Fudo PAM
Photo Gallery
 |

 |
Fudo PAM

Additional Info
| Company | Fudo Security |
| Website | http://www.fudosecurity.com |
| Company size (employees) | 50 to 99 |
| Type of solution | Software |
Overview
Privileged accounts enable unrestricted access to essential IT resources: main servers, networking equipment or users’ workstations. They also provide the tools necessary to cover up possible administrator errors.
A lack of control over privileged users puts the integrity and security of a company’s data at risk, especially in the case of outsourcing IT services. Taking over a privileged account by an unauthorized person may lead to a data leak and damaging an enterprise’s reputation.
The GDPR law acknowledges that monitoring and recording the administrators’ behavior is crucial while managing data leaks and modifications of personal databases.
Fudo responds to the security needs of modern companies, concerning not only the external threat but also complying with various regulations. Fudo is dedicated to the institutions that are aware that criminals are also driven by business intuition, so they strike in the areas which are most vulnerable to attack. That means they disguise themselves as remote IT consultants, taking over administrative accounts, or exploiting weaknesses in password management procedures within critical sectors of the organization’s infrastructure.
How we are different
* Unmatched shield against attacks on any operating systems and network protocols.
*Possibility to use recorded sessions as evidence in court. The recording is also
evidence for the suspected administrator or other privileged user that the error was not
caused by his/her actions.
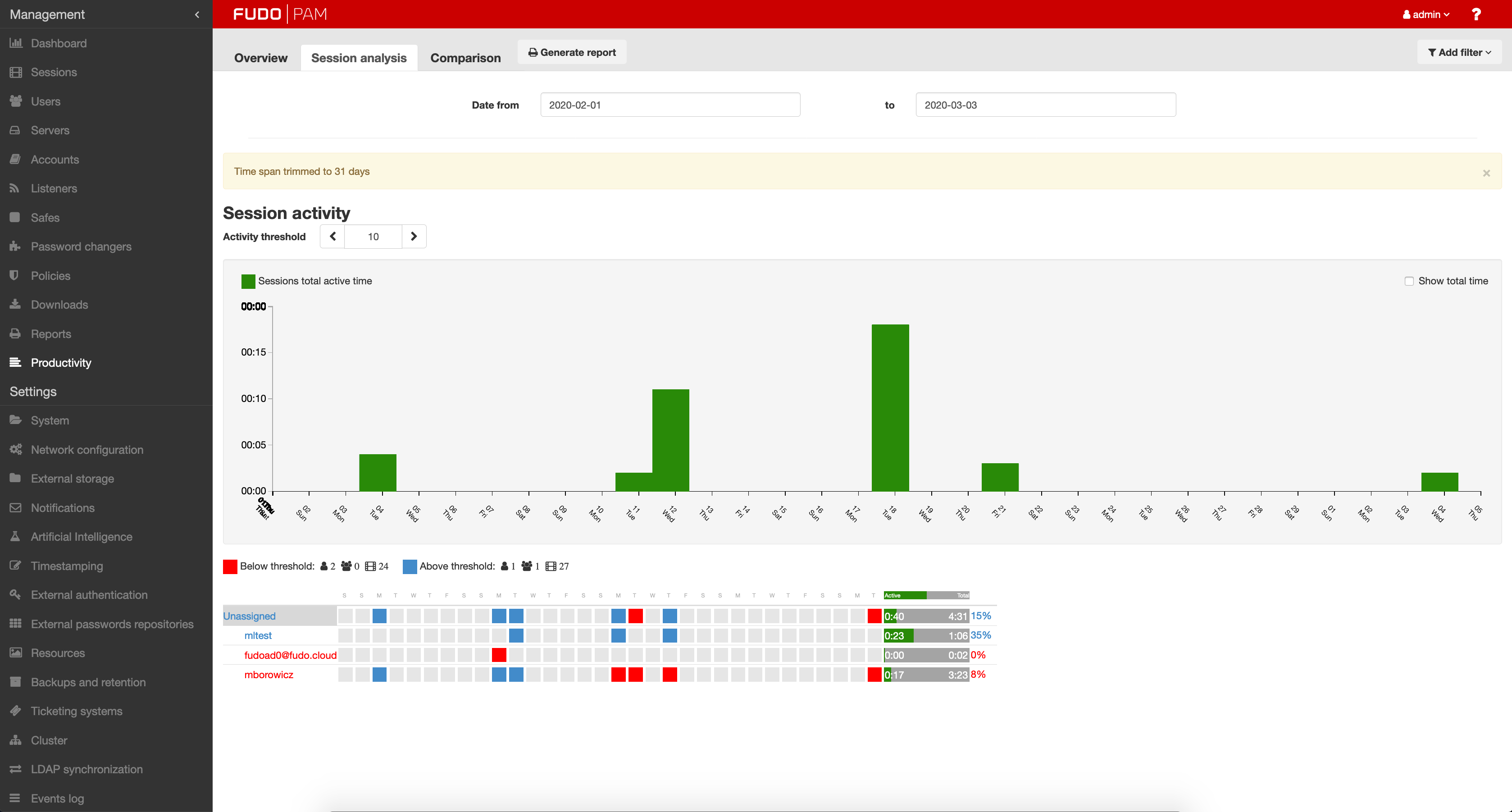
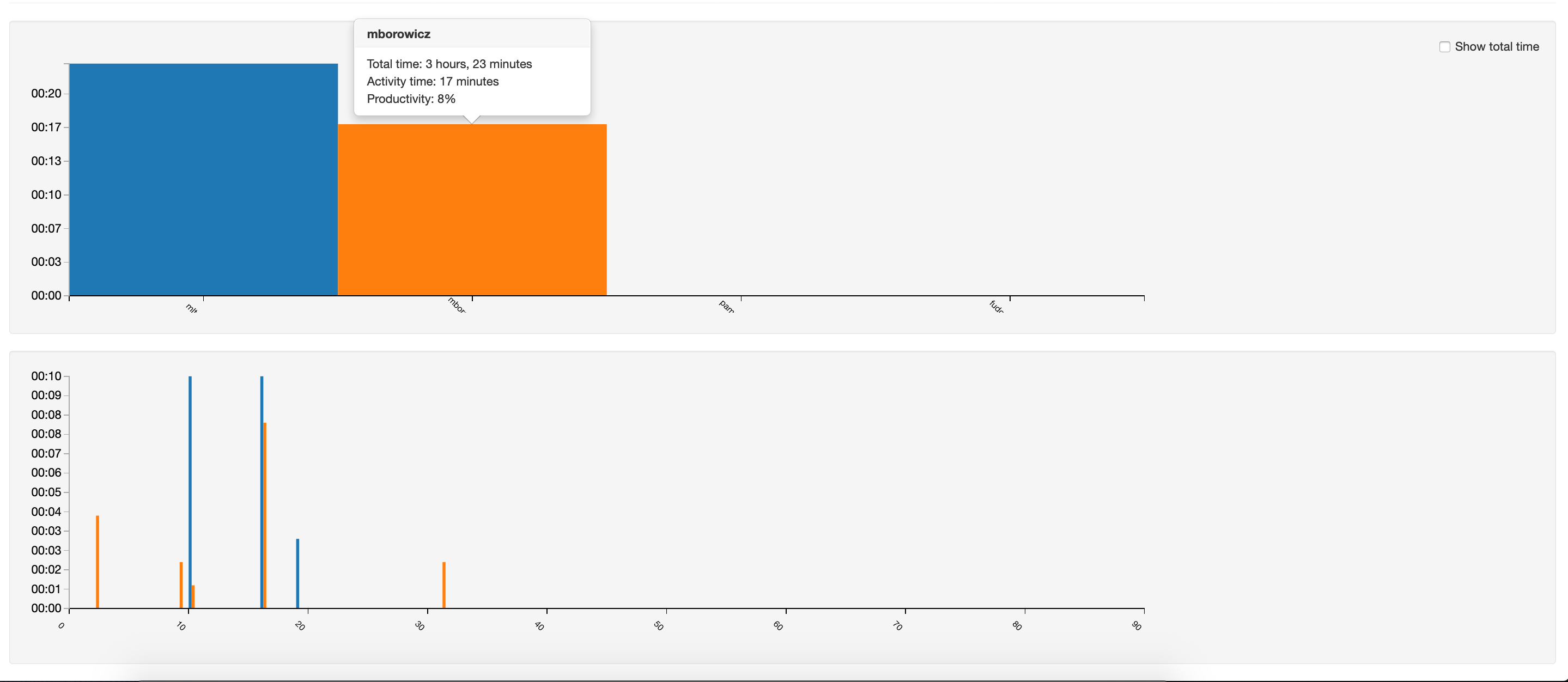
*Fudo’s efficiency analyzer is an imperative element in documenting an organization's
activities to minimize the risk of personal data leakage in the GDPR aspect.



