Photo Gallery
 |
 |
Core Impact

Additional Info
| Company | Core Security, a HelpSystems Company |
| Company size | 500 - 999 employees |
| Website | http://www.coresecurity.com |
NOMINATION HIGHLIGHTS
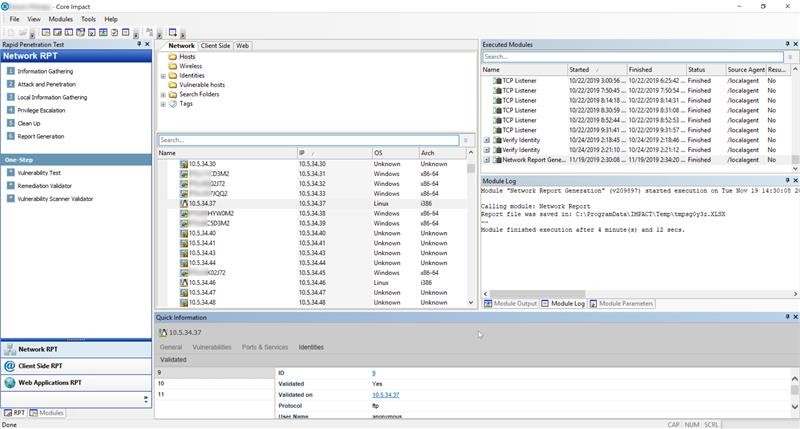
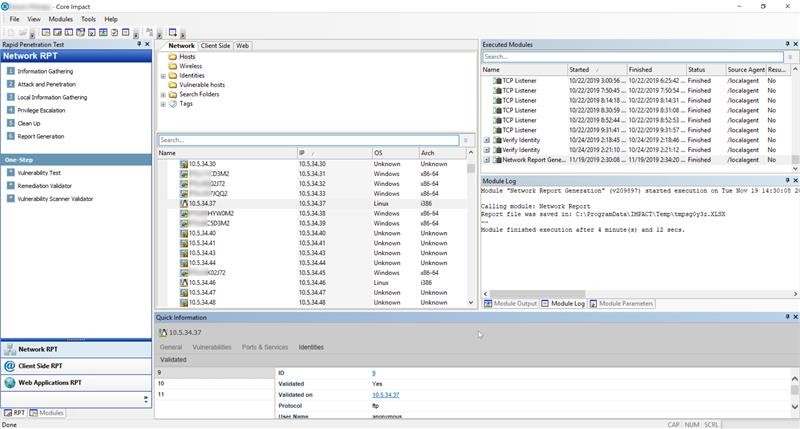
Core Impact is one of the most comprehensive penetration testing solutions on the market that enables security teams to exploit security weaknesses using the same techniques as cyber criminals. It’s the only solution that empowers you to replicate multi-staged attacks that pivot across systems, devices and applications.
Core Impact is designed for both new and advanced penetration testers alike. It simplifies testing for new users by providing intuitive, step-by-step wizards and rapid penetration tests so they can automatically gather the information they need. Meanwhile, advanced users can efficiently execute common tasks, saving time while providing a consistent, repeatable process for testing infrastructure.
Multiple security testers have the capability to interact in the same session, providing a common view of discovered and compromised network targets for optimal collaboration. This allows one penetration tester to pick up where another may have left off to improve efficiency.
Penetration testers can also easily simulate a phishing campaign using Core Impact’s dynamic phishing tools. In additional to identifying who is susceptible to phishing withing the organizations, the tool can be used to harvest credentials for further testing purposes.
How we are different
- Core Impact includes an up-to-date library of commercial-grade exploits to reveal how chains of exploitable vulnerabilities open paths to mission-critical systems and assets.
- Designed for users at every skill level with step-by-step wizards for beginners and automation of common tasks for advanced users to save valuable time.
- Provides multi-vector testing capabilities with the ability to replicate attacks across network infrastructure, endpoints, web, and applications.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



