Photo Gallery
 |

 |
Forescout – Zero Trust Security


Additional Info
| Company | Forescout Technologies Inc. |
| Company size | 1,000 - 4,999 employees |
| Website | https://www.forescout.com/ |
NOMINATION HIGHLIGHTS
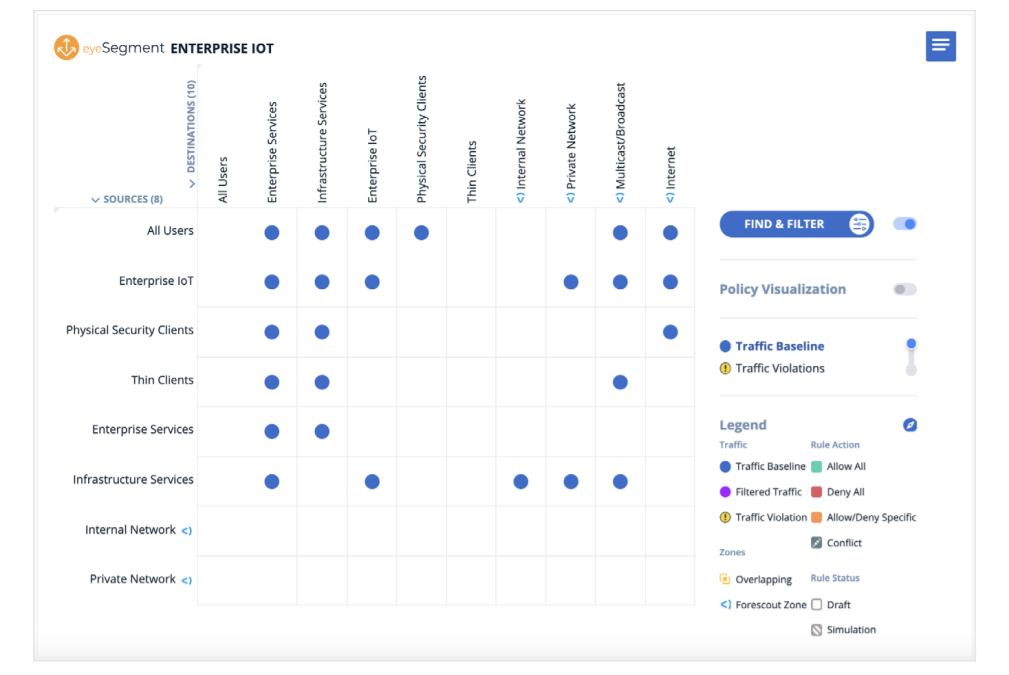
Network segmentation has become a critical component of Zero Trust programs and organizations’ ability to maintain compliance amid numerous regulations being introduced by governments and industry bodies. Forescout believes that IoT security must be based on a Zero Trust approach that combines complete device visibility, proactive network segmentation and least-privilege access control of all digital assets –devices, users, apps and workloads.
To support organizations with their Zero Trust initiatives, Forescout recently expanded its set of network segmentation capabilities on the Forescout platform that will provide end-to-end visibility and real-time analysis to automate risk mitigation and policy management.
These capabilities offer a clear path from managed network access to full Zero Trust. With Forescout, organizations are able to take a more proactive stance in combating threats posed by all devices. A clear path to execute network segmentation is imperative, and Forescout embraces these three principles to help lead the most successful network segmentation outcomes:
– Understand business requirements
– Know what is on the network and how it communicates
– Visualize traffic flows
Forescout continues to help security teams of workers and CISOs explore new tactics in the evolving threat landscape by encouraging them to:
– Follow a Zero Trust model to ensure security leaders are accounting for any potential risks that may have arisen due to remote work
– Update cybersecurity strategies and quiet networks to baseline network activity for better understanding of anomalous activity
– Educate workers on best practices for remote work
Based on the effective and efficient nature of its platform and guidance, Forescout has been selected by prominent organizations to help implement Zero Trust architectures and/or initiatives, including the National Institute of Standards and Technology’s (NIST) National Cybersecurity Center of Excellence (NCCoE), Canada’s University Health Network, and the Defense Information Systems Agency (DISA).
How we are different
The Forescout platform’s network segmentation capabilities provide unparalleled end-to-end visibility and real-time analysis to automate risk mitigation and policy management, allowing organizations to more effectively pursue Zero Trust programs. With Forescout, companies have increased ability to simplify the design, planning and deployment of non-disruptive, dynamic segmentation across their Enterprise of Things to reduce attack surfaces and regulatory risk. Existing infrastructure can be leveraged, instead of starting from scratch, meaning that customers can streamline integration across multiple network security solutions and more quickly identify authorized/unauthorized devices. After deployment, this is 30% more on average than customers originally anticipated.
Forescout values the performance of its end-products and the experience of its end-users. Forescout uses its powerful policy enforcement and industry-leading device knowledge to advise customers on how to make smarter decisions on security and business strategy in an ever-evolving threat landscape. Today, over 3,800 global companies, including many Fortune 1000 companies, rely on Forescout and its 20+ years of device intelligence and automated cybersecurity governance to mitigate risks from network-connected devices. With the consistent increase in connected devices and rise in sophisticated attacks, organizations can trust Forescout to secure enterprises, continuously innovate its solutions, and guide its customers in Zero Trust programs that help secure the cybersecurity community at large.
Forescout has earned partnerships with prominent organizations across diverse industries ranging from government to healthcare to manufacturing and beyond. This is a testament to the platform’s versatility and the company’s reliability. For instance, in 2021, Forescout was selected by the National Institute of Standards and Technology’s (NIST) National Cybersecurity Center of Excellence (NCCoE), Canada’s University Health Network, and the Defense Information Systems Agency (DISA) to help develop Zero Trust architectures and initiatives for enterprises that wish to implement Zero Trust security defenses.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



