Photo Gallery
 |

 |
Group-IB Cyber Threat Intelligence

Additional Info
| Company | Group-IB |
| Company size | 500 - 999 employees |
| Website | https://www.group-ib.com/ |
NOMINATION HIGHLIGHTS
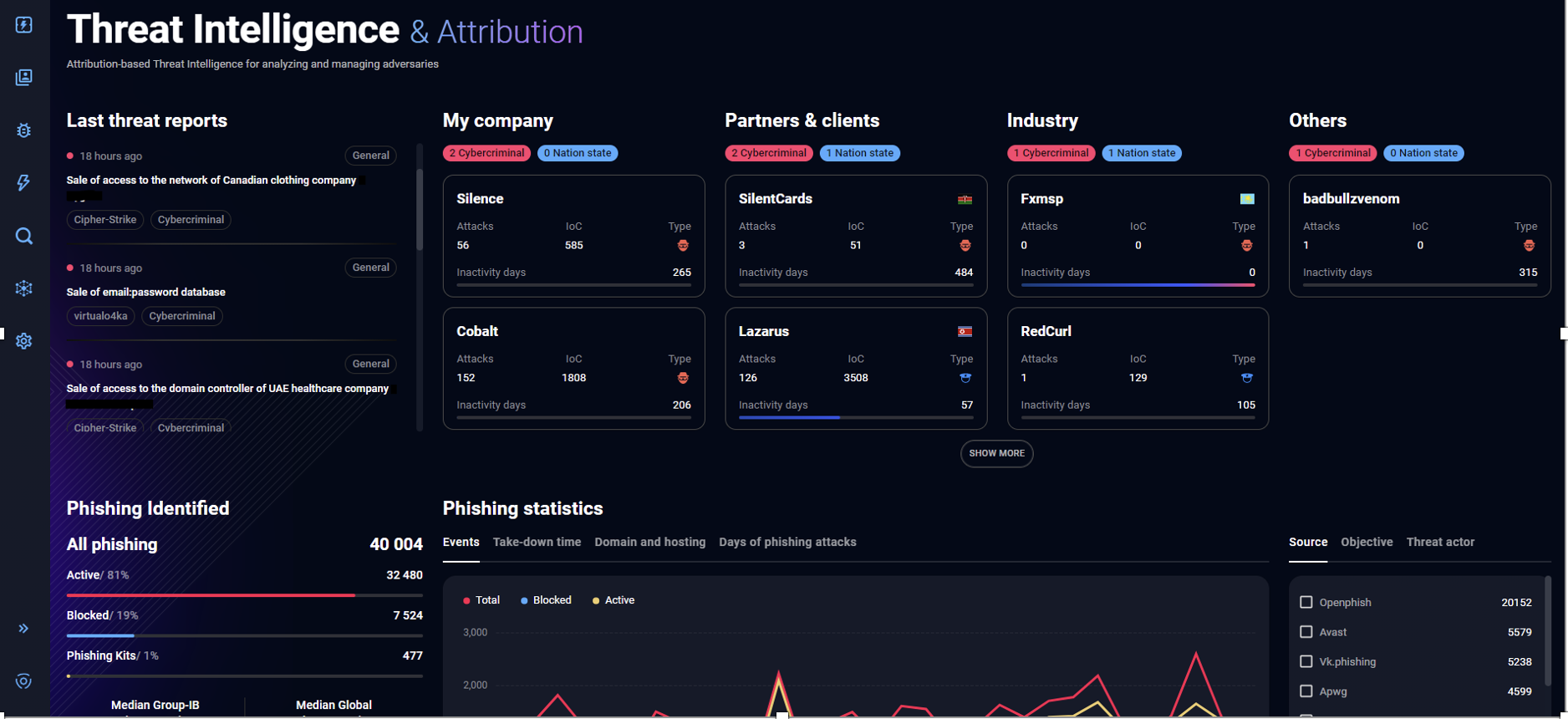
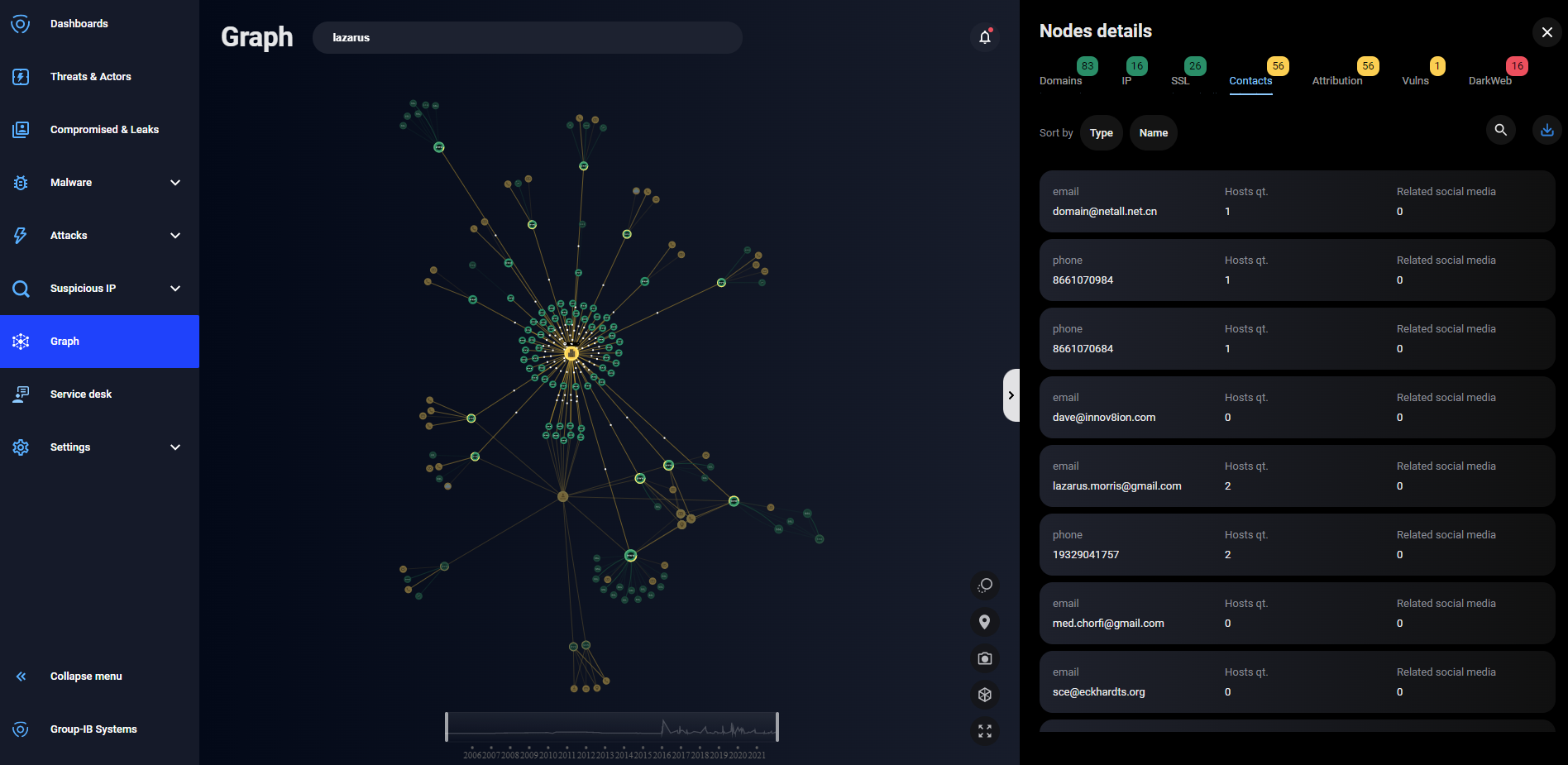
Group-IB Threat Intelligence & Attribution provides security teams with the latest information about the tactics, techniques and procedures being used by threat actors targeting their organization, industry, partners and customers. These insights are used to improve security posture, enabling teams to make data driven decisions.
Better strategic decisions are made by using the information to assess risk and decide where to allocate budget to achieve a strong, cost effective security. Improvements can be made to operational security practices with insight into attacker behaviours and infrastructure, for example teams can improve vulnerability management by prioritizing patching with intel about common exploits. Tactical decision making is improved with tailored data about more informed alert triage and incident analysis.
Intelligence is filtered for each customer, providing comprehensive visibility of their unique threat landscape. Group-IB works with stakeholder groups within the organization to establish priority intelligence requirements, which are continuously refined, to ensure that their threat intelligence is relevant and actionable.
To understand threat actor activities Group-IB uses a range of sources:
Human Intelligence – Undercover agents in underground forums on the dark web
Malware Intelligence – Advanced malware detonation platform & malware configuration files extraction, public sandboxes, honeypot networks, malware reverse engineering
Data intelligence – C&C-server analysis (botnet and phishing), C&C-servers of JS-sniffers, phishing data collection points and cardshops
Open source intelligence – Paste sites like Pastebin, code repositories like GitHub, messengers, social networks, vulnerabilities and exploits, and URL sharing services
Telemetry – ISP-level sensors, botnet data extractors, IP scanners and web crawlers, passive DNS and SSL collection
Investigations – Collaboration with law enforcement around the world including Interpol and Europol
Teams can consume intelligence in a number formats to suit their needs. Analyst written reports can be downloaded and shared with executives, the online portal allows teams to conduct research, and machine-to-machine intelligence sharing automates workflows.
How we are different
Group-IB’s threat intelligence is highly actionable, it is curated and maintained by highly skilled analysts so that organizations can get the most value from it. Forrester Consulting conducted a Total Economic Impact assessment and evaluated that deploying Group-IB provides strong financial benefits. The results of their analysis found that a reference Group-IB Threat Intelligence & Attribution customer had a 339% return on investment. deploying the solution had a 2.6 million USD net present value and a payback period of under 6 months.
Group-IB is a technology leader, with over 100 patents around the world for intelligence gathering tools, making the solution one of the most advanced available. In Frost & Sullivan’s 2021 market analysis they found that “Group-IB is one of the most innovative vendors in the market and a leader on the Frost Radar.”. Furthermore, Group-IB is the only vendor who passed compliance with recommendations from the US DoJ’s Legal Considerations when Gathering Online Cyber Threat Intelligence and Purchasing Data from Illicit Sources.
Group-IB has investigations and incident response in it’s DNA, we have over 18 years of experience in the field and frequently collaborate with law enforcement around the world, including with Interpol and Europol. These connections grant Group-IB access to exclusive data about threat actor groups which we make available to our customers. Additionally, Group-IB works with law enforcement to fully neutralize criminals, helping take their infrastructure offline and convict them.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



