Photo Gallery
 |
 |
CylancePROTECT
Additional Info
| Company | Cylance |
| Company size | 500 - 999 employees |
| Website | https://www.cylance.com/en-us/index.html |
NOMINATION HIGHLIGHTS
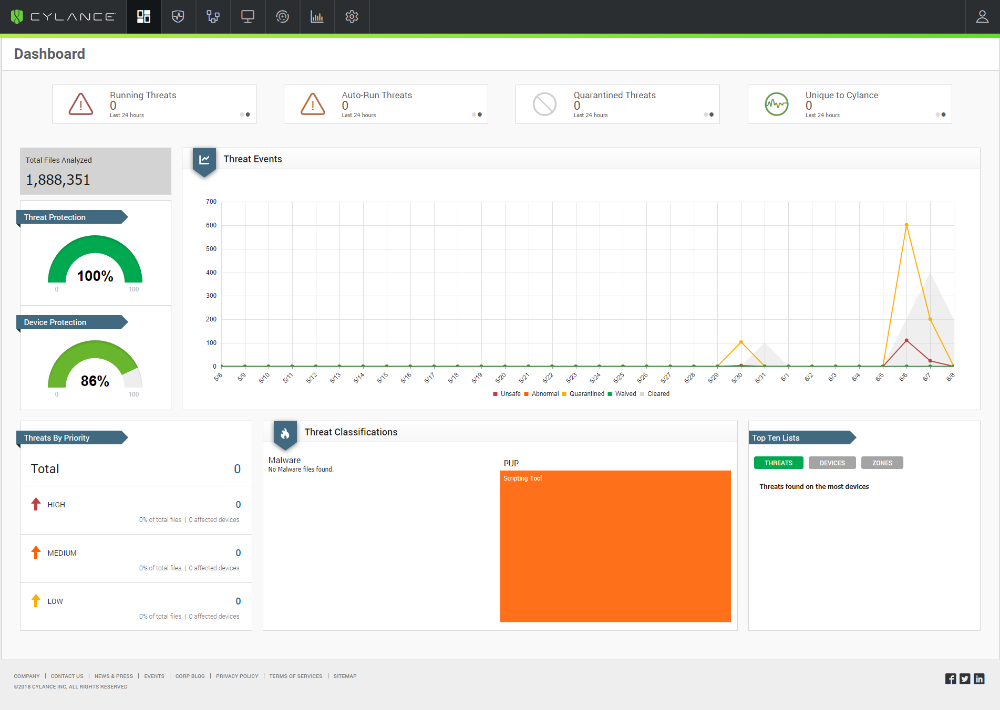
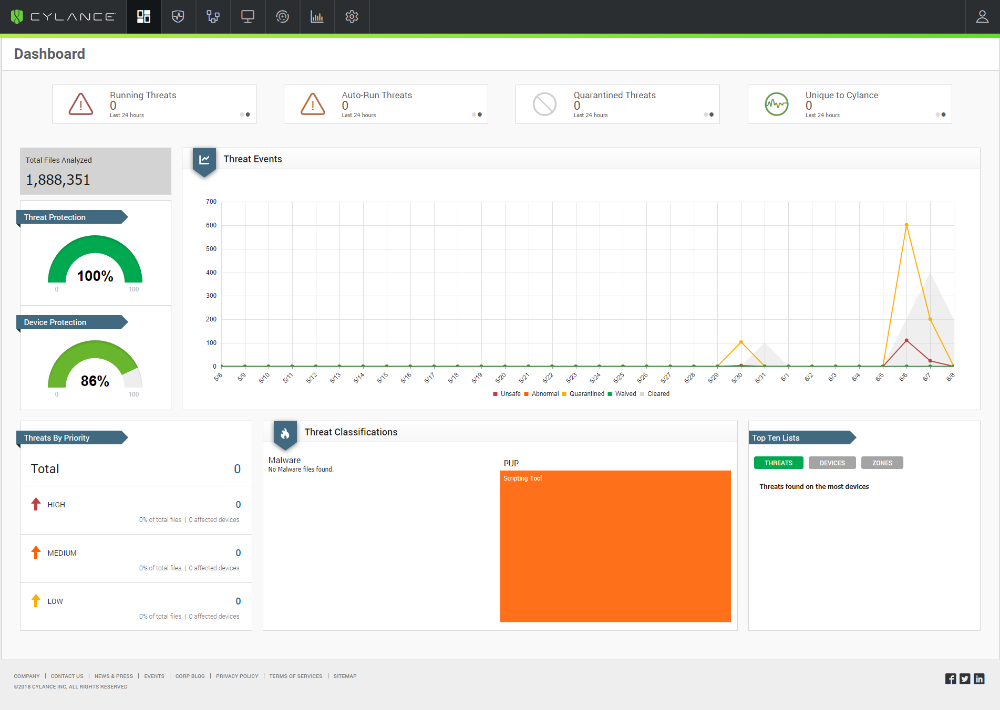
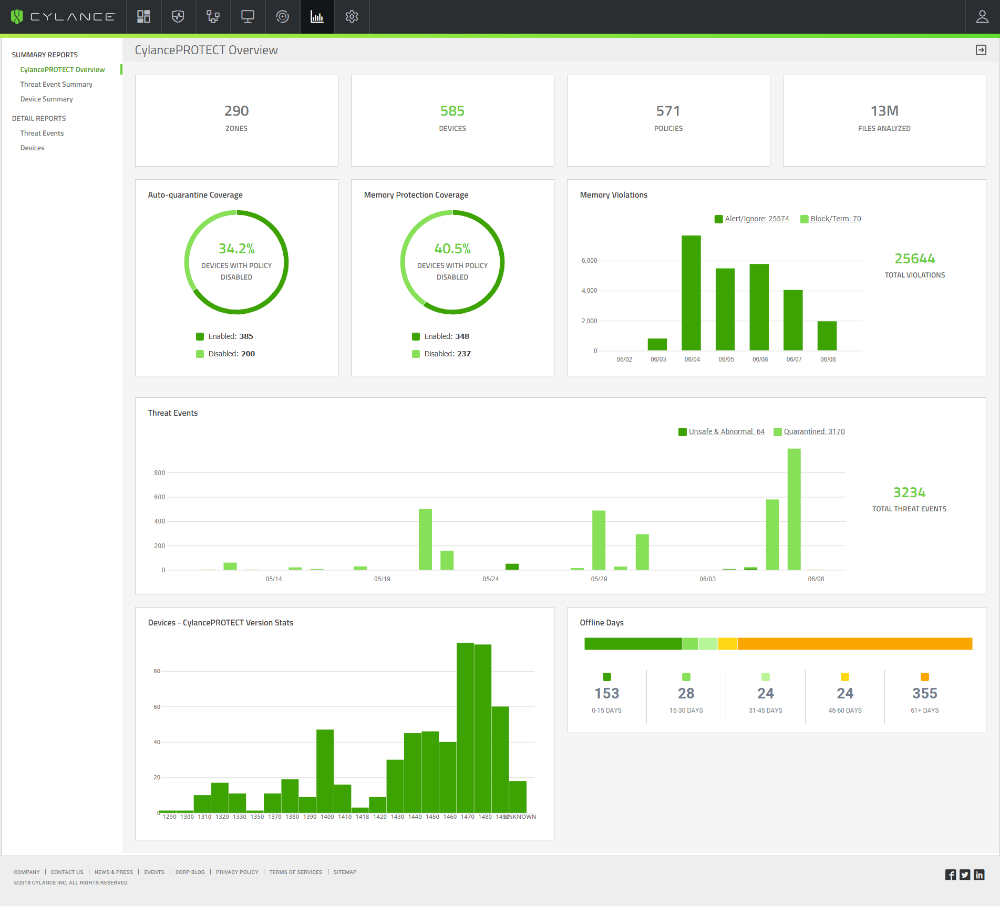
Unlike traditional endpoint security products that rely on signatures to detect threats, CylancePROTECT delivers protection against common threats such as malware, ransomware, fileless malware, malicious scripts and weaponized docs without the use of signatures or the need to stream data to the cloud. This approach eliminates the need for IT administrators to spend hours pushing out new signatures and software updates, freeing them to finally work on other projects that can help the organization grow.
CylancePROTECT offers something that no other security solution on the market can: zero-day payload prevention. Cylance trains its AI model against billions of files, good and bad, so that it learns to autonomously convict, or not convict files, pre-execution. The result of this massive, ongoing training effort is a predictive AI model that can block malware that has never been seen in the wild.
Cylance puts this predictive power to use in a local version of the cloud-trained AI model that gets deployed on the endpoint. Once deployed, the endpoint is protected from future attacks, even attacks that have yet to be conceived by attackers, without the use of signatures or any connection to the cloud.
In real time, this model is put into action each time an executable attempts to launch on the endpoint. The model determines the nature of the executable in just milliseconds. If good, the model allows the application to run, but if malicious, the application is blocked.
Key features of CylancePROTECT include:
● AI Driven Malware Prevention (execution control)
● USB Device Usage Policy Enforcement (device control)
● Script Management (script control)
● Memory Exploit Prevention (memory protection)
● Application Control for Fixed-Function Devices (app control)
● Zero-day Payload Prevention
How we are different
●Predicts what zero-day threats will look like, even before they exist, using zero-day payload prevention to enable immediate detection and prevention when the attacker attempts to deploy their attack, thus ensuring it’s business as usual for Cylance customers while others are scrambling to recover from a widespread attack.
●Provides a single endpoint agent that delivers continuous malware prevention, device and script control, application control and memory exploitation protection without the use of signatures or frequent updates to the product, freeing up the analyst to address other business needs.
●Delivers whisper-quiet prevention with minimal impact on the endpoint, enabling users to be as productive as possible with superior protection.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



