Photo Gallery
 |

 |
Fudo PAM

Additional Info
| Company | Fudo Security |
| Company size | 50 - 99 employees |
| Website | http://www.fudosecurity.com |
NOMINATION HIGHLIGHTS
As the normal security perimeter approach is no longer sufficient, organizations need to adopt ways to ensure that all users within the network are given appropriate access to key resources. Fudo PAM allows for this kind of monitoring which is even more crucial in the current global environment, as remote work has spiked and normal security expectations have had to adapt to an increase in security vulnerabilities from external as well as internal sources.
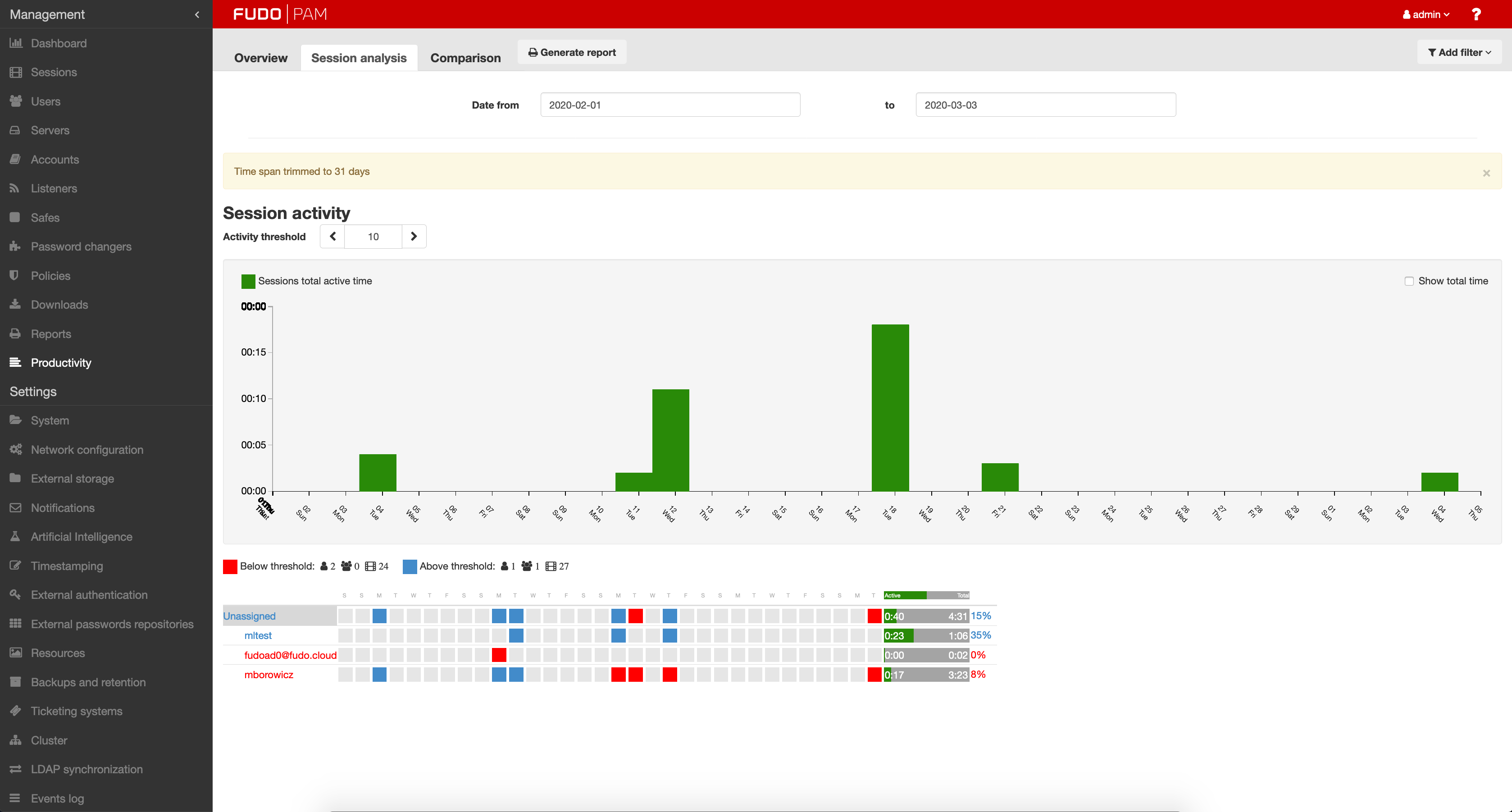
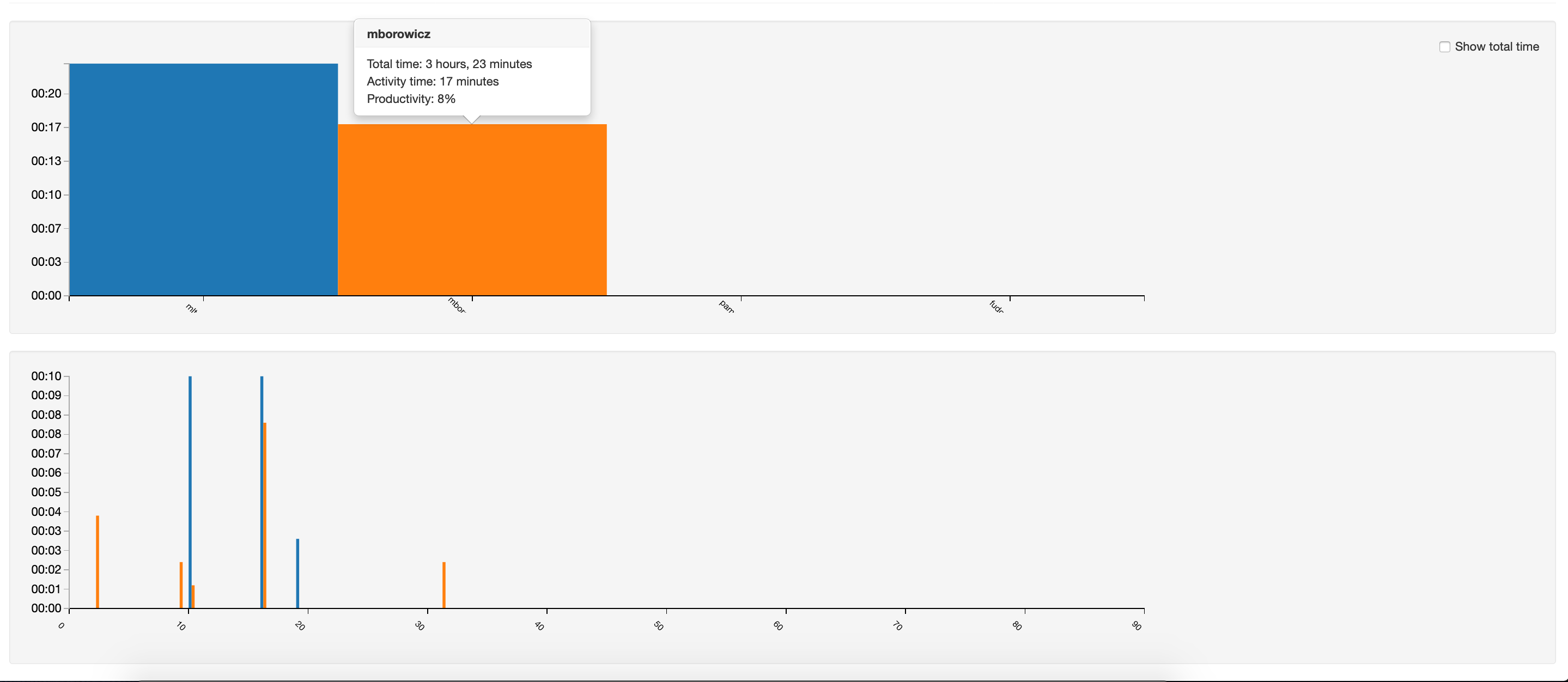
While firewall logs only provide proof that given resources have been accessed, usually without pinpointing the exact user, Fudo PAM records all user actions and who performed them, including executed commands, transferred files, mouse movement, etc. Its state-of-the-art AI, monitoring and prevention technology, ensures the servers are accessed by approved users only.
Thanks to Fudo’s top-tier session recorder, you can easily monitor and archive any action taken on your servers and applications – even web-based ones. Backed by AI real-time monitoring, all the actions of users and third party contractors can be tracked, analyzed and reported as they happen.
Additionally, one of the crucial elements of Fudo PAM is the built-in User Access Gateway, leveraging the power of protection and security that PAM systems provide with an ease of use by non-technical users. This can be leveraged to provide secure access to a company’s infrastructure, with a straightforward way for working remotely.
One of the most valuable features of Fudo PAM is the ability to deploy it swiftly, usually in one day or less, depending on the complexity of the IT infrastructure it needs to integrate with.
How we are different
* Unmatched http/rdp/vnc session management: visual session playback for RDP, SSH, Telnet and HTTPs
*Award-winning AI-powered biometric verification (patent-pending technology)
*The only effective real-time privileged misuse prevention

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



