Photo Gallery
 |
 |
Contrast Serverless Application Security
Additional Info
| Company | Contrast Security |
| Company size | 100 - 499 employees |
| Website | https://www.contrastsecurity.com/ |
NOMINATION HIGHLIGHTS
Contrast Security’s Contrast Serverless Application Security is a breakthrough application security solution designed specifically for cloud-native and serverless application development that will initially support AWS Lambda. It empowers developers to automatically detect security vulnerabilities directly within serverless environments and validate and prioritize alert test results for remediation. Using context-based static and dynamic engines, Contrast can improve the operational efficiencies of serverless security by 50% while accelerating development release cycles.
Contrast’s solution harnesses the power and data of serverless architectures to map all the resources within the environment, execute static code scans, and simulate tailored dynamic attacks. It automatically validates and prioritizes test results with accuracy that eliminates false positives and alert fatigue that plague traditional application security approaches—with upwards of 85% of alerts being false positives.
Solution features:
Dynamic Environment Scanning. Automatically initiates tailored, dynamic security assessments based on any specific updates introduced to the testing environment in real time. This greatly improves the ease of pentesting versus manual approaches. Dynamic scans are based on the interpretation of OWASP Top Ten benchmarks, including SQL injection, code injection, command injection, and local file inclusion.
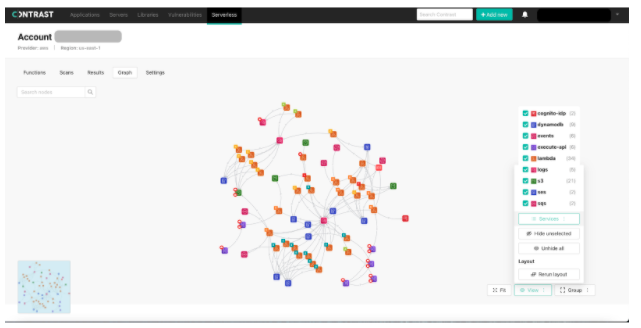
Resource Mapping. Automatically discovers all resources (e.g., S3 bucket, API Gateway, DynamoDB) and their relationships within tested environments in a few short minutes per session. Results are presented using a highly interactive graph which visualizes the entire application. Use the graph to zero-in on key vulnerabilities and understand the ‘blast radius’ of a potential exploit.
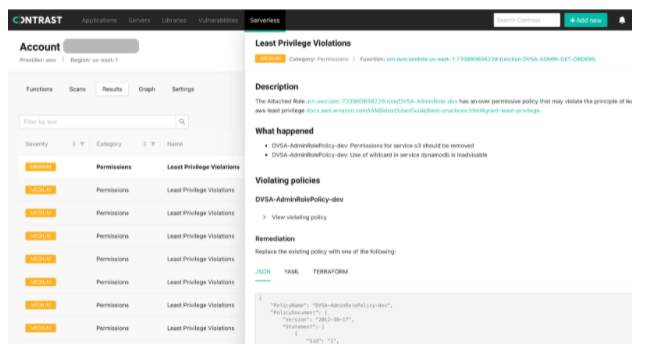
Code Scanning. Automatically executes assessments of relevant code and configuration to discover new vulnerabilities in near real time with recommended context-rich remediation guidance. Vulnerability types covered include:
Least privilege: Identity and access management (IAM) vulnerabilities (over permissive functions) within serverless workload prior to deployment
Software composition analysis (SCA): Analysis of open-source libraries using Contrast’s unique open-source security engine
How we are different
According to Contrast's State of Serverless Application Security Report, serverless computing is the next step in the two-decade-long process of removing friction from the software development life cycle (SDLC) to improve the speed, scalability, and cost efficiency of software development. With serverless computing becoming mainstream during the COVID-19 pandemic, the survey found that more than 70% of respondents report that 6 or more of their development teams now work on serverless applications, and Contrast is seeing customers turn to Contrast Serverless Application Security to help them secure their codes in serverless technologies.
Differentiators of Contrast’s serverless security capabilities include:
The new Contrast Serverless Application Security solution initially supports AWS Lambda deployments and takes just minutes to get up and running. Three-click installation, zero configuration, and automated operations all support developer-friendly deployment.
The complimentary, purpose-built solution for serverless application security ensures that security and development teams get the testing and protection capabilities they need without legacy inefficiencies that delay release cycles. Contrast's solution harnesses the power and data of serverless architectures to map all the resources within the environment, execute static code scans, and simulate tailored dynamic attacks. It automatically validates and prioritizes test results with accuracy that eliminates false positives and alert fatigue that plague traditional application security approaches—with upwards of 85% of alerts turning out to be false positives.
Traditional application security approaches were not built for serverless applications. Contrast Serverless Application Security empower developers to detect and remediate serious security vulnerabilities easily and quickly. This unleashes the full potential of the cloud and serverless while dramatically reducing the risk of vulnerabilities in these environments.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



