Photo Gallery
|


|
Enea Qosmos ixEngine

Additional Info
| Company | Enea |
| Company size | 500 - 999 employees |
| Website | https://www.enea.com/products-services/traffic-intelligence |
NOMINATION HIGHLIGHTS
The increasing use of encryption for malware and other malicious attacks is challenging the effectiveness of cybersecurity products. To solve the problem, there is a need for embedded traffic intelligence that can identify and classify encrypted and evasive traffic.
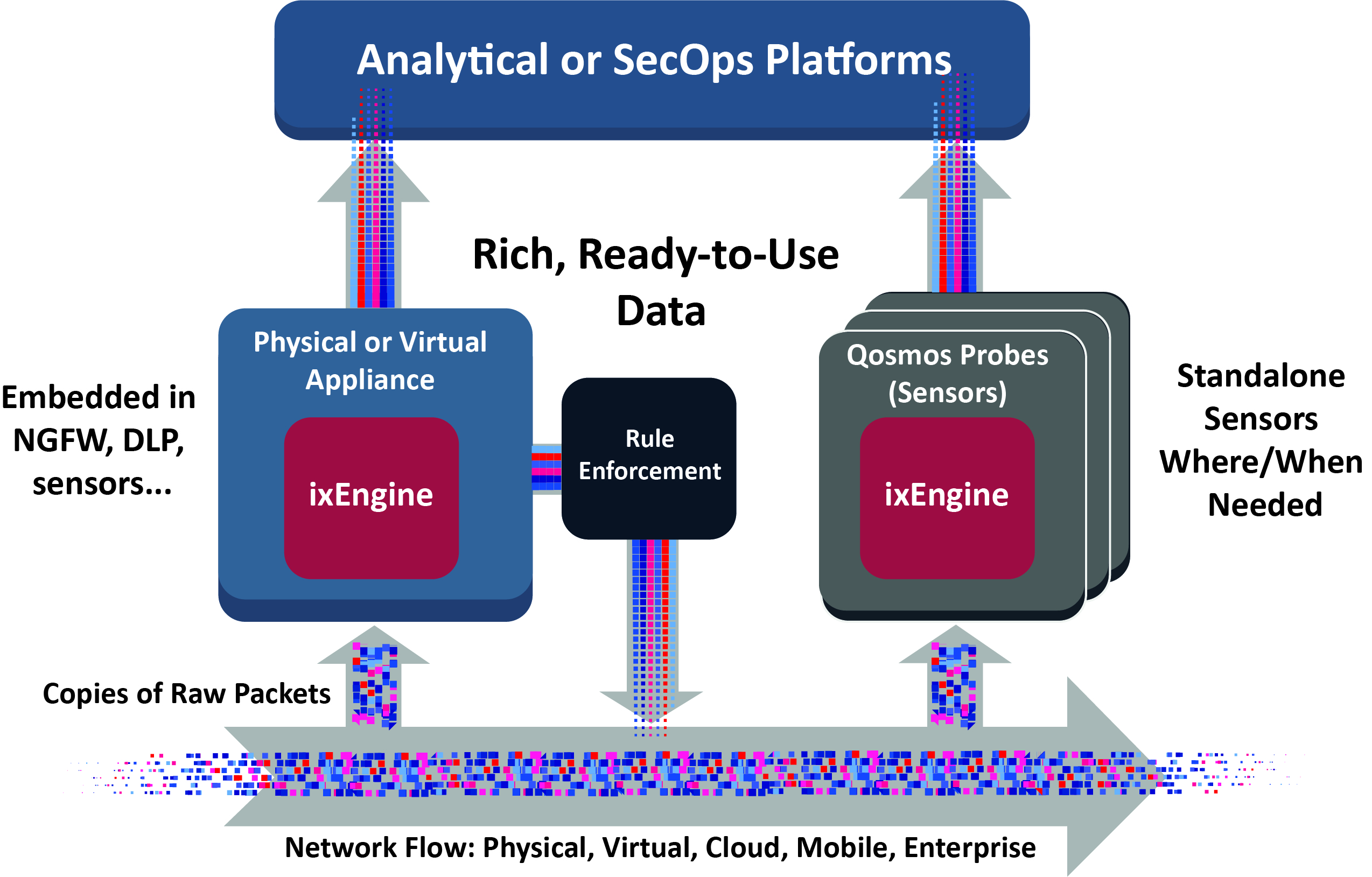
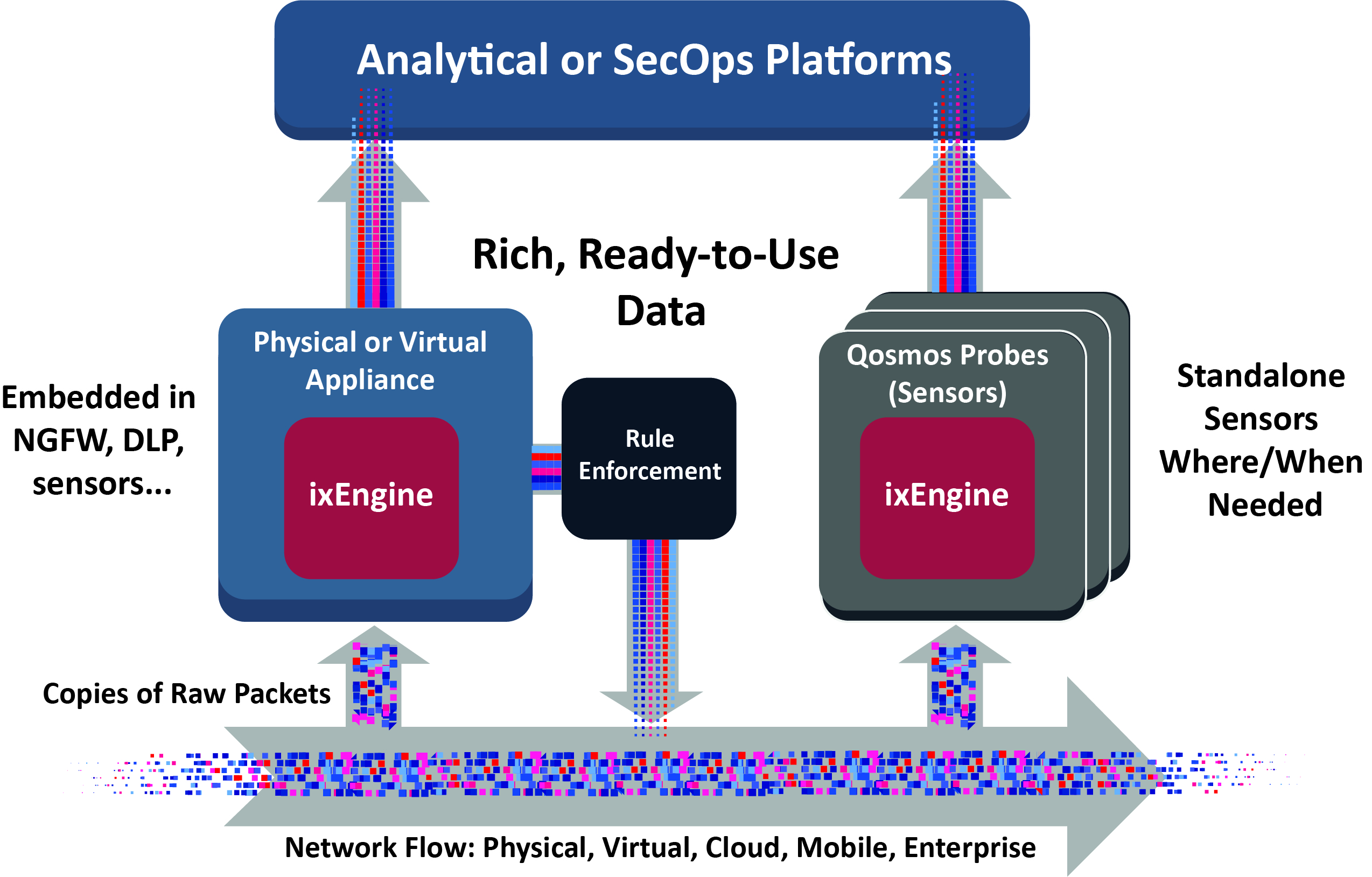
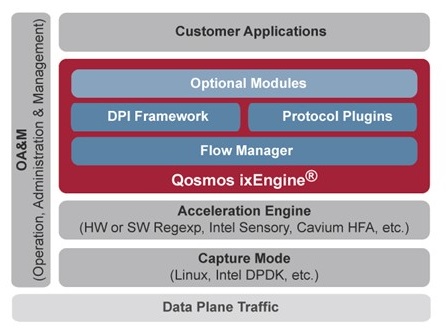
Available as a software development kit for embedded use in cybersecurity products, the Enea Qosmos ixEngine is the most widely deployed traffic classification engine in cybersecurity and networking. It delivers crucial intelligence about encrypted traffic flowing across a network and extracts detailed information about traffic using evasive techniques.
Enea Qosmos Deep Packet Inspection (DPI)-based software analyzes the data packets of traffic flows in real time, up to the application level. It immediately detects suspicious activity and raises the alert to possible threats. This granular visibility enables security solutions to accurately map traffic flows, understand network activity and immediately identify suspicious behavior, raising the speed and effectiveness of malware detection.
To maximize visibility into encrypted traffic, Qosmos ixEngine version 5 uses a combination of advanced techniques:
• Handshake Analysis: Extraction of metadata in handshake messages that remain clear
• Binary Pattern Analysis: Detection & matching of binary patterns against known applications and services
• Statistical Analysis: Packet and flow characteristics using custom models
• Behavioral Analysis: Encrypted session behavior versus characteristic protocol behaviors
• DNS Cache Analysis: Identification of mismatches between cache what the final resolution reveals
For detection and classification of evasive traffic (encrypted or not), the following techniques are used:
• Session Correlation: Regrouping and analysis of flows belonging to the same applications, clients & hosts
• Public IP/Port-Based Classification: Identification of discrepancies between traffic behavior and well-known apps/services, FQDNs, ports & publicly routable IP subnets
• Deep File Inspection: Packet reassembly, file type detection (280+), MIME type and file extension consistency check, and file hash computation
• Cryptocurrency Analysis: Multi-layered analytics to detect and classify cryptocurrencies and mining pools
How we are different
1. Enea Qosmos ixEngine recognizes over 3400 protocols, more than any other DPI library on the market, giving the most detailed view of network traffic available
2. This unparalleled traffic intelligence enhances the ability of endpoint and perimeter defense systems to detect and respond appropriately to encrypted and evasive traffic
3. The visibility also enriches analytics platforms dedicated to detecting and assessing advanced persistent threats that have used evasive techniques to bypass traditional defenses

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

