Photo Gallery
 |
 |
CYBERShark

Additional Info
| Company | BlackStratus |
| Company size | 50 employees |
| Website | http://www.blackstratus.com |
NOMINATION HIGHLIGHTS
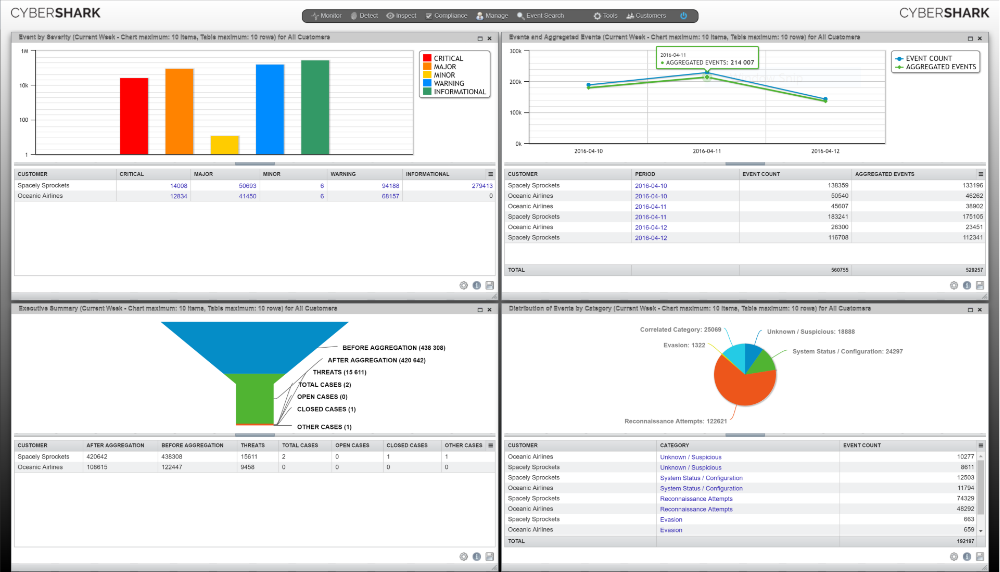
CYBERShark is a white labeled, SaaS-based SIEM service specifically tailored for the SMB market and the MSP community. CYBERShark empowers MSPs to build a sustainable managed services business without the need to invest in expensive infrastructure, buy expensive hardware appliances and recruit expensive security analysts. By simply sending their end-customer event log data to the advanced CYBERShark cloud, MSPs receive a white-labeled portal view of their customers’ compliance reports and security posture complete with step-by-step remediation to resolve security incidents and malicious activity. The cost for a small business to use CYBERShark start as low as $300 a month, which is remarkable given the new service is built on the same platform as BlackStratus’ enterprise SIEM product which is used by some of the largest global brands and government agencies.
CYBERShark Features
•Advanced architecture designed to cover complex regulatory compliance, business continuity and risk management needs
•Multi-tenancy support silos customer accounts and files, protecting privacy and data integrity
•Real-time attack visualization identifies zero-day attacks based on rules-based, vulnerability, statistical, and historical correlations
•Vulnerability correlation integrates data from detection systems, eliminating false positives and freeing up your team to focus on actual threats
•Unparalleled visibility in distributed networks to correlate activity in individual customer environments, identifying hidden threats, suspicious trends and other potentially dangerous behavior
•Sophisticated reporting tools for ISO, PCI, HIPAA, SOX and other compliance standards
How we are different
-CYBERShark allows small businesses an easily affordable enterprise-level SIEM service, which includes free of charge the constant monitoring of a firm’s network by BlackStratus’ Security Operations Center
-CYBERShark is the first white-label, SaaS-based SIEM that allows MSPs to integrate the service under their brand
-CYBERShark is one of the only SIEM services in the market that shares the same foundation as a proven enterprise-level SIEM product that has been used by thousands of large companies and government entities for nearly two decades

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



