Photo Gallery
 |

 |
Lumeta Enterprise Situational Intelligence (ESI)

Additional Info
| Company | Lumeta Corporation |
| Company size | 40 employees |
| Website | http://www.lumeta.com |
NOMINATION HIGHLIGHTS
Lumeta ESI includes a multi‐phase indexing methodology that identifies all assets on a network and provides a topological map of the network. It offers comprehensive, real-time network visibility to hunt for new or changed infrastructure, routes, paths, and devices, which is essential for breach detection in virtual, cloud, mobile and software-defined networks. Lumeta ESI delivers:
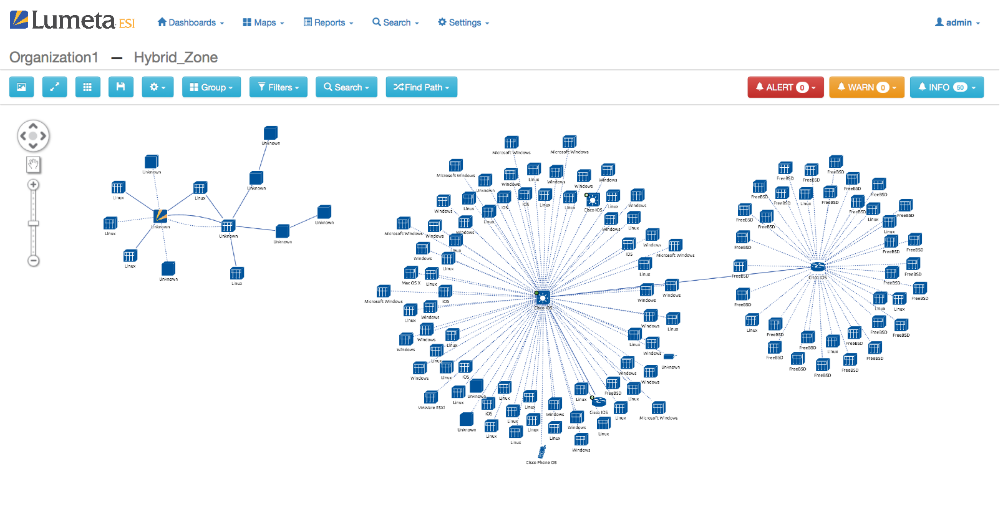
Network Infrastructure Analytics: Providing organizations with a true view of what the network really looks like (what devices and connections are attached, and how) in real time. To understand the entire network at any time, organizations need:
• an authoritative network census
• real-time network infrastructure updates (broadcast, OSPF, BGP, etc.)
• address space validation
• network edge definition
• unreachable network segment identification
• device indexing/profiling, both passive and active
• enterprise-wide certificate identification
• network topology mapping
• port mapping/usage
Network Segmentation Analytics: Providing the advanced intelligence organizations now require to verify their network segmentation and fully understand their network architecture relative to the organization’s policy. Having tools which enable quickly detecting leak paths, unauthorized Internet connectivity, multi-homed hosts, split tunneling identification, unauthorized bridging device identification along with hybrid physical/virtual segmentation provides the information teams need to understand, detect and prevent breaches.
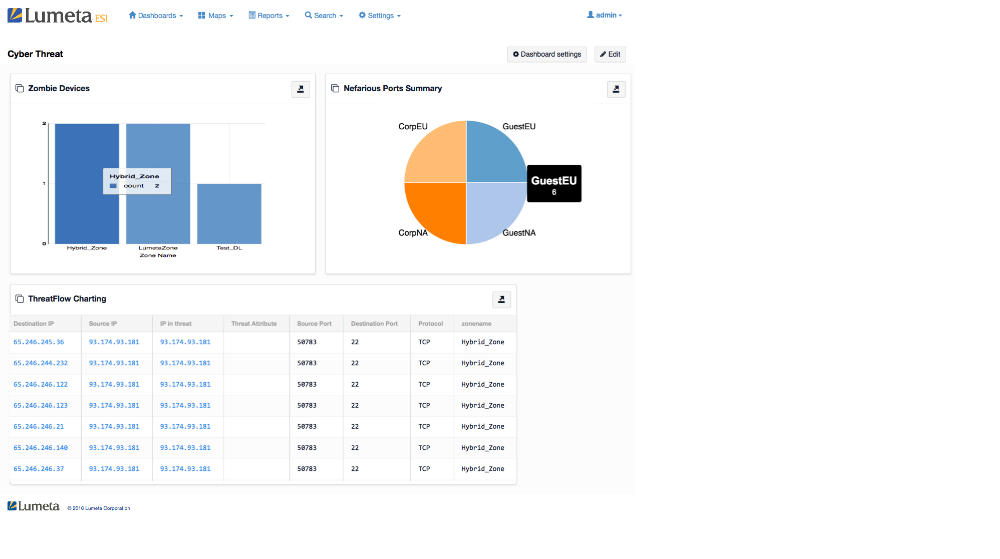
Breach Detection Analytics: Via seamless integration of Lumeta’s comprehensive network indexing to external threat intelligence sources (with the ability to ingest open source threat intelligence feeds), it operationalizes in-depth intelligence enabling security teams to:
• Identify any internal use/accessibility of known Trojan/malware ports;
• Correlate NetFlow data to malware command and control (C2) servers;
• Hunt for zombies on the network.
Lumeta’s foundational intelligence is also integrated (via an open API) with third-party products such as SIEM, GRC, HVA, IPAM, and Endpoint Detection & Response greatly improving analytical capabilities, allowing organizations to fully understand their IT environment in more context and have greater insight into network traffic, connections and devices.
How we are different
• Many IT network and security teams have little authoritative understanding about the current state of their networks. Often, 20% or more of assets are “unknown” to the teams. This is true of large, physical, static networks as well as modern networking environments involving mobile endpoints, virtualized compute and virtual network functions, private and public cloud, and software defined networking. Modern networks contain transitory infrastructure and assets – on the network one minute/hour/day, gone the next. Network and security teams often have limited control over shadow IT instances. So, while there are many cyber security tools in use within enterprise networks today, most security experts cite accurate inventory as a common concern. Gaining enterprise network visibility, via Lumeta ESI, to know what is running on a network provides the type of foundation that is essential to supporting any type of enterprise security program.
• Real-time network situational awareness through enterprise network infrastructure and asset discovery, as well as network segmentation validation, provides the base for threat/breach detection. If you don’t know what the infrastructure is, where the edge is, what endpoints you have, how they’re connected, and what routes are present, then there’s no way to quickly and efficiently handle incidents that may lead to a breach. Visibility, provided in real time by Lumeta ESI, needs to be the foundation upon which a modern security program is developed.
• Visual representation of network information is very important. Especially with large and complex networks, it takes too long to identify problems by sifting through tables with hundreds or thousands of line items. Lumeta ESI includes maps, charts, graphs and other rendered visualizations of indexed information and anomalies that involve beaconing, color changes of nodes or edges, and graphical illustration of outliers to highlight where an anomaly may exist. The objective is faster time to detection, repair

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



