Photo Gallery

|

|
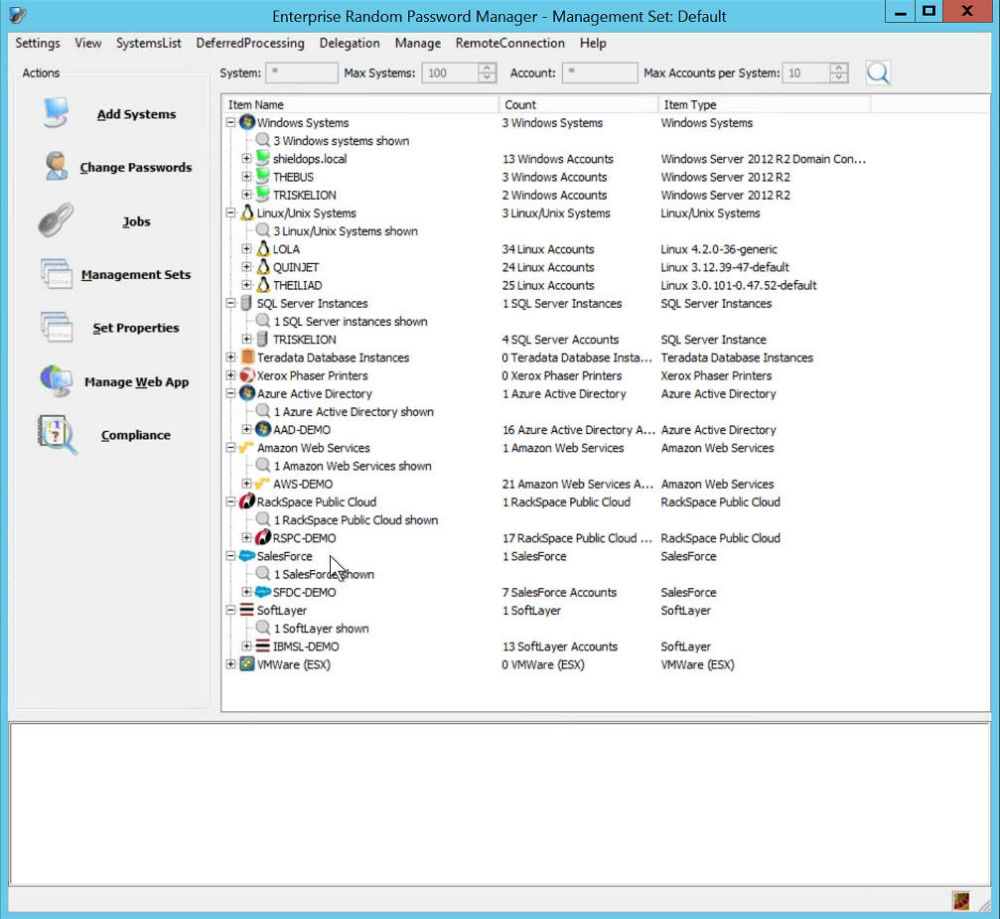
Enterprise Random Password Manager

Additional Info
| Company | Lieberman Software Corporation |
| Company size | 70 employees |
| Website | http://www.liebsoft.com |
NOMINATION HIGHLIGHTS
Perimeter security tools like firewalls and intrusion detection systems react too late to block sophisticated, targeted cyber attacks like advanced persistent threats (APTs). The identity is the new perimeter. Enterprise Random Password Manager (ERPM) arms modern organizations with the proactive cyber defense capabilities they need to cope with the reality of the porous network perimeter.
ERPM is a complete, proactive cyber defense platform that protects organizations against malicious insiders, APTs and other sophisticated cyber attacks – on-premises, in the cloud and in hybrid environments.
The key to stopping cyber attacks with ERPM is its ability to automatically discover and eliminate privileged access security threats before cyber attackers can exploit them. We accomplish this by limiting the value of credentials stolen by criminals, nation-state attackers or malicious insiders.
ERPM eliminates lateral motion when intruders penetrate the network. It does so by time-limiting how long a captured credential can be exploited. Passwords, SSH keys and other credentials are continuously rotated, as frequently as necessary, even every couple of hours – effectively negating zero day attacks. Even if an attacker compromises a machine, those credentials cannot be leveraged to leapfrog from system to system, and anonymously steal sensitive data along the way.
How we are different
ERPM is the only privileged access management solution available on the market today that allows enterprises to manage and secure cloud identities on all of these major platforms: Azure Active Directory, Amazon AWS, IBM SoftLayer, Rackspace and Force.com.
ERPM incorporates continuous, automated discovery and correlation of privileged accounts, while competitors’ solutions require you to maintain complete knowledge of systems lists, credentials and their usage.
According to research published by IDC, we have “the largest verified deployment of a password manager/vault, consisting of hundreds of thousands of machines for privileged access management.”



