Photo Gallery
 |
 |
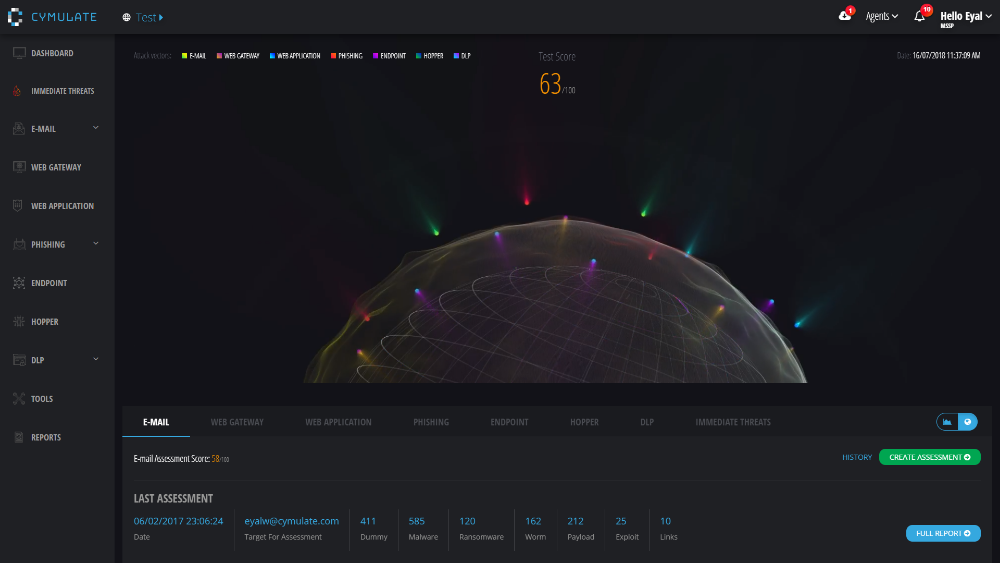
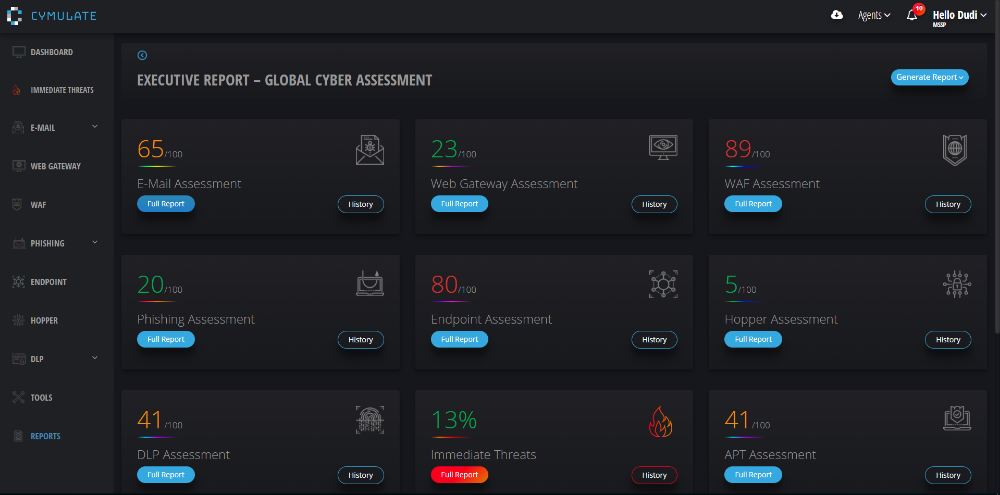
Cymulate Breach & Attack Simulation Platform
Additional Info
| Company | Cymulate |
| Company size | 10 - 49 employees |
| Website | http://www.cymulate.com |
NOMINATION HIGHLIGHTS
Cymulate Breach & Attack Simulation platform allows organizations to assess their true readiness to handle cybersecurity threats effectively by simulating the myriad of tactics and strategies used by hackers to attack network and endpoint security infrastructures.
Fully-automated and diversified attacks allow for complete security testing anytime, providing organizations with a better understanding of their security posture while allowing them to improve it continuously.
Cymulate’s platform comprehensively exercises the company’s defenses with the industry’s widest range of attack vectors, providing an Advanced Persistent Threat (APT) simulation of your security posture at all times. It tests the network’s ability to cope with pre-exploitation-stage threats in Email, Web-Gateway and Web application. It analyzes the ability to respond to real incidents with our post-exploitation modules like the Lateral movement, Endpoint, and Data Exfiltration. In the end, it Assesses and improves awareness among employees against phishing, ransomware and other attacks.
The platform helps you gain a clear picture of the company’s vulnerabilities from every point of exposure and learn what will really happen If you are attacked.
How we are different
1. Cymulate validates a wider range of attack vectors: Email, Web-Gateway, Lateral Movement, Data exfiltration, Human, Web Application, Endpoint and APT.
2. Cymulate platform is the easiest to deploy, allows you to perform your first assessment within minutes and does not require complicated implementation or hardware.
2. Cymulate also validates the effectiveness of the organization security controls.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



