Photo Gallery

|

|
Cycode

Additional Info
| Company | Cycode |
| Company size | 50 - 99 employees |
| Website | http://www.cycode.com |
NOMINATION HIGHLIGHTS
Software supply chain attacks like Solarwinds, Kaseya, and Codecov are becoming more prevalent as attackers shift their focus from production applications to the software delivery pipelines that build those applications. This is happening because modern development approaches have outpaced application security and DevSecOps capabilities. Software supply chain attacks can be caused by code leaks, hardcoded secrets, poor coding practices, misconfiguration, code tampering or even breaching the DevOps tools and infrastructure themselves. Moreover, once the software delivery lifecycle (SDLC) is compromised by way of any entry point, attackers can easily move between the tools and phases of the SDLC due to the automation and orchestration inherent to DevOps. Unfortunately, security teams are relegated to point products which exist within the silo of a single phase of the SDLC, causing a lack of context, blind spots, and false positives. Finally, there is a lack of security tools that prevent DevOps tooling like SCMs, build tools, container registries and cloud providers from being used as attack vectors. This creates a perfect storm for attackers and a headache for development and security teams.
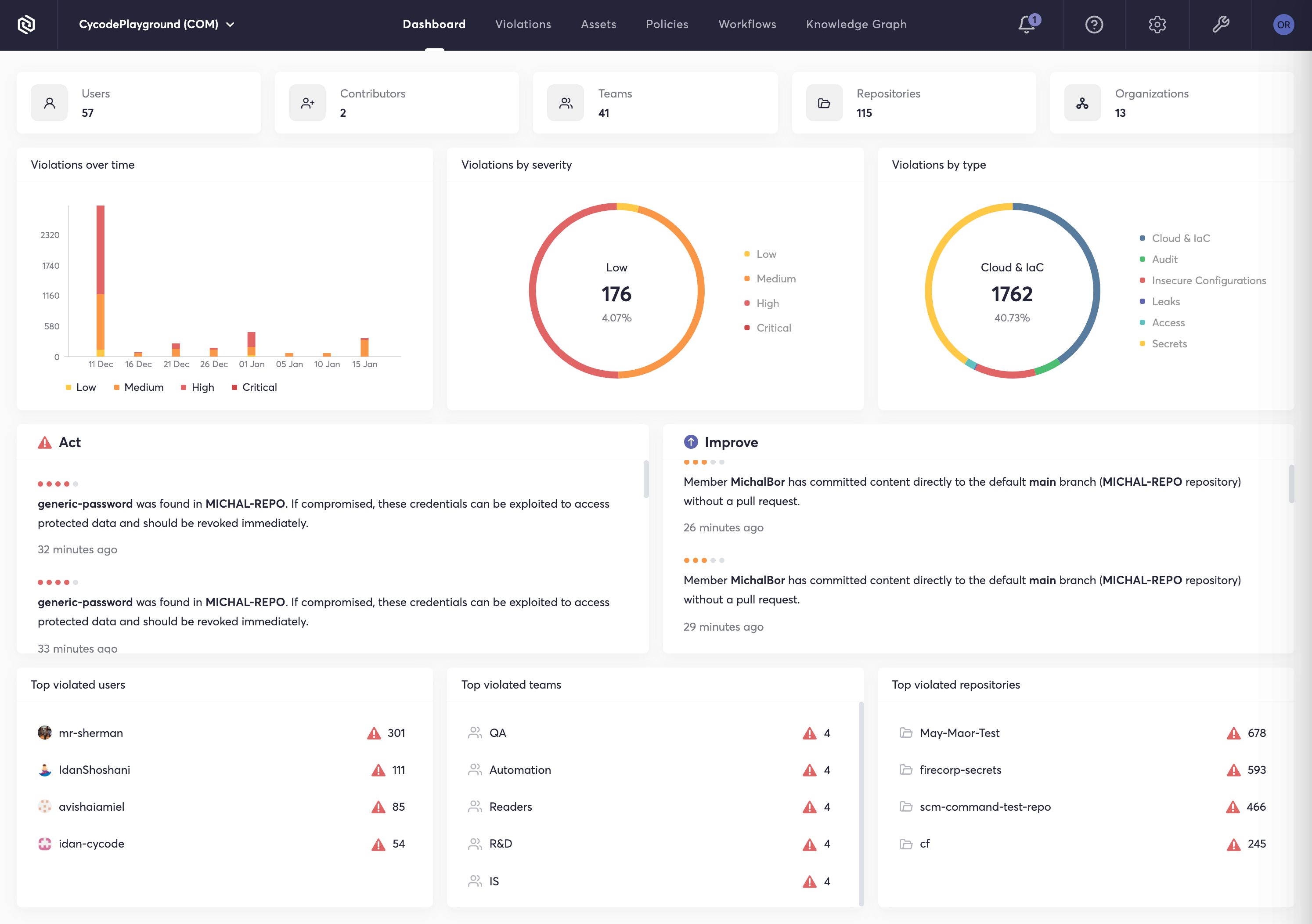
Cycode attacks these issues head on with a complete software supply chain security solution that provides visibility, security, and integrity across all phases of the SDLC. Cycode integrates with DevOps tools and infrastructure providers, hardens their security postures by implementing consistent governance, and reduces the risk of breaches with a series of scanning engines that look for issues like hardcoded secrets, infrastructure as code misconfigurations, code leaks and more. Cycode’s knowledge graph tracks code integrity, user activity, and events across the SDLC to prioritize risk, find anomalies, and prevent code tampering. Finally Cycode helps efficiently remediate any security issues it discovers by way of developer workflow integration and auto-generated code fixes and suggestions.
How we are different
Cycode’s approach to SDLC security is unique in that:
Cycode enables customers to implement consistent, effective security policies across their teams and tools to harden the SDLC and DevOps tooling against attack. This includes things like access controls, enforcing least privilege, branch protection rules, and build rules. This is a challenge because organizations often have multiple engineering and DevOps teams, each of which pick their own tools (SCMs, build tools, registries cloud providers, etc.). Those tools are configured by default for efficiency, not security. Which means each tool must be individually audited and configured according to security best practices. The same is true for user access privileges, and in SCMs that is often done on a repo by repo basis. This is an incredibly large and time-consuming job, but one that’s essential to the security of your software delivery pipeline. Cycode is unique in its ability to review and implement security and governance best practices across DevOps tools and infrastructure.
Cycode's Knowledge Graph breaks down AppSec's silos to increase accuracy - Our system is built on a graph database that maps out relationships between tools, user behavior, configurations, policies, violations, vulnerabilities and more. This graph database serves as a platform upon which our product is built; one which can correlate between tools and phases of the SDLC. This has many applications within a security program including compliance, code tampering, anomaly detection, breach path analysis, prioritization and more.
Cycode takes a comprehensive, holistic approach to securing software delivery pipelines. The Cycode platform provides a series of complementary security techniques and approaches (code tampering detection, hardcoded secret detection, Infrastructure as code security, code leakage detection, and security and governance) that address the problem of software supply chain or SDLC security from multiple angles, thus providing better results than could be achieved using individual point products.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

