Photo Gallery
|
Ericom Shield
Additional Info
| Company | Ericom Software |
| Company size | 100 - 499 employees |
| Website | http://www.ericom.com |
NOMINATION HIGHLIGHTS
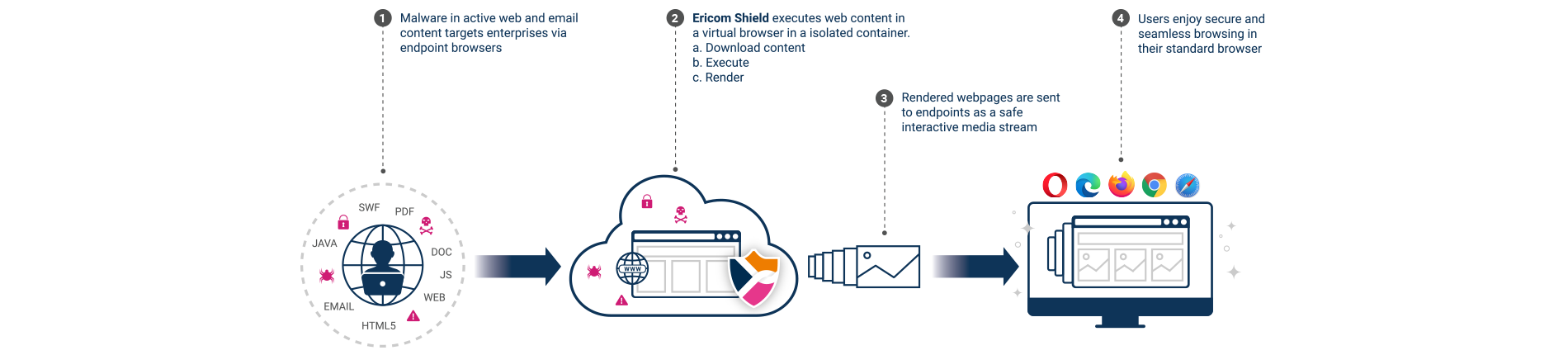
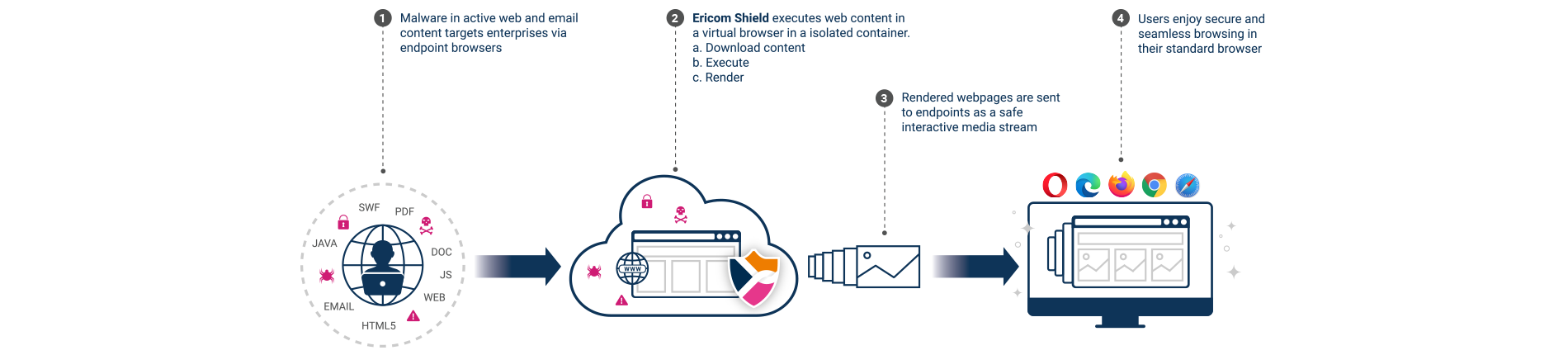
With over 60% of the world’s population estimated to be active web users, the web browser has become the most world’s most widely used application. Unfortunately, it’s also one of the most targeted applications from a cyberthreat perspective, with hackers using malicious web code to exploit browser vulnerabilities and compromise endpoints. Ericom Shield takes an innovative approach, using remote browser isolation (RBI) technology, to protect organizations from these types of attacks.
Ericom Shield RBI prevents 100% of web-based ransomware, zero-day threats, and phishing attacks from reaching devices by executing web content in a remote, cloud-based container. Whether users browse to a malicious site on their own or click on a URL embedded in a phishing email, they are completely safe since no web content is ever executed directly in the browser. The website, isolated in a remote cloud container, is rendered and sent to the user’s device as safe rendering information, providing a safe, fully interactive, seamless user experience. For additional protection from phishing attacks, websites launched from emails can be rendered in read-only mode to prevent users from entering credentials. Attached files are sanitized before users download them, ensuring that malware within documents cannot compromise endpoints.
In addition to browsers being a vector for malware, the websites and cloud apps to which they provide access, are prime channels for data leaks. Browser caches (especially in unmanaged devices), social media and cloud storage apps, and even print-from-browser functions represent data security risks. To prevent data loss, Ericom Shield allows IT teams to set policies to limit users’ data sharing actions on websites and cloud apps. For example, users trying to print pages from internal web apps, downloads or uploads may be blocked, or data may be kept from entering the browser cache on unmanaged BYOD devices.
How we are different
Ericom Shield RBI faces direct and indirect competitors.
· Indirect competitors are traditional security gateway solutions – Secure Web/Email Gateways and Next Generation Firewalls – that use legacy scanning approaches designed to “detect then protect” by attempting to match known malware signatures to internet traffic in the hope of catching threats. If they spot malware, they can block it. Unfortunately, if they miss something – like a zero-day strain of malware – it gets in. Ericom takes a fundamentally different approach, a Zero Trust approach, to protecting the browser that is designed to “trust nothing, verify everything”. Ericom Shield assumes that every site a user visits is a threat and has the potential to deliver malware. By rendering all websites in a remote, isolated container and sending only safe information to users’ devices, Ericom Shield prevents 100% of web-based malware from reaching the users’ devices. Additionally, pre-integrated multi-scan and sanitization technology ensures downloads are safe and fully functional.
Compared to alternative Remote Browser Isolation competitors (Direct Competition), Ericom Shield differentiates in two key areas: User Experience and Security Approach:
· User Experience: Ericom Shield cloud service is deployed on the Ericom Global Cloud platform, a global cloud infrastructure with autoscaling and high availability, delivering latency roughly equivalent to what the user’s browsing experience would be if going directly to the site without any isolation protection. Shield also has proprietary techniques that allow it to correctly render the broadest set of websites in the industry. With Ericom Shield behind the scenes, the end user is not even aware the site is being isolated.
· Security: Shield renders pages in multiple modes, giving organizations the ability to balance the highest levels of security with performance. Further, Ericom Shield has a number of information sharing controls that can be used to prevent data leakage to the web.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

