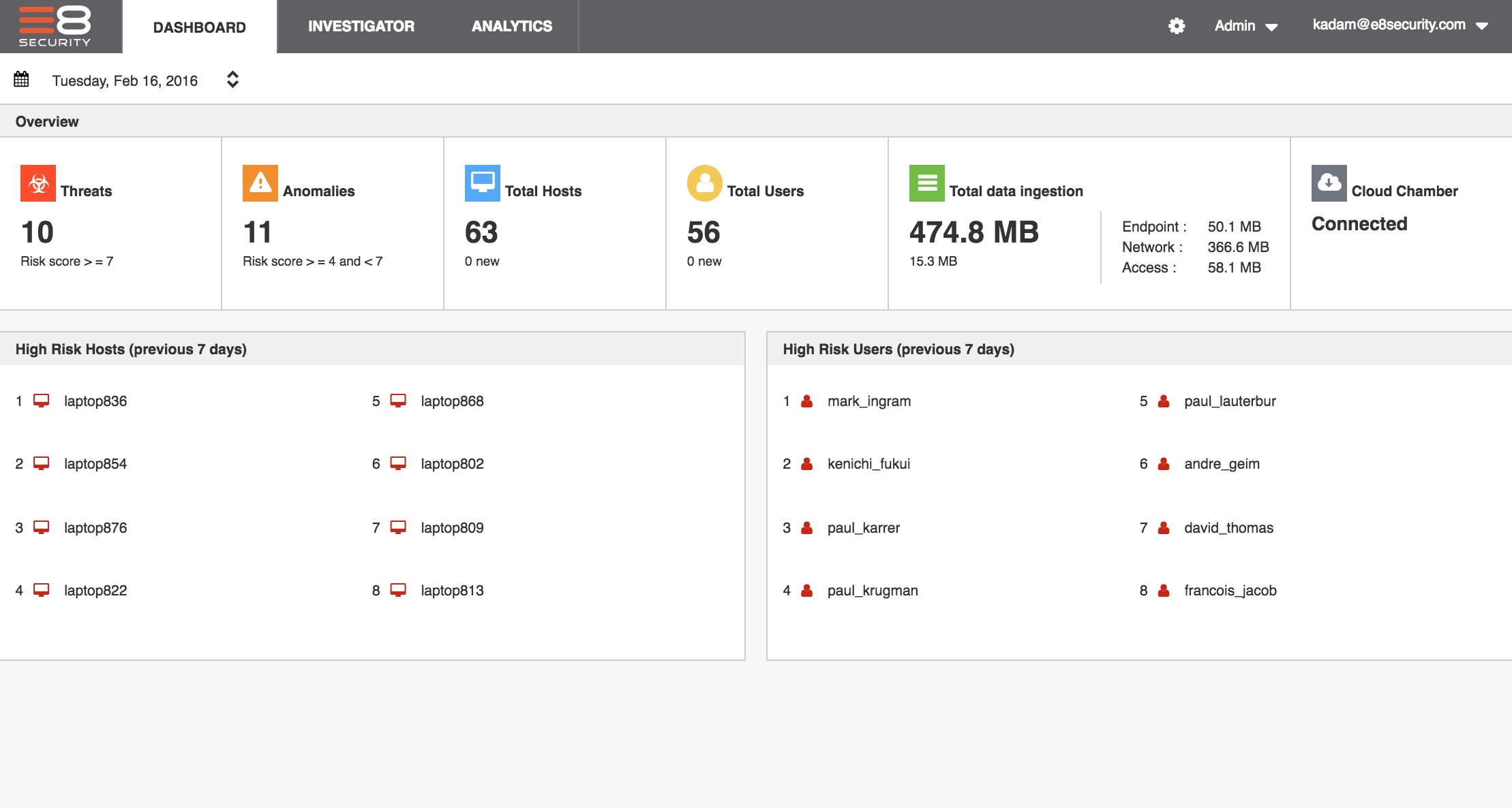
E8 Security is fixing the broken Security Operations Center. E8’s Behavioral Intelligence Platform applies self-learning behavior models to a customer’s own data to pinpoint hidden threats by identifying behaviors that are new, rare, and changed. The platform ingests data from any network, endpoint, and user/access data source, and groups behavioral threat indicators together as they perform various actions, enabling analysts of all levels to instantly understand which alerts are related, as well as which are critical, and which are not, so that response times are faster and efforts aren’t duplicated.
E8’s platform uses completely unstructured, self-learning detection. A pitfall of traditional threat detection tools is that they rely on rules and signatures, which require constant maintenance to stay relevant to the organization’s evolving environment and hacker’s changing threat tactics. With E8, there are no rules, which enables analysts to detect all kinds of threats, including zero-days and insider misuse.
Through its Entity Fusion technology, E8’s platform ties IP addresses to the device (or devices) and the person to whom it belongs so that analysts always know who to investigate. This has traditionally been one of the biggest bottlenecks for security analysts, which stalls prioritization and response. Analysts spend an average of 20 minutes per event figuring this out, manually combing through several different logging systems and comparing spreadsheets. E8 Security gives back those 20 minutes.
Through E8’s platform, customers are able to detect and monitor new devices, such as smart phones, personal laptops, printers, and even connected automobiles entering their networks, all of which are possible threat vectors. The focused visibility and threat prioritization provided by E8 has been instrumental in helping customers monitor all users and devices within their environments, detect and hunt for threats, and respond to critical incidents in significantly less time.
How we are different
- E8’s platform self-learns the customer environment, understanding what’s normal for individuals and groups without rules and policies, saving customers time and money.
- E8 Security reduces investigation time by providing the user and device identify, and alert grouping and prioritization information analysts need, and that they typically spend time working through manually.
- Focused visibility: Through E8 Security, security operations is transformed; security analysts can see the entire organization, and focus on the most critical issues.



