Photo Gallery
 |

 |
Endpoint Protector 4


Additional Info
| Company | CoSoSys |
| Company size | 60 employees |
| Website | http://endpointprotector.com/ |
NOMINATION HIGHLIGHTS
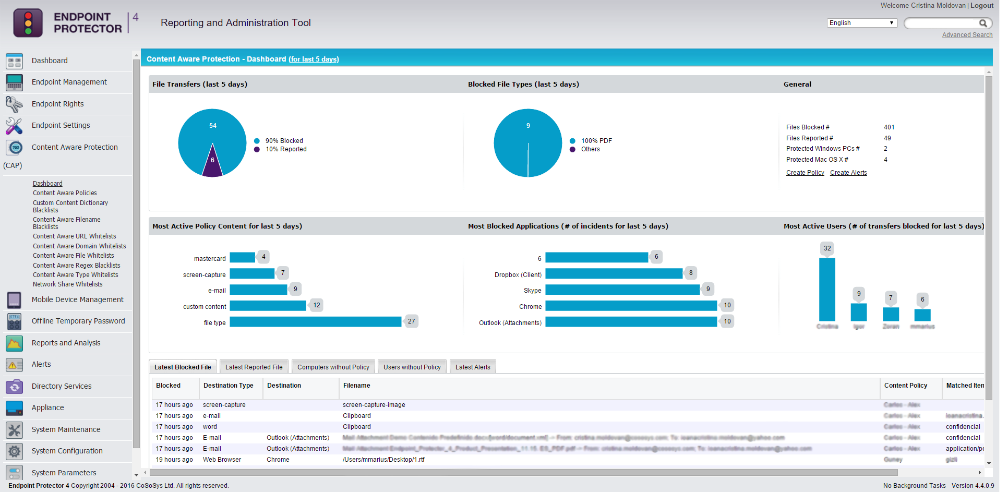
Endpoint Protector 4 Data Loss Prevention (DLP) for Windows, Mac OS X and Linux addresses top business security concerns related to data security, including controlling the use of portable storage devices, enforcing encryption and filtering data transfers through the most common exit channels.
The content-aware DLP features allow organizations to create policies based on file type, predefined content and keywords, as well as monitor and block unauthorized data transfers, including computers outside the network and not connected to the server. For both situations, when data transfers are blocked or allowed but monitored, detailed tracking logs are available. This tracking provides valuable information and a document copy can be downloaded for audit. The product also scans data transfers to portable storage devices, or blocks the use of these devices as required. Additionally, it enforces encryption on removable USB devices with EasyLock, ensuring documents can only be saved on encrypted devices.
How we are different
• One of our main differentiators is our focus on mixed networks, protecting organizations’ confidential data in Mac OS X, Windows and Linux environments, with DLP for Linux being available since January 2016 in Private Beta. In 2013, Endpoint Protector 4 was the first solution of its kind for Mac OS X. Since adding this capability, our customer base in this sector has grown rapidly.
• Another key differentiator is the ease of implementation and use. The hardware and virtual appliances come with preinstalled packages and modules, making the server setup extremely easy. The centralized management console is web-based and can be securely accessed from the company network, or from outside the network through VPN or external IP.
• The one click HIPAA and PCI policies make compliance and data security achievable with minimal efforts.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



