Photo Gallery
 |

 |
Cyber Defense Labs


Additional Info
| Company size | 23 employees |
| Website | http://www.cyberdefenselabs.com |
NOMINATION HIGHLIGHTS
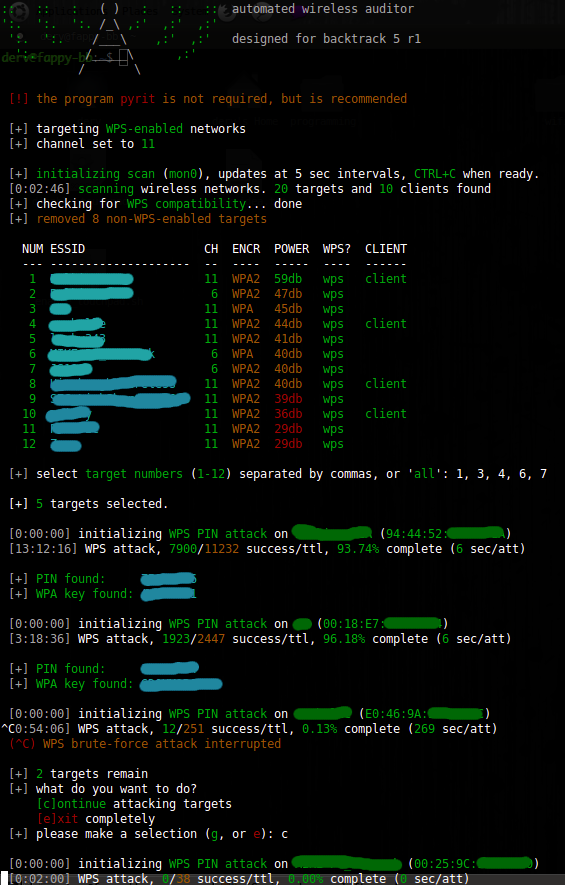
Cyber Defense Labs is a small but fast growing cyber security company. That mixes applied research, penetration testing and educational outreach seamlessly into its offerings. Located on UT Dallas’s campus, CDL is a magnet for the best and brightest form across north Texas. Student an interns help develop new exploits, and automation tools. The research staff teach and or guest lecture at 4 different local colleges and hold a 4 week (160) hour hands on camp during the summer to bring high school student into the field with real world hands on problems. This highly inovative approach to teaching and recruiting keeps a steady supply of the most precious commodity in cyber security, “Trained Creative Problem Solvers”. Students flock to this program from across the country. They are already taking applications for the 4th year of this camp with they say is being prepared by the best and brightest students form its first year. On the applied research side CDL is working in SCADA security, automating forensic processing, and advanced error checking and reporting tools for penitent operations. The Red Team at CDL writes its own exploits and conducts network, wireless, web application, and physical penitents as well as cryptanalysis. CDL is very active with Infragard, the North Texas Crime commission and other local state and national agencies to help handle cyber crime incident snd provide real time treat warning and response. Finally CDL works to provide a roadmap to novel the issues they find during a Vulnerability assessment or a penetration test. Their work is not over when the vulnerability report is written,
How we are different
All the services and law enforcement connections you would expect from a company many times its size.
All the advanced research,development and next generations you would expect from a first class university.
The personal touch and attention to detail you would expect if you hired a full time cyber specialist to solve your problem and train your team.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



