Photo Gallery
 |

 |
Cognito™


Additional Info
| Company | Vectra |
| Website | http://www.vectra.ai |
| Company size (employees) | 100 to 499 |
| Type of solution | Software |
Overview
The Internet of Things (IoT) is everywhere. Eight-five percent of enterprises surveyed are in the process or intend to deploy IoT devices, according to AT&T’s Cybersecurity Insights Report, yet only 10% feel confident they could secure those devices against cyberattacks. (https://www.business.att.com/solutions/Family/cybersecurity/cybersecurity-report/ )
Securing enterprise IT systems has been difficult enough. It’s widely known that cyber attackers operate undetected for an average of 99 days, but obtain administrator credentials in less than three days (Mandiant M-Trends Report 2017).
The addition of hundreds or thousands smart, connected devices, often designed without security in mind, vastly increases the attack surface. Many IoT devices are unable to run client-based security. They rarely get patches or updates, meaning vulnerabilities can be left unaddressed for months or years. From the power grid to wearable heart monitors, IoT systems are critical to across a broad range of consumer, operational, and business uses.
The Cognito™ automated threat detection and response platform from Vectra® automates the hunt for cyber attackers and speeds-up incident response. Using artificial intelligence (AI), Cognito automates the real-time detection and response to in-progress cyberattacks hiding inside enterprise networks. Cognito is the fastest way to find and stop active threats – from cloud and data center workloads to user and IoT devices.
Gartner states: “Cognito excels at the ability to roll up numerous security events to create a single incident to investigate that describes a chain of related activities, rather than isolated alerts that an analyst then has to piece together.”
How we are different
-- Cognito speeds-up incident response. With Cognito, stopping threats against IoT systems is no longer an impossible task. Cognito employs a unique array of AI techniques – including supervised (pre-trained), unsupervised machine learning and deep learning techniques – to detect and respond to in-progress cyberattacks in real time. Integrated intelligence enables Cognito to correlate events to reveal the larger attack narrative.
Threats are automatically triaged, scored and correlated to compromised hosts, and attack behaviors are correlated across hosts to provide the “narrative” of developing attacks. Threats are prioritized on an intuitive user interface while alerting and remediation actions are taken with other security technologies that are integrated with Cognito. No signatures or client software is needed.
Cognito reduces customers’ security operations workload by 29X or more (2017 Vectra Attacker Behavior Industry Report). https://info.vectra.ai/hubfs/Vectra-Attacker-Behavior-Industry-Report-2017-Q1.pdf
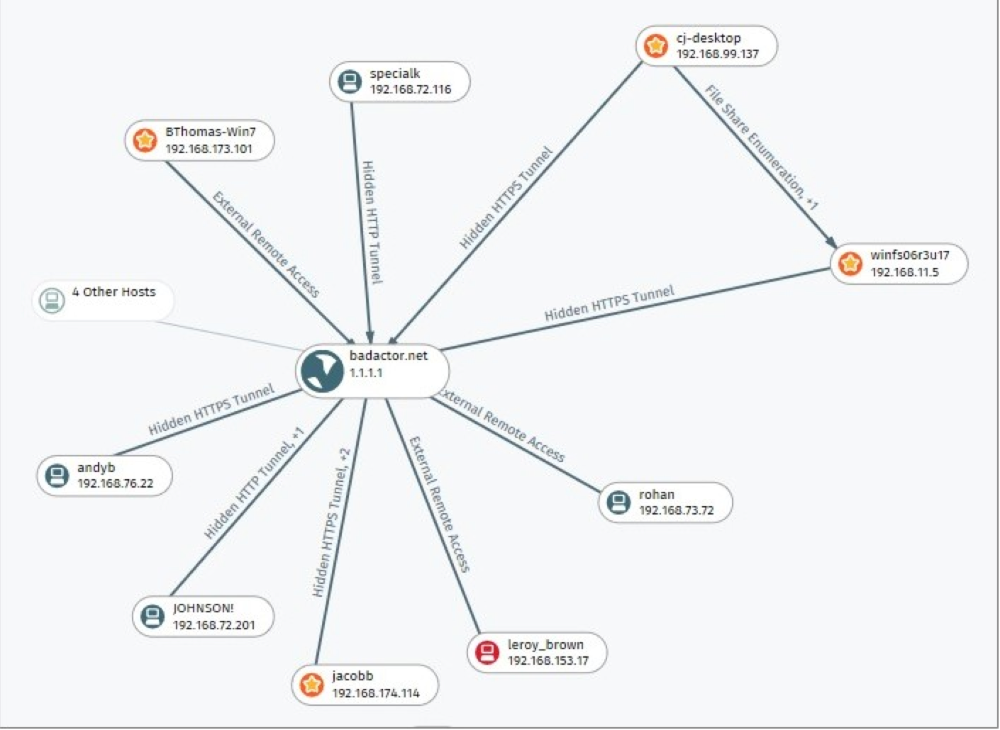
-- Connect the dots of attacker behaviors. Highly complex, multi-stage attacks are difficult to root out. Cognito connects the dots of related attacker behavior detections across all hosts in real time, relieving the burden on security analysts to find these relationships manually. A synthesized view of an attack campaign allows an entire attack to be stopped at the earliest signs of detection.
Cognito integrates threat intelligence and indicators-of-compromise (IoC) feeds. Threat intel detections capture metadata from data packets to protect personal privacy and are correlated with Cognito attacker behavior detection algorithms to amplify the attacker signal and provide the most complete context.
-- Stop in-progress attacks. Tight integration with leading security tools allows customers to build well-coordinated security infrastructures that automatically map active attacks to infected hosts, rank the certainty and severity of threats, and prioritize the threats that pose the highest risk. Cognito works with leading endpoint security, network access control, firewall, SIEM, security orchestration and network visibility products. https://vectra.ai/partners-technology



