CloudSphere Cloud Governance Platform
Photo Gallery
 |

 |
CloudSphere Cloud Governance Platform

Additional Info
| Company | CloudSphere |
| Website | https://cloudsphere.com |
| Company size (employees) | 100 to 499 |
| Type of solution | Cloud/SaaS |
Overview
According to IDC, total worldwide spending on cloud services will surpass $1 trillion in 2024. For many enterprises investing in cloud services, the complexity of public cloud service offerings and the emphasis on new service velocity has resulted in escalating security risks. A survey CloudSphere recently conducted in partnership with Dimensional Research revealed that many enterprises rely on different identity and access management (IAM) tools for each of their cloud services (e.g. Azure, AWS, GCP). This leads to increased security gaps and inconsistencies with how IAM is applied, and — more importantly — how it is enforced. These issues result in a higher probability of misconfigurations and data breaches.
CloudSphere solves these challenges by allowing customers to create and enforce IAM governance policies in hybrid and multi-cloud deployments from a single platform. With CloudSphere, customers can:
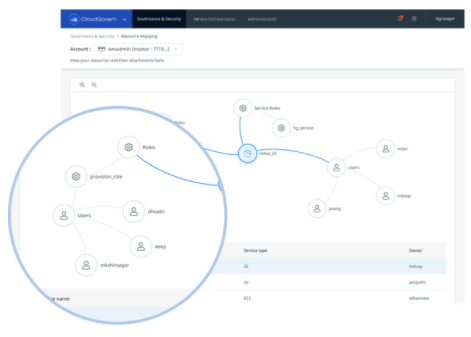
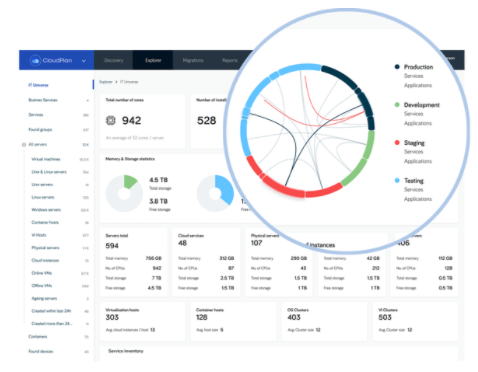
– Track who has access to critical cloud-based assets with dashboard diagrams visualizing access paths that provides insights into users and attached policies and permissions.
– Minimize the cloud’s attack surface with comprehensive security controls that monitor and control security status in real-time.
– Remediate IAM problems before they can be exploited with auto-remediation and assisted-remediation capabilities.
– Regain and maintain control in multi-cloud environments with policy consistency for access privileges to key cloud assets.
Traditional governance controls lack the visibility and reach required to address current issues, and a new approach is needed to reduce security risks and eliminate access sprawl. CloudSphere provides a comprehensive and visual approach to monitor, manage and retain visibility of users’, groups’ and resources’ access to cloud-based services and resources in the cloud. CloudSphere enables organizations to always understand who or what has access to services and functionality in real-time, ensuring comprehensive visibility and security across the cloud landscape.
How we are different
- CloudSphere’s agentless application discovery and dependency mapping solution allows practitioners to have a much more intuitive and logical view of identity, solving the problem of complexity in multi-cloud deployments. It is the only platform with Application Intelligence that allows customers to manage identity and security on a per-application basis in the cloud.
- CloudSphere provides a single platform and user experience for identity and security governance across all cloud providers, dramatically reducing the number of tools required. CloudSphere’s unique dashboard diagrams enable customers to visualize access paths in an easy-to-use format that also provides insights into users and attached policies and permissions. Rather than sorting through massive tables and event logs provided by companies like AWS and Azure, CloudSphere customers can group by application and visualize access paths, significantly reducing complexity. CloudSphere’s identity governance maps provide a clear graphical representation that immediately shows which employees and contractors have access to important resources in the cloud and on-premises. Customers can see who launched key resources in the cloud and detailed attributes of those resources like S3 bucket permissions, encryption, and whether logging is enabled. The platform also alerts customers in real-time to any issues that may need attention.
- CloudSphere further differentiates itself with its agentless application discovery and dependency mapping solution. While most competitors are agent-based, CloudSphere’s agentless approach simplifies cloud landscape monitoring by bypassing tedious management involved with deploying hundreds to thousands of monitoring agents. Delivered as a SaaS, the CloudSphere platform integrates quickly and easily to deploy across all common cloud environments.



