Photo Gallery
 |
 |
GRSee Consulting | Pentest as a Service

Additional Info
| Company | GRSee Consulting | Compliance ASAP |
| Company size | 50 - 99 employees |
| World Region | North America |
| Website | grsee.com |
NOMINATION HIGHLIGHTS
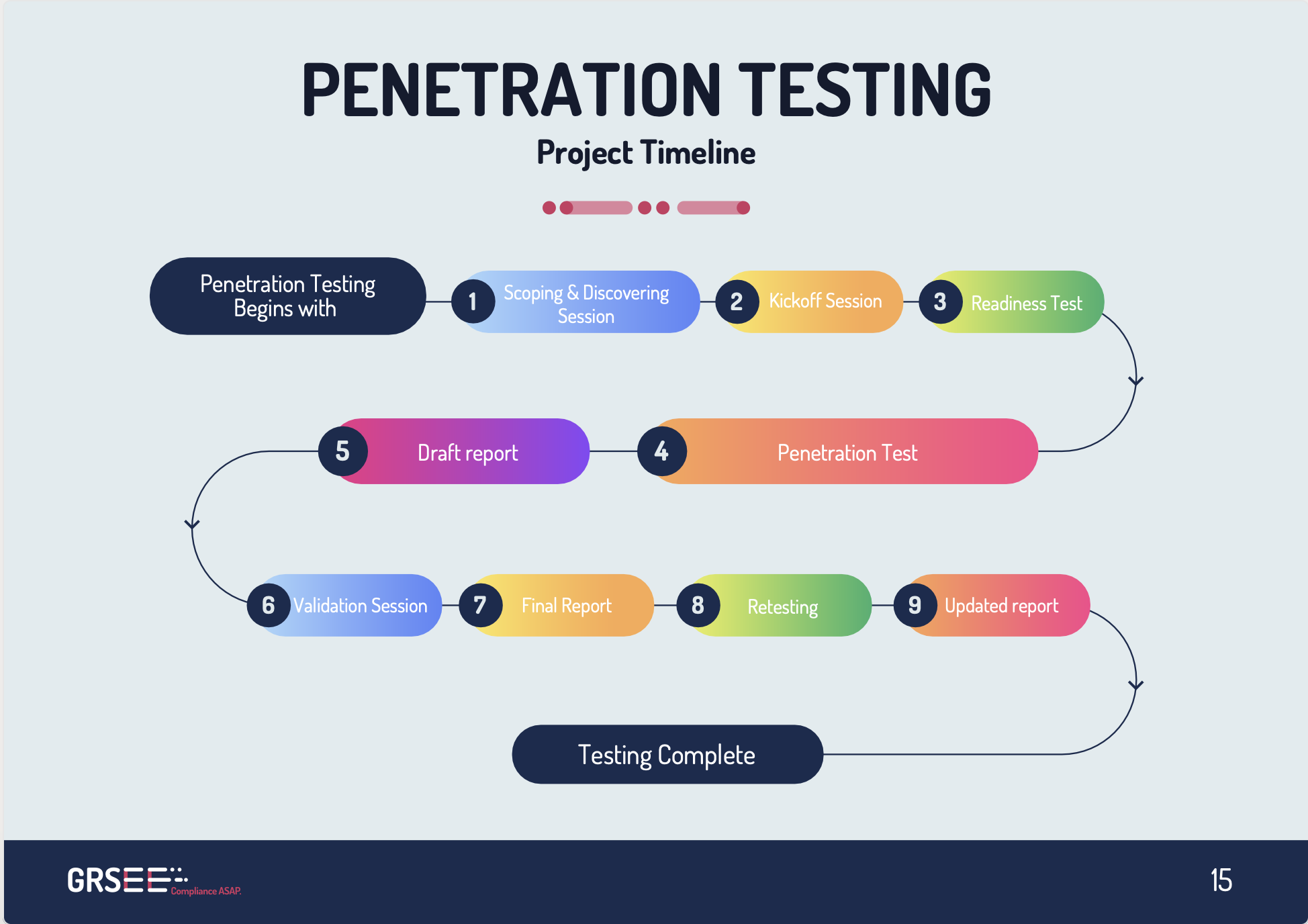
GRSee Consulting is one of the leading PenTest service providers with a 95% NPS score. A Penetration Test is a real-time, managed, simulated cyberattack done by authorized and professional Pen-testers with the intention of discovering vulnerabilities in the targeted environment.
At an age where the volume of data and information stolen is at its peak, having a clean penetration report proves the maturity of product and service security. It also brings in self-assurance while earning the trust of clients.
Our approach to Penetration Testing helps our clients dispel the concerns around data breaches, discover current vulnerabilities, prepare against malicious intent, and ensure business continuity.
The insights gained from this simulated attack help companies fix their current vulnerabilities, build a strong security posture, and offer a safer user environment to clients and vendors.
GRSee Consulting’s PenTest offering includes approaches like:
**White Box:**
It simulates a state where the supposed hacker (penetration tester) has full knowledge of and access to elements like the source code and software architecture of the web application. This aims to reveal exploitable errors hidden in the code, infrastructure, and software integration and is beneficial in improving the software code and overall application quality.
**Gray Box:**
Grey Box Penetration Testing (also known as authenticated PT) involves a situation where the tester has obtained partial knowledge of the platform and credentials. With this information, the tester inspects the platform’s resilience, post-login attack vectors, and multi-tenant attack vectors.
**Black Box:**
Black Box Penetration Testing (also known as unauthenticated PT) simulates a state where the hacker knows very little about the cyber infrastructure. In Black Box, the tester only tests public resources like login pages, legal IP addresses, etc. and focuses on ‘pre-login’ attack vectors.
How we are different
- We provide Ongoing Penetration Testing packages to clients to make sure they’re always one step ahead of finding and fixing their vulnerabilities as they continue to grow their product.
- Our team has yet to find a security system that doesn’t have a vulnerable security flaw.
- We have a tried and tested methodology, and all our testers are seasoned and have certifications like:
1. CEH (Certified Ethical Hacker)
2. CPT (Certified Penetration Tester)
3. OSCP (Offensive Security Certified Professional) and more

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



