Photo Gallery

|


|
Endpoint Protector

Additional Info
| Company | CoSoSys |
| Company size | 50 - 99 employees |
| Website | https://www.endpointprotector.com/ |
NOMINATION HIGHLIGHTS
Endpoint Protector is an all-in-one Data Loss Prevention (DLP) solution for Windows, macOS, and Linux that puts an end to data leaks protects from data theft and offers seamless control of portable storage devices. With its modern intuitive interface and its smooth integration as Virtual or Hardware Appliance, Endpoint Protector is easy to install and does not require advanced technical knowledge to run, making it the most accessible and user-friendly solution on the market.
It features five specialized modules which clients can pick and choose from based on their needs:
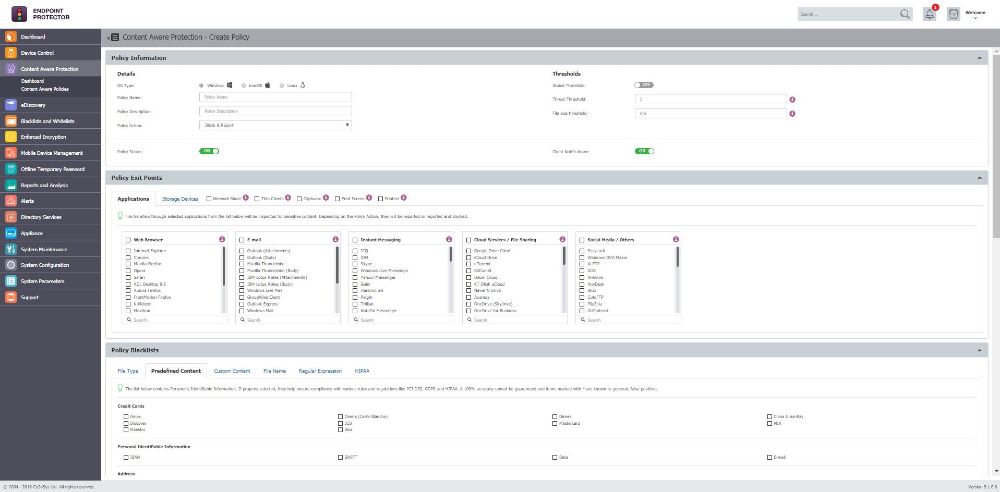
Content Aware Protection allows companies to decide which sensitive data can leave computers by creating policies based on predefined content or compliance regulations such as GDPR or HIPAA. It also logs and reports transfers of important documents.
Device Control is the most granular solution of its kind on the market, allowing administrators to block or limit the use of portable storage devices based on criteria such as device type or serial number as well as based on time or network policies.
Enforced Encryption automatically encrypts any USB devices connected to network endpoints, ensuring data can only be saved on encrypted devices.
eDiscovery offers the possibility to scan sensitive data at rest stored on employees’ endpoints based on specific file types, predefined content, Regular Expressions, GDPR or HIPAA protected content and more. Based on the scan results, remediation actions can be taken such as encrypting or deleting data.
Mobile Device Management provides enhanced control of Android and iOS mobile device fleets and macOS devices through strong security policies, monitoring and tracking capabilities and asset management.
How we are different
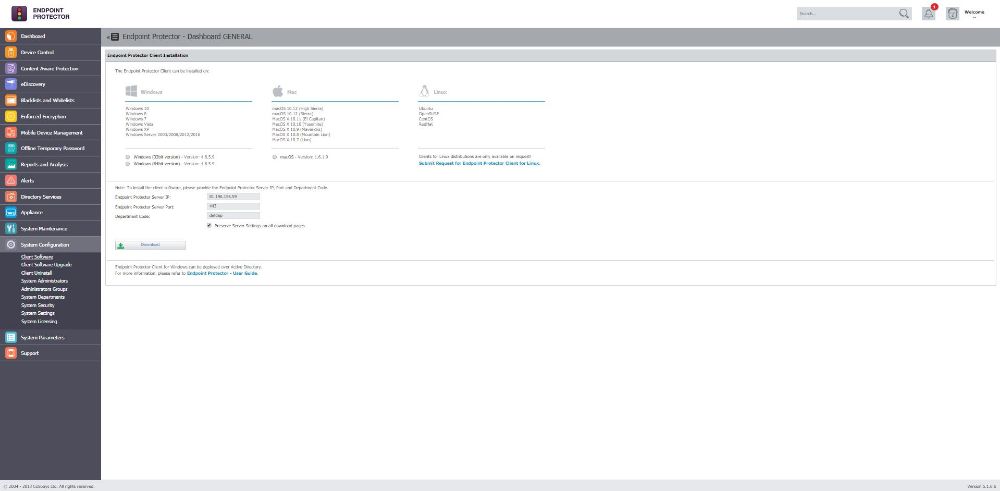
• Endpoint Protector provides Data Loss Prevention not just for Windows, but also macOS and Linux, making it the go-to solution for companies running hybrid OS networks. We are pioneers in the implementation of DLP for macOS and Linux, covering Mac OS X 10.4+ and several Linux distributions – Ubuntu, openSUSE, RedHat and more. Our cross-platform coverage extends to all Endpoint Protector modules including USB Enforced Encryption, enabling a seamless management of all endpoints regardless of their operating system, all from a single dashboard.
• We offer diverse implementation formats to meet the needs of all organizational infrastructures. Endpoint Protector can come as a Virtual Appliance compatible with popular virtualization tools, as an easy to use Hardware Appliance preinstalled with a variety of models based on clients’ needs or as an EC2 Instance on Amazon Web Services. These three optimized implementation methods greatly reduce the time it takes new clients to set up our Data Loss Prevention software and makes it an attractive product for companies worried about the difficulties they might encounter while adopting a DLP solution.
• Our motto at CoSoSys is that clients will have Endpoint Protector up and running in 30 minutes and with its intuitive, user-friendly interface, its flexible policy management, and its carefree installation, it’s easy to see why it’s become one of our biggest selling points. Our Data Loss Prevention solution also offers a short learning curve and can be managed even by non-specialized personnel so there is no need for companies to spend money on additional trainings for staff, helping to reduce the cost and hassle of transitioning to a more secure work environment.


