Photo Gallery
 |
|
Canopy Data Breach Response Solution

Additional Info
| Company | Canopy Software, Inc. |
| Company size | 10 - 49 employees |
| Website | https://www.canopyco.io/ |
NOMINATION HIGHLIGHTS
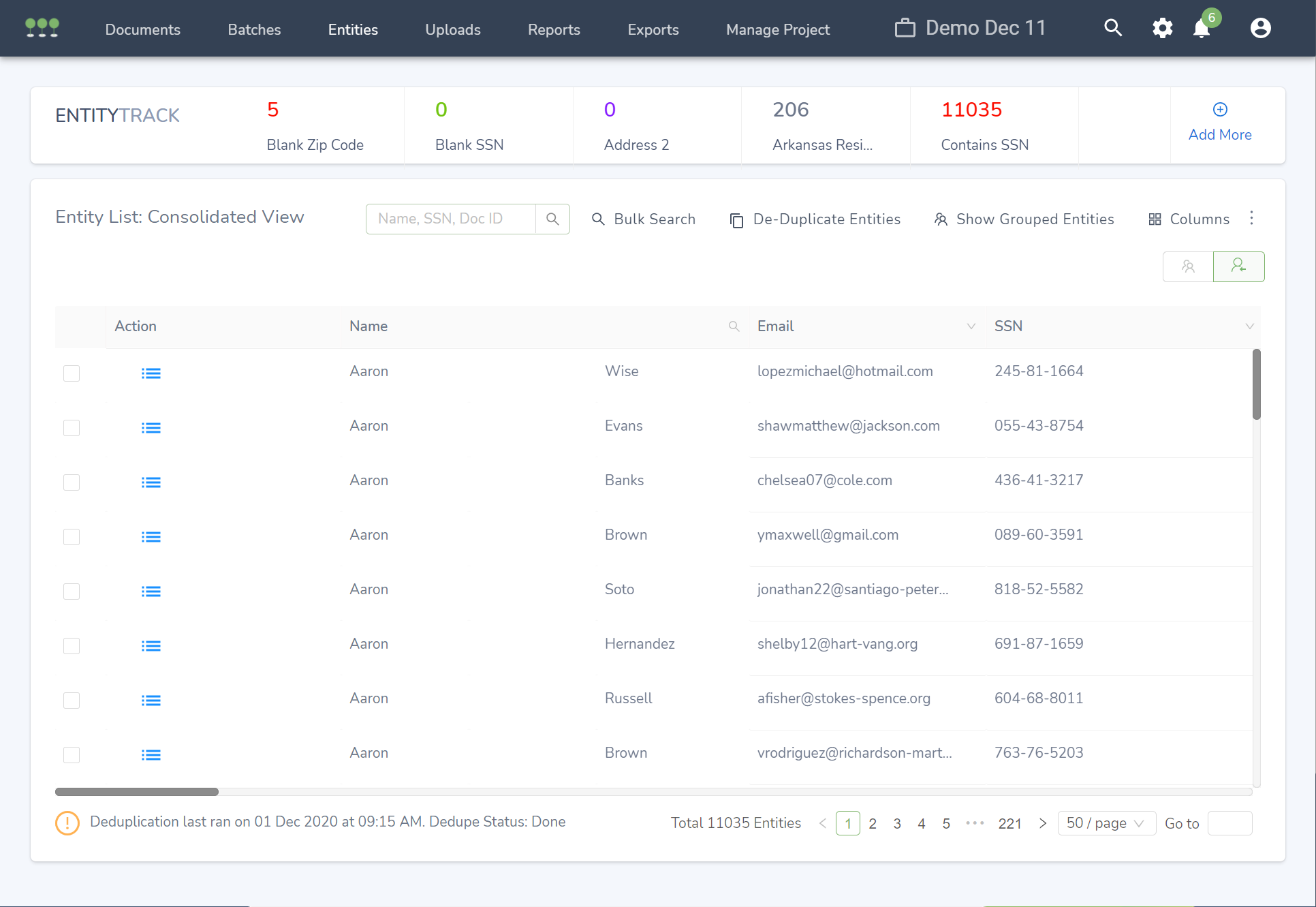
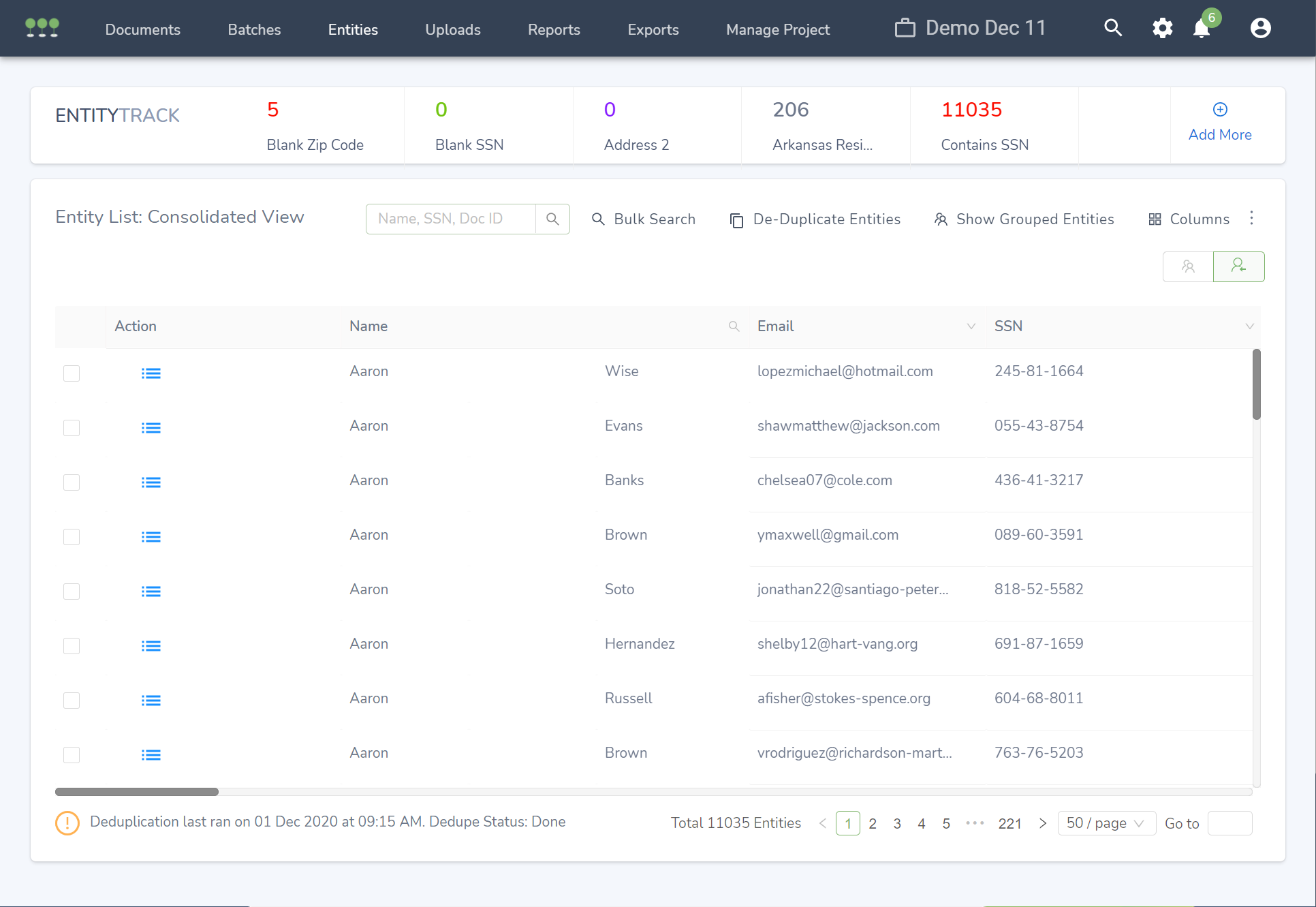
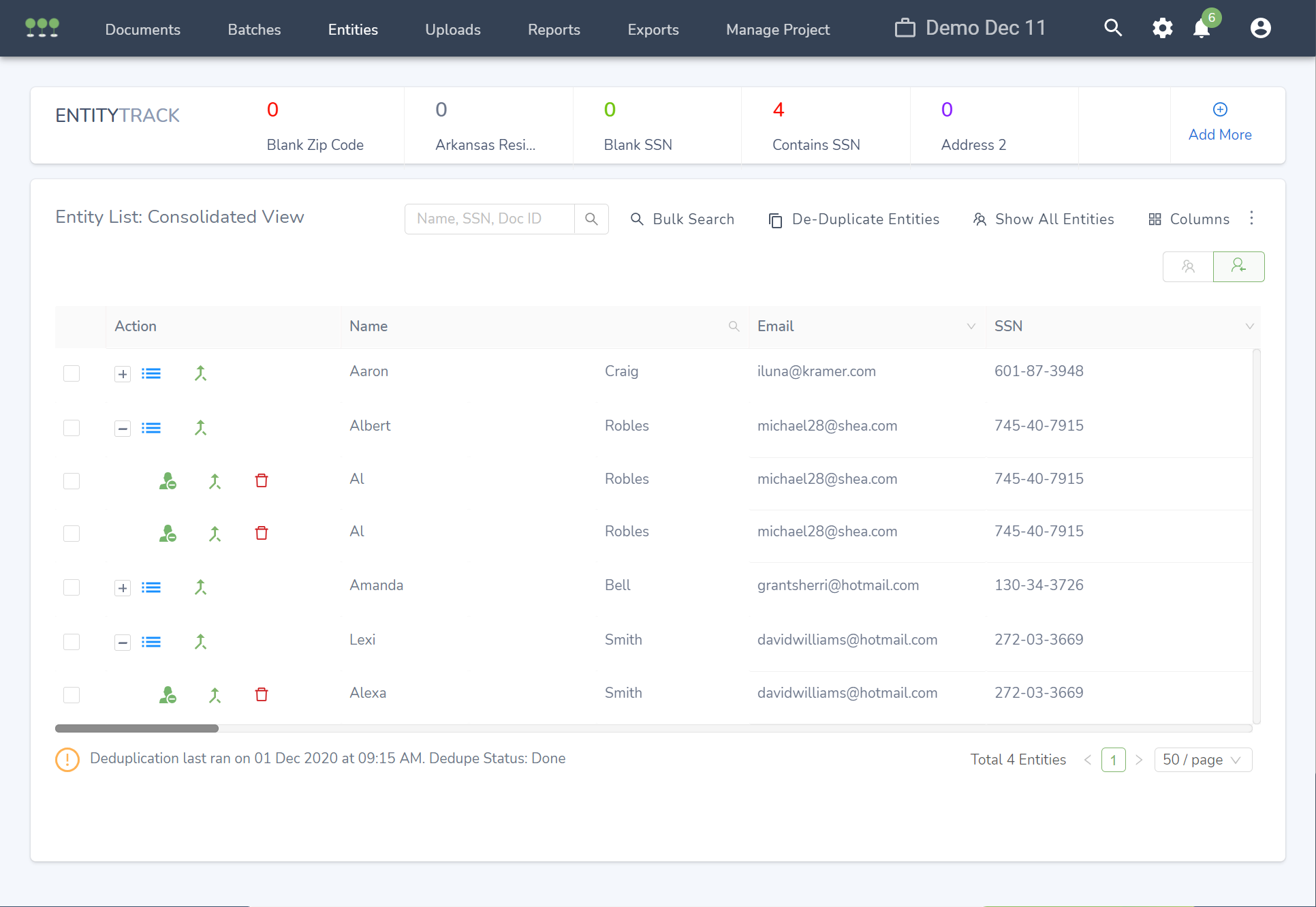
Canopy is the pioneer of purpose-built data breach response and notification software. Cyber incident response teams, legal service providers, and insurance providers rely on Canopy to mine and convert fragments of protected data found in a Business Email Compromise into an accurate list of affected individuals in a fraction of the time of traditional eDiscovery tools. Canopy’s patent-pending, continuous machine learning automates the detection, extraction, and relationships of PII and PHI across breached data.
As data privacy regulations continue to emerge on a global scale, each with varying stipulations, fines, and response times, complying with data breach laws becomes a challenge. Organizations require a purpose-built solution that not only has the ability to identify compromised PII but ties the PII to people.
Furthermore, organizations face significant challenges in determining if a “reportable” breach has occurred because without incurring a time-consuming and manual review process it is impossible to know what PII has been compromised.
Canopy works closely with our partners and their customers to ensure that they quickly and accurately compile notification lists in compliance with the privacy laws relevant to their projects.
Our patent-pending features purposefully solve the toughest data mining and workflow challenges faced by document review teams. Canopy’s innovations help reviewers rapidly consolidate PII and PHI within unstructured data into defensible entity lists. To help our partners overcome challenges as they arise, Canopy’s data mining experts work alongside their teams. Our developers then deliver weekly adjustments to our platform based on insightful customer feedback and enterprise compliance research.
Our focus on overcoming the specific challenges of document review and notification enabled us to create features that make projects take only days when they would have previously taken years. This drastically reduces the resources spent on data breach response and allows organizations to create more revenue opportunities.
How we are different
- Canopy has been used on over 500 data breach response projects, identified over 5 billion PII elements, and consolidated these elements to tens of millions of affected individuals that were promptly notified.
- Canopy improves accuracy by up to 50% by reducing false positives by up to 90% compared to traditional data mining processes, alleviating the resource-intensive manual data breach review process, and cutting costs by up to 50%, and ensuring legal compliance.
- Unlike traditional eDiscovery tools that simply identify if breached data is relevant to a specific incident, Canopy holds the ability to automate the relationship between compromised, unstructured data, and individuals requiring notification. Because of this, Canopy has been profitable since May 2019 and has realized 500% growth in annual sales over the trailing twelve months and grown its customer base by 300%.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



