Best Managed Detection & Response Vendor
Recognized in the Category:
Photo Gallery

|


|
Best Managed Detection & Response Vendor

Additional Info
| Company | CyberProof Defense Center |
| Company size | 50 - 99 employees |
| Website | http://www.cyberproof.com |
NOMINATION HIGHLIGHTS
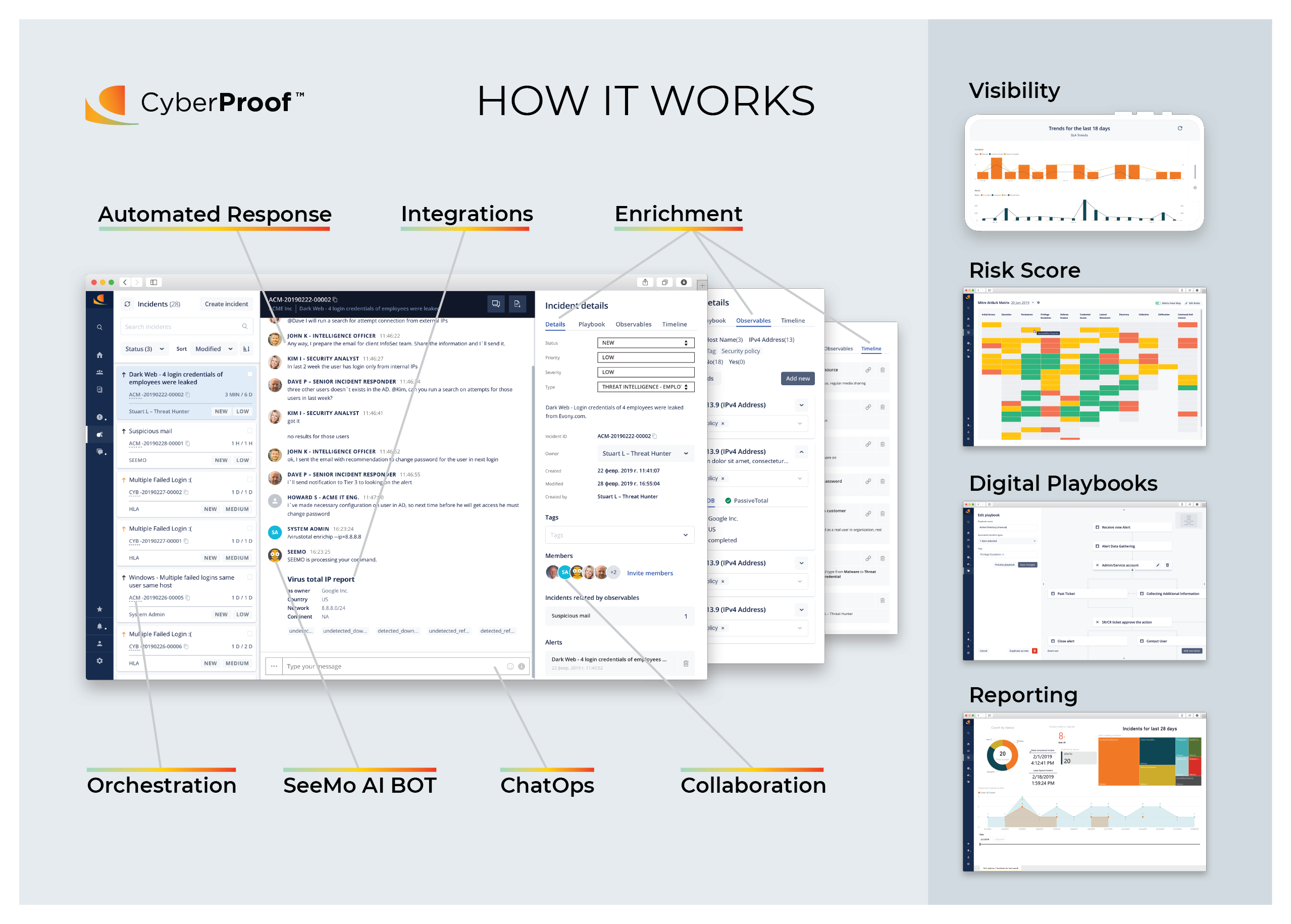
CyberProof is a managed detection and response vendor that is redefining the next generation of cyber security operations. Our uniqueness has recently been recognized by Forrester by placing us as the top leader of their Wave report on Emerging Managed Security Services Providers. Using AI driven automation and orchestration capabilities, CyberProof simplifies SOC operational activities, improves operational efficiency, and proactively detects cyber threats.
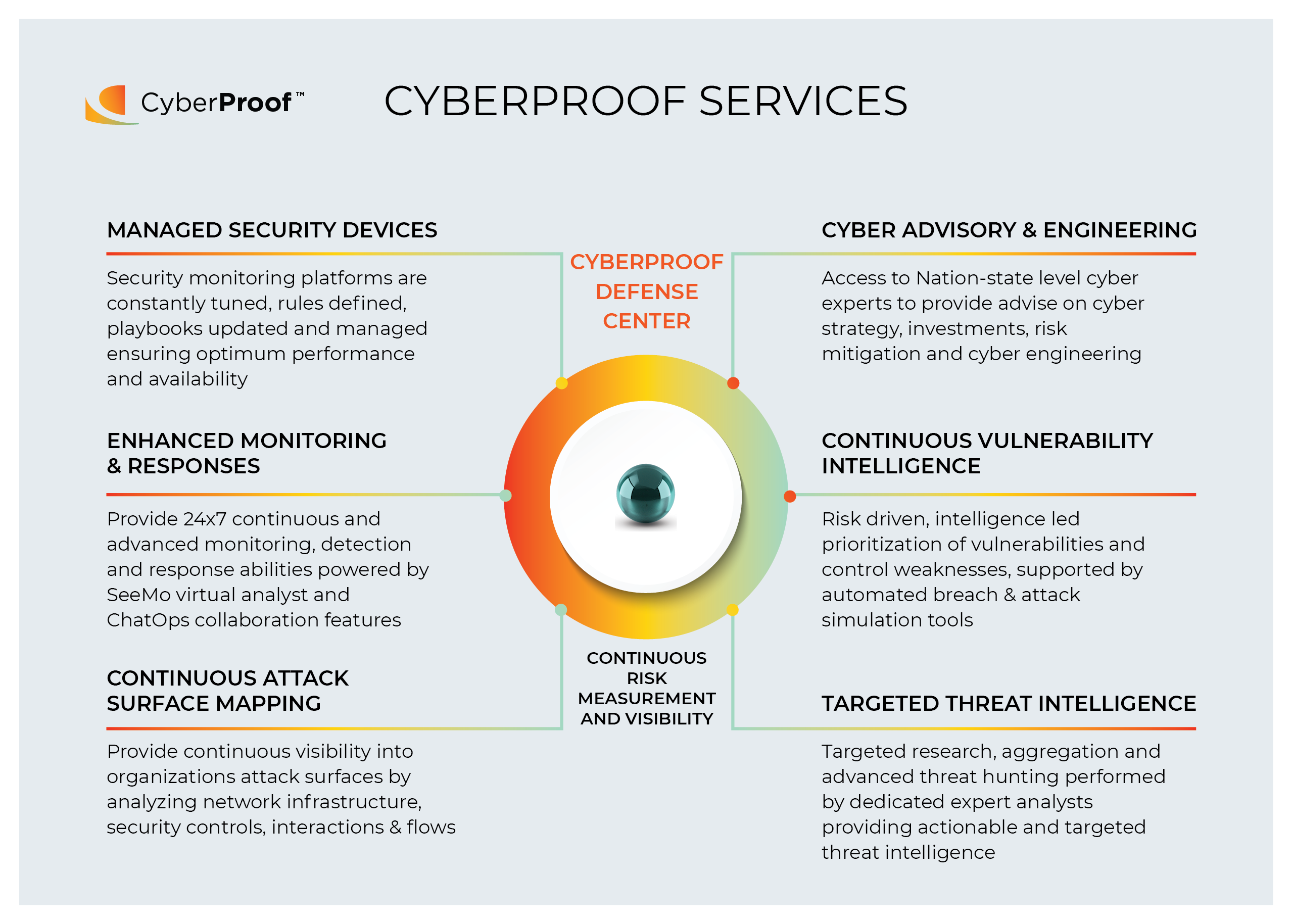
CyberProof works as an extension of our customer’s security team and is an integral part of their threat reduction objectives. CyberProof services includes security operations monitoring and response capabilities through its CyberProof Defense Center (CDC); a collection of pioneering services integrated with our own state of the art security orchestration and automation platform. The delivery of the capabilities is led by our team in Tel Aviv, who are military trained experts from elite divisions of Israeli intelligence and is assisted by highly trained security experts out of India, Singapore, Europe and NA for 24/7 coverage and monitoring.
The CDC platform functions as the core of the cyber defence infrastructure, providing the means and framework to detect and respond to cyber-attacks by containing and negating damage vectors aimed at critical assets, business processes and sensitive repositories. The CDC platform relies on broad access to data and intelligence from internal and external sources. Internally, it connects to a native cloud SIEM platform or where necessary directly to security sensors and IT infrastructure. Externally, it pulls information regarding threat landscapes, threat actors, vulnerabilities, exploits, campaign alerts and indications of breach related to its customer base.
The platform supports the entire security operations lifecycle workflows covering security event monitoring, vulnerability enrichment, threat intelligence, and event analysis to incident response, issue remediation and workflow management.
How we are different
CyberProof foundational concepts include:
• SeeMo, a virtual cyber team member, automates SOC operations and enriches data to reduce detection and response time
• Lowest cost per alert/incident handling
• Fastest time to respond and detect

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

