Photo Gallery
 |
 |
Fudo PAM

Additional Info
| Company | Fudo Security |
| Company size | 50 - 99 employees |
| Website | http://www.fudosecurity.com |
NOMINATION HIGHLIGHTS
Fudo PAM provides the next generation of privileged access management – it provides a complete password management system for secrets management, seamless live session streaming and recording, and AI anomaly detection to continuously analyze behavior patterns and anomalies and make sure there is no identity theft happening inside or outside of the network. Best of all, Fudo PAM is a self-contained system that can be deployed in a single day, to quickly protect your credentials – and valuable corporate data – from cyberattacks.
Top notch session monitoring with prevention:
Fudo provides every possible tool to supervise privileged remote sessions including: live sessions viewing, and session sharing for both Fudo users as well as third parties. Proactive monitoring allows for notification alerts, suspension or termination of a suspicious session.
Built for performance – high load ready:
Fudo PAM supports a multi-master cluster configuration ensuring high availability and
performance scaling. Fudo appliances can handle even up to hundreds or thousands of
concurrent connections, depending on session properties.
All in one Solution, deployable in one day:
Fudo PAM is a self-contained system, including storage and a complete set of management tools. No agents, no additional licenses, no downtime.
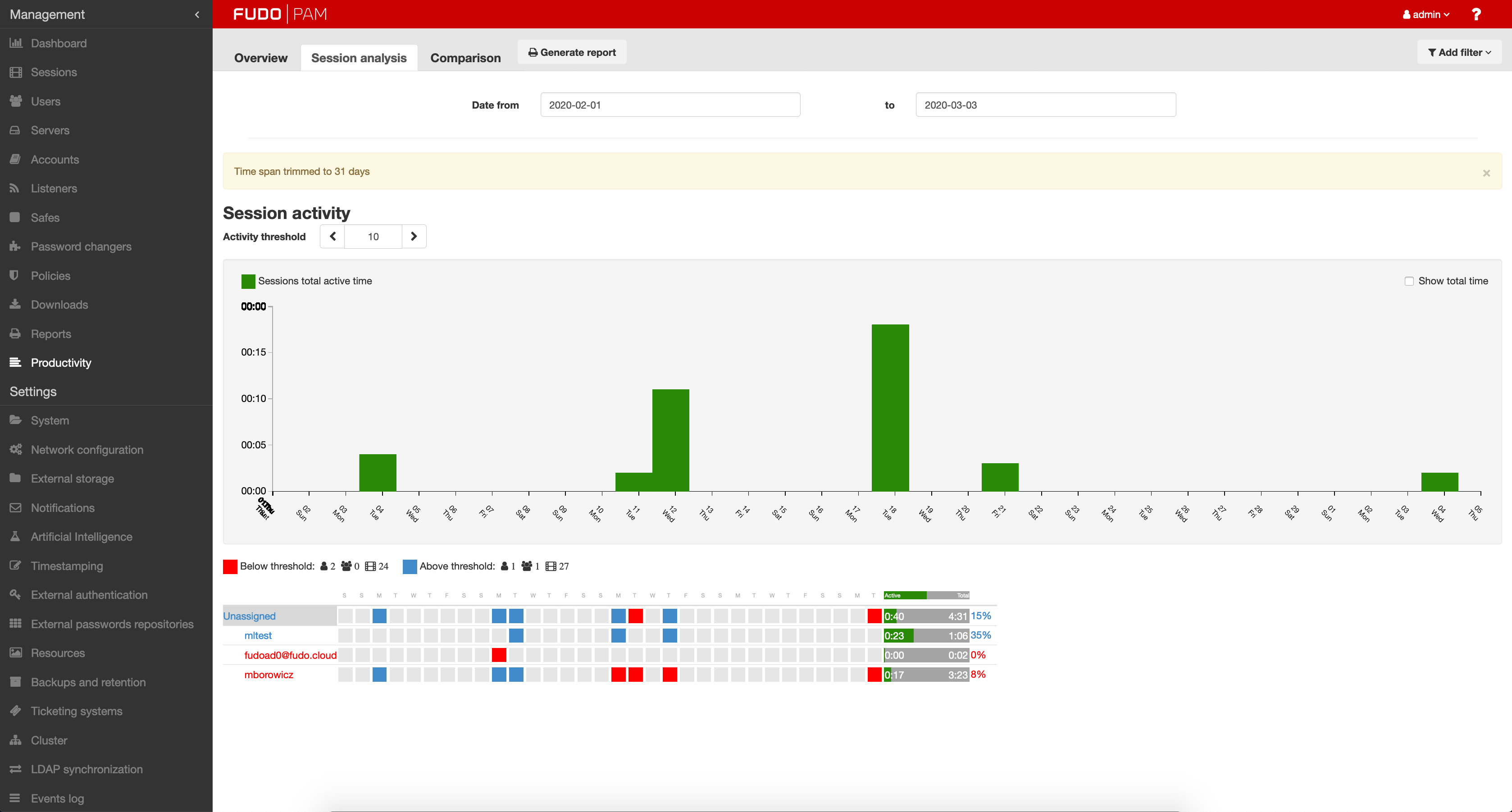
Behavioral analytics through machine learning:
Fudo PAM enables existing systems to build user and system usage profiles, based on continuous analysis of behavior patterns and anomalies. The AI module is able to accurately detect changes in user behavior and take defined actions to prevent misuse. It also keeps close track of volumetric parameter sessions and alerts the system administrator when it detects anomalies related to the number of sessions or their duration. Login credentials by themselves are no longer sufficient to impersonate an authorized user with impunity.
How we are different
● Award-winning AI-powered biometric verification (patent-pending technology)
● Real-time privileged misuse prevention
● Unmatched http/rdp/vnc session management

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



