Photo Gallery
 |

 |
Cymatic
Additional Info
| Company size | 10 - 49 employees |
| World Region | North America |
| Website | https://cymatic.io/ |
NOMINATION HIGHLIGHTS
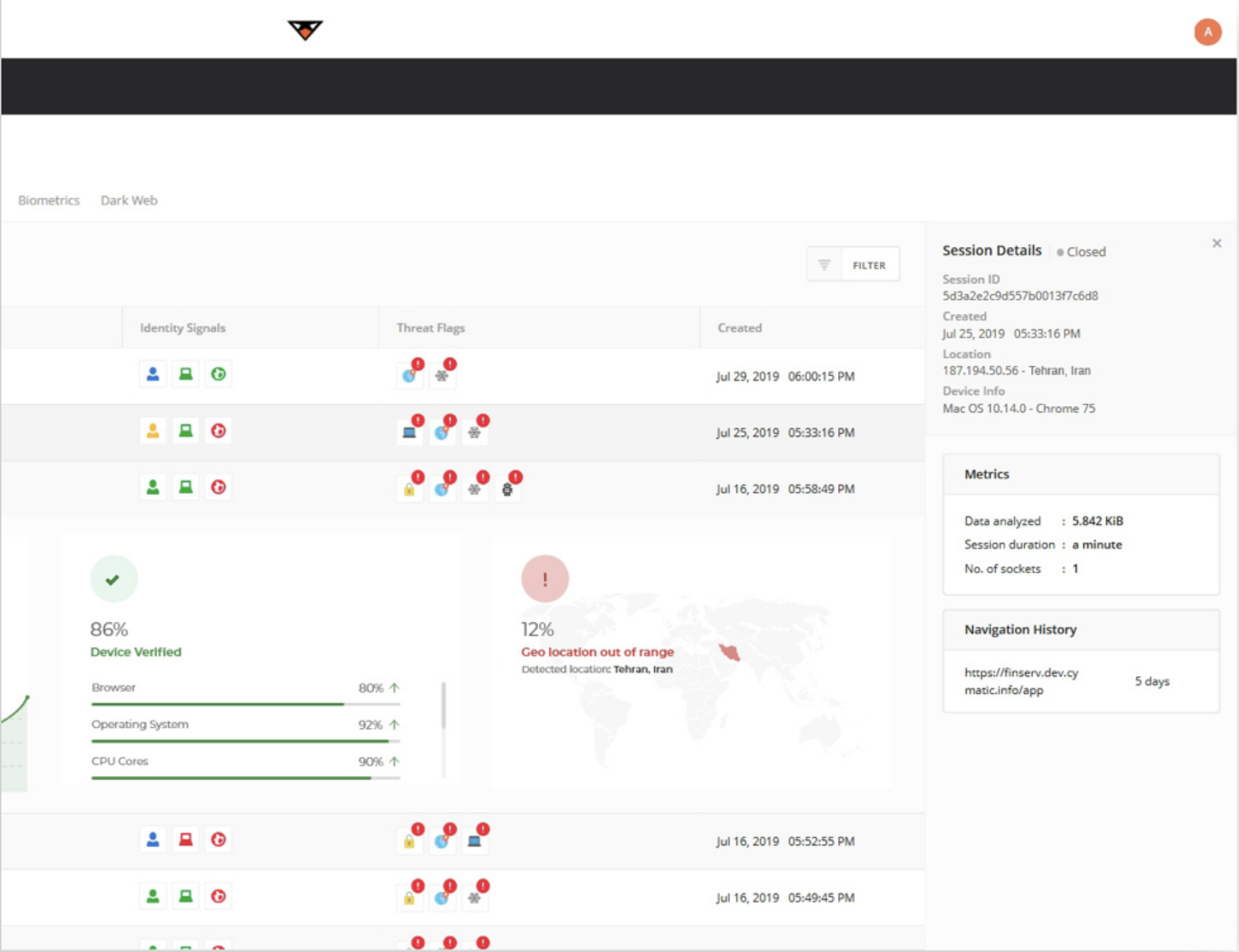
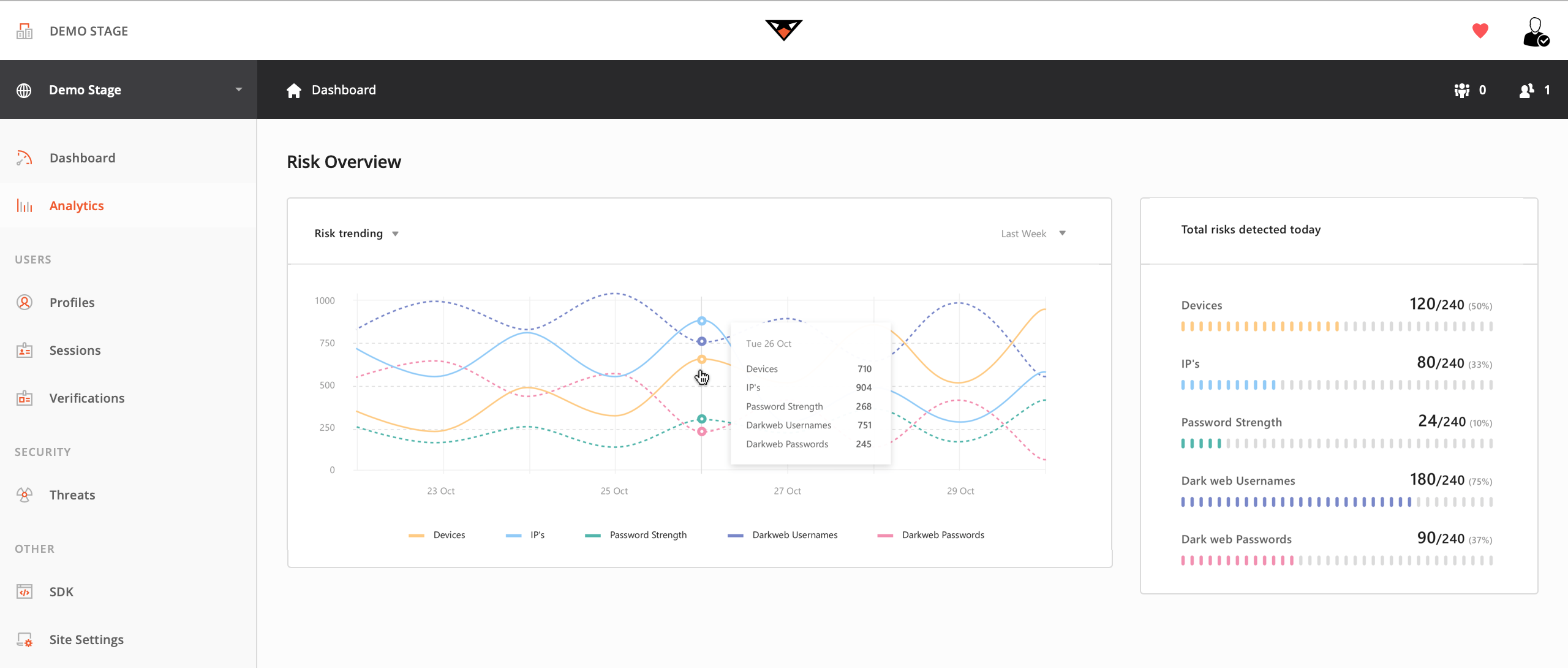
Cymatic has revolutionized the way we defend web applications by offering the only unified WAF that deploys at the client through a simple line of JavaScript without agents or proxies to provide improved efficacy and threat mitigation in addition to ease and speed of deployment. Cymatic’s groundbreaking client-side platform delivers first-look, first-strike capability that is earliest in the kill chain—a fundamental shift in traditional approaches to security. By moving protection from the network side to the client, Cymatic defends against today’s most sophisticated client-based attacks. It provides universal in-session visibility and control to reduce risk across web applications, networks, and users while decreasing network traffic loads and eliminating user friction.
Instead of just protecting network-based threats like traditional WAFs, Cymatic uses sophisticated artificial intelligence and machine-learning algorithms to identify page mutations and user anomalies. The platform protects against user-derived and device-based threats such as poor credential hygiene, dark web vulnerabilities, and potentially risky devices. It is invisible and frictionless to users, deploys in mere minutes, and has immediate time-to-value.
Cymatic’s advanced cloud-based microservices and real-time message-bus architecture offer unparalleled scale to provide the resilience necessary to validate and process the millions of users and transactions that touch web properties every second. The platform is engineered to work across all web applications regardless of operating system, browser, or device. It eliminates the OWASP top 10, bots, CAPTCHAs, dark web threats, forced MFA, shared accounts, IP threats, device vulnerabilities, and other cloud-based threats with no erosion of the user experience.
How we are different
1) Traditional WAFs are plagued with problems resulting from being designed as a network appliance and suited to earlier web applications that did their processing on the server-side; next-generation WAFs, designed to protect data in the cloud in addition to server-side, also fall short because they require the installation of agents and the integration of many additional siloed, independent products (such as bot mitigation, geolocation, dark web scans, and more), adding significant cost and complexity to the security environment.
2) Today’s threats are client-side, making it difficult for existing WAFs to see and protect against user- and session-level threats. This inability to defend against the newest and most widespread attack vectors--enabled through applications processing at the client and in the browser--leaves organizations more susceptible to a breach. Furthermore, traditional WAF deployments are slow, expensive, and late in the kill chain, all of which have the additional downside of increasing user friction, particularly when coupled with the siloed nature of ancillary products and services.
3) Cymatic does for WAFs what Apple did for smartphones--it reimagines and ultimately rearchitects the way we think of and use WAFs to deliver better overall security. Cymatic eliminates the weaknesses of traditional and cloud-native WAFs by moving the visibility and protection to users and devices where threats originate. It combines the benefits of WAF solutions with intelligence from user- and device- recognition to combat web application threats without agents, proxies, network changes, signatures, or cookies. Regardless of whether threats come from APTs, organized crime, bad actors, or unsuspecting users, Cymatic can see into each session to provide the highest levels of insight and protection.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



