eSentire Managed Detection and Response
Recognized in the Category:
Photo Gallery

|

|
eSentire Managed Detection and Response

Additional Info
| Company | eSentire |
| Company size | 100 - 499 employees |
| Website | https://www.esentire.com/ |
NOMINATION HIGHLIGHTS
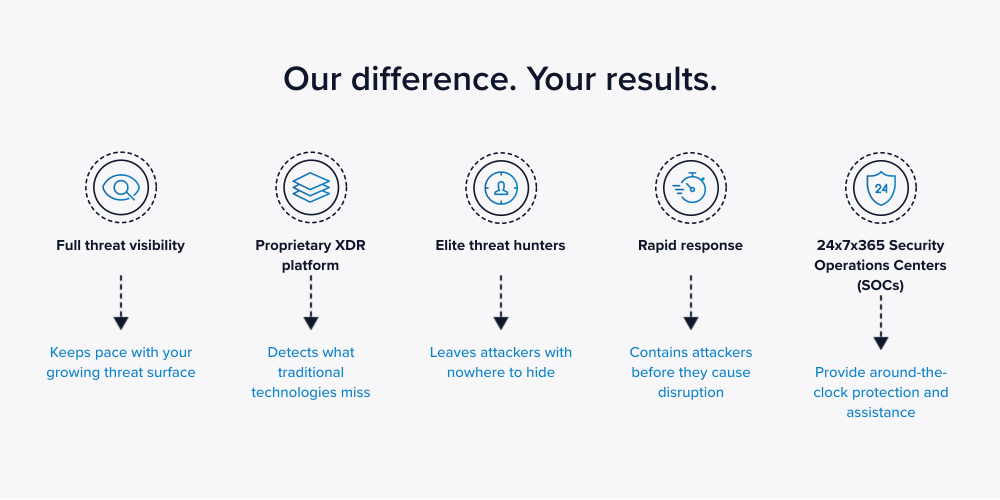
eSentire’s cloud-native Managed Detection and Response (MDR) offering is a modern solution that keeps organizations safe from the cyberattacks that traditional cybersecurity technologies miss. eSentire’s elite security analysts, who staff our 24x7x365 Security Operations Centers (SOCs), hunt, investigate, and respond on a customer’s behalf to known and unknown threats in real-time before they become business-disrupting events. With visibility across all signal sources — network, endpoint, logging, cloud and on-premises — we can ensure that our customers’ data and applications are never compromised.
eSentire MDR significantly reduces threat-actor dwell time, then rapidly contains and remediates cyber threats to ensure that they don’t adversely affect customers. We reduce an organization’s cybersecurity total cost of ownership with an integrated service that combines people, processes, and technology and absorbs the considerable challenges of operationalizing cybersecurity in a “DIY” model.
Over the past 12 months, our SOCs stopped over 2 billion signals which bypassed traditional security controls. We encounter at least one potentially business-disruptive event daily, which we investigate, isolate, and remediate before it can cause damage. How do we do it?
* 24x7x365 continuous hunting/monitoring
* Detection of unknown attacks, leveraging patterns, and behavioral analytics
* Human-led investigation, utilizing always-on, full-packet capture logs, endpoint, and event data
* Full forensics analysis to confirm threats/eliminate false positives
* Threat isolation and communication disruption performed on client’s behalf with no retainer
* Full remediation support (not just alerts/guidance) until the threat is eliminated
How we are different
eSentire’s Managed Detection and Response Solution:
* The average time to respond to a cyber threat is 35 seconds; average time to resolving a threat is 10.5 minutes, and an average service level objective (SLO) to remediation of 20 minutes
* Stops breaches in real time on customers’ behalf, unlike the competition, which sends alerts and leaves customers to contain threats on their own.
* The company employs cybersecurity experts who are available 24x7x365 to assist customers, no matter the issue

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

