Photo Gallery
|
|
D3 Automation and Orchestration Platform
Additional Info
| Company | D3 Security |
| Company size | 50 - 99 employees |
| Website | https://d3security.com |
NOMINATION HIGHLIGHTS
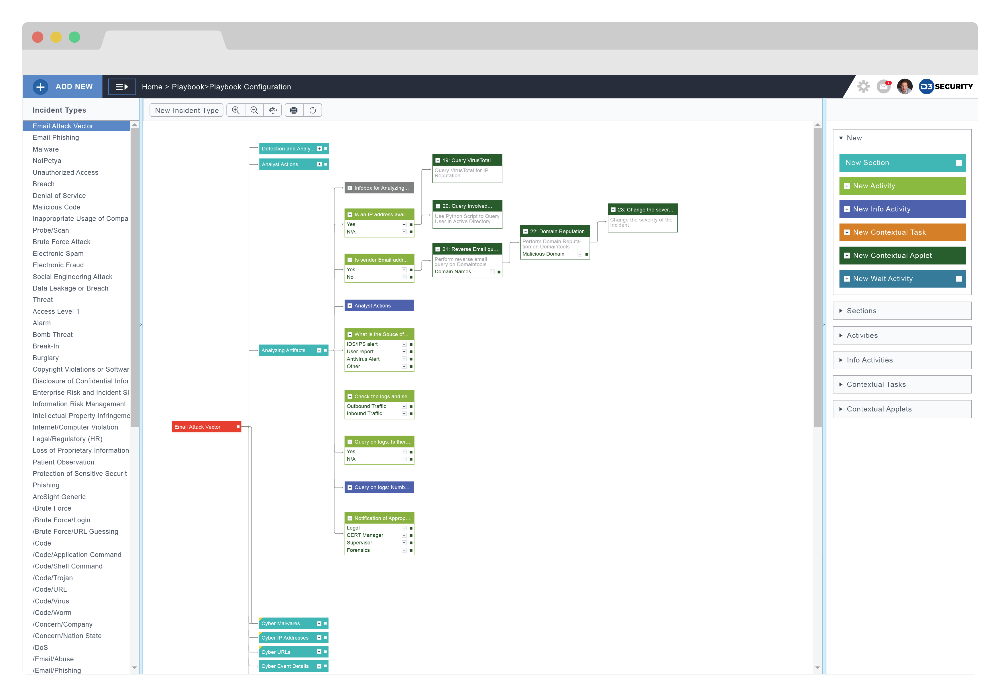
Incident response and SOC teams can no longer afford to manually coordinate across workflow and reporting silos. Short on resources and facing sophisticated attackers, security teams need advanced technology to win the fight. Equipped with the D3 Security Automation and Orchestration Platform, organizations can manage every alert and fulfill compliance obligations, while drastically reducing incident response times and ensuring SOC analysts work on the highest-impact tasks, with the benefit of full contextual awareness. Previously, iIdentifying a threat, assigning tasks, gathering intelligence, and taking action used tocould take hours—but D3 automates it all, by enriching workflows with threat intelligence, reputational data, and artificial intelligence.
D3 integrates with an organization’s security stack to enable a powerful incident response hub. Playbooks offer repeatable incident-handling procedures and efficient workflows, while bi-directional SIEM integration, dynamic task orchestration, and security automation speed up all phases of the incident management lifecycle.
The D3 Automation and Orchestration Platform automatically enriches incidents with contextual data from domain, reputation, malware, endpoint, and threat intelligence. Incidents are triaged rapidly and have associated risk scoring, which forces serious events to flow up to Level II and III analysts, while likely false positives are handled via automation or are sent to the bottom of the queue.
The artificial intelligence (AI) built into D3 transforms incident data and prior responses into a proactive and dynamic security posture. With machine learning and AI-driven response, security teams can automate triage and prioritization, while reducing false positives by up to 91%.
How we are different
- Fully Configurable Automation - D3 is the only fully configurable platform on the market, and the automation controls are no exception. D3 offers full automation, which allows the closing of ports, killing of processes, and blocking of malicious IPs, files, or users. Human-guided, or partial, automation is also supported, placing a human supervisor in the loop to approve some, or all, automation actions. Using D3’s Visual Playbook Editor, analysts can modify workflows and add automations at any point within the incident response, including on-the-fly, which is critical for zero-day attacks.
- Global Threat Feed Integration - D3 integrates with global threat intelligence feeds, including leading threat intelligence platforms like HPE Threat Central, FireEye iSIGHT, and IBM X-Force. With D3’s automation, the user receives all the relevant context that these feeds provide, without having to step outside of their normal work flow. Reputational data from sources like VirusTotal, DomainTools and MaxMind are automatically gathered, and presented to analysts within the incident record, saving more valuable time.
- Helps Inform Analyst Decisions - Most automation platforms offer some information gathering, and even some basic actions, but no other vendor offers what D3 does to help inform analysts’ decisions. D3 creates a false positive probability score for each new incident, which can be used to assign the incident an appropriate place in an analyst’s queue. If the false positive probability is high enough, the incident can even be resolved automatically without the analyst even needing to see it.


