GoodAccess
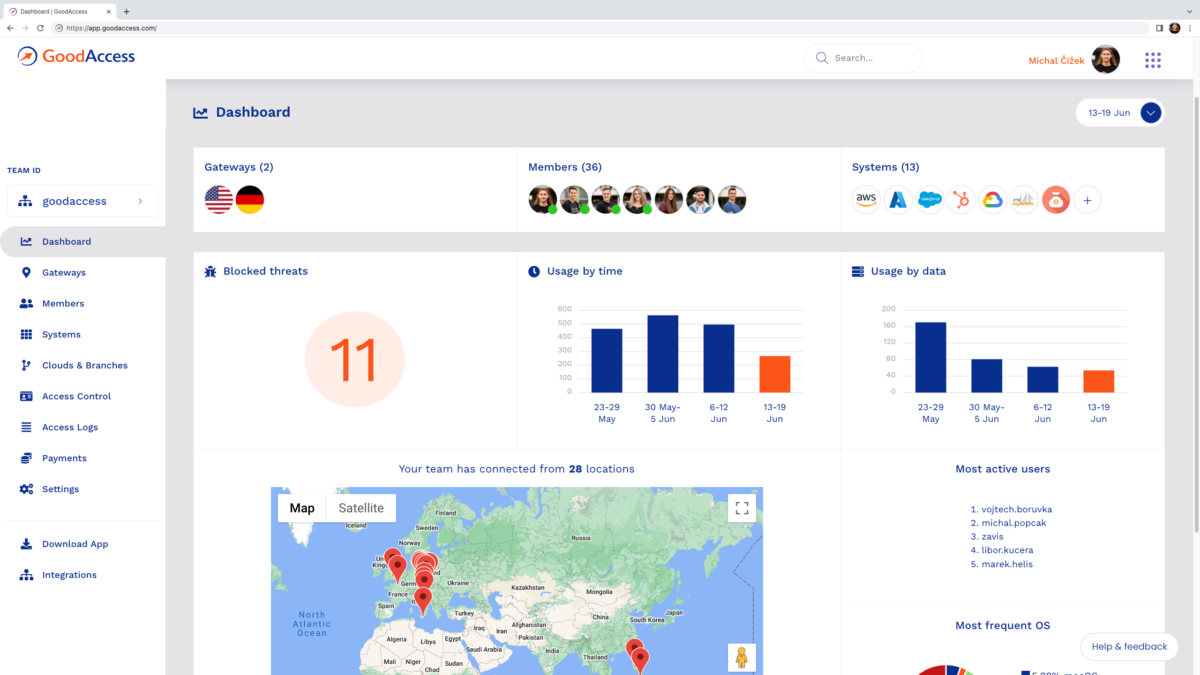
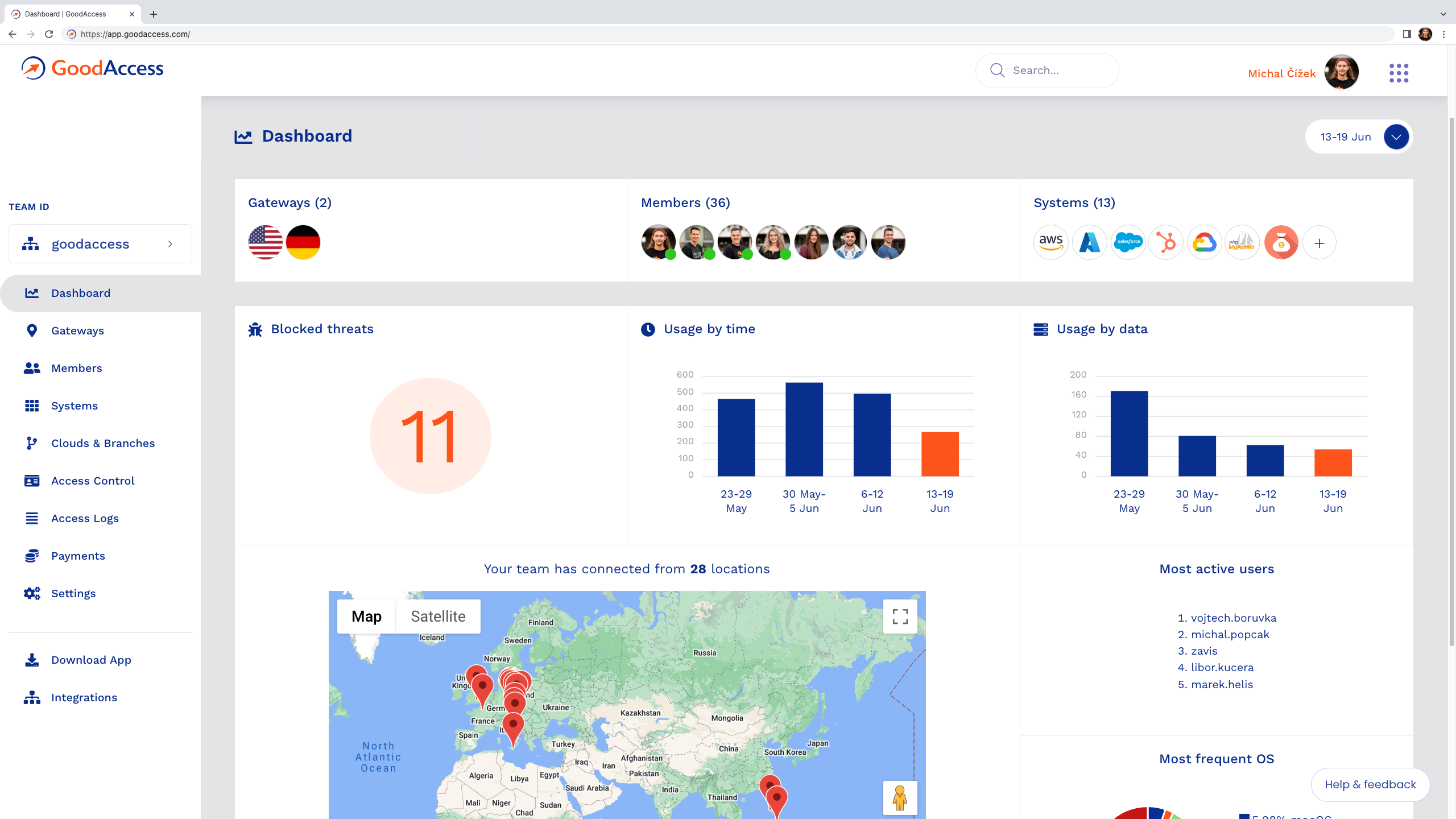
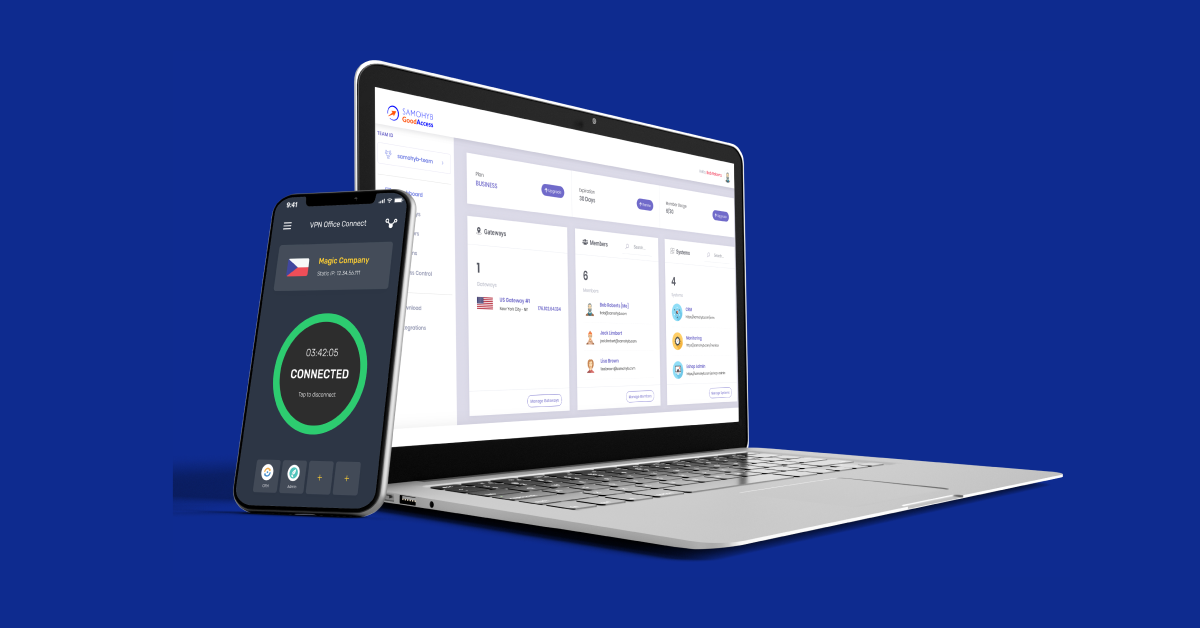
Photo Gallery
 |

 |
GoodAccess

Additional Info
| Website | http://www.goodaccess.com |
| Company size (employees) | 10 to 49 |
| Headquarters Region | Europe |
Overview
In GoodAccess, we invest our passion into developing an affordable zero-trust network access solution that is easy to deploy, easy to manage, and easy to use. Thanks to this, any company can provision secure remote access to its business systems, clouds, and data in 10 minutes. Even without a dedicated networking expert. Anytime, anywhere.
GoodAccess is the cybersecurity platform that gives businesses the security benefits of zero trust without the complexities so users can securely access digital resources anytime, anywhere. It is the world’s simplest SaaS for enabling zero-trust access to business networks. Tailored to meet SMB’s needs, it allows mitigating the risks introduced by remote workforce, BYOD and distributed IT resources with no hassle.
Our platform is recognized by TechRadar as one of the best ZTNA solutions and acclaimed by leading review platforms such as G2 and Capterra for its excellence in customer support, simplicity, and ease of use.
As part of our mission, in 2022 we brought companies all around the world the first forever-free business VPN that helps them achieve secure remote access essentials with no constraints.
How we are different
- GoodAccess has taken a far different approach than other security companies by catering to the needs of small and medium businesses which typically lack security personnel, budgets and other resources. GoodAccess sees the VPN as being capable of far more than simply being a traditional VPN and a way to provide robust security to small and medium companies. It provides a unique VPN cloud with zero-trust access controls for each organization, enabling encrypted internet access and online threat protection for remote employees, network-less offices and cloud resources and applications. No hardware or complex set-up is required, as the platform is fully cloud-based and designed to deploy in less than 10 minutes.
- GoodAccess extends secure private browsing and use of cloud applications to each employee, protecting their identity, devices and connections. Encrypting the network layer in browser-based communications provides privacy and protects against phishing and malicious software attacks from compromised websites. GoodAccess provides fixed IP addresses and white and black listing for deterministic, controlled connections. GoodAccess includes advanced authentication, device state security checks, flexible policy-based rules and other technologies to protect users, defeat malware, phishing and ransomware.
- GoodAccess also incorporates Zero Trust Network Access for further protection. It provides the easiest way for small and medium companies to add zero trust without undue complexity and expense. For many companies this means the ability to add zero trust when it would otherwise be impossible.



