Photo Gallery
|

|
Medigate

Additional Info
| Company | Medigate |
| Company size | 50 - 99 employees |
| Website | http://www.medigate.io |
NOMINATION HIGHLIGHTS
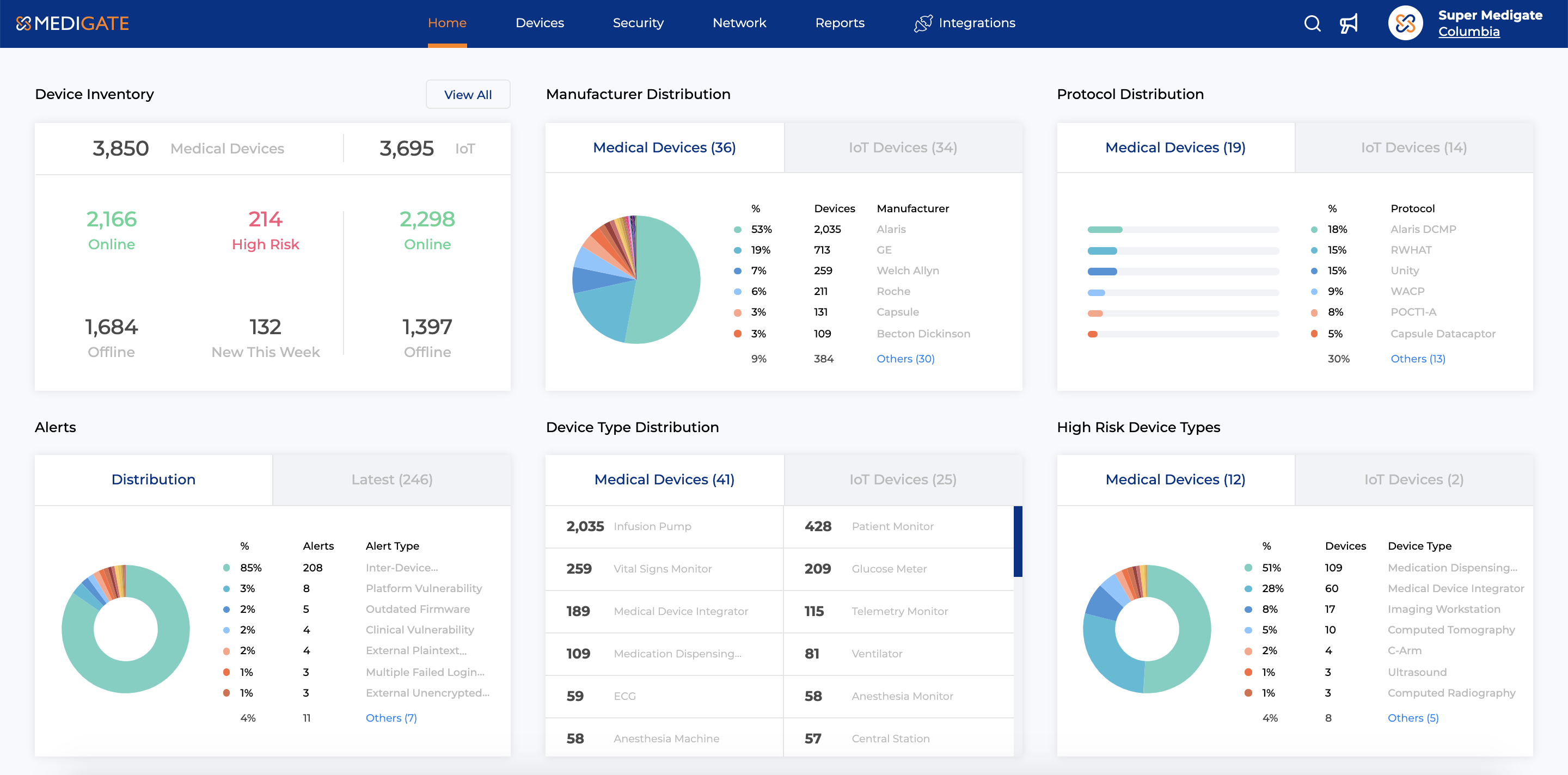
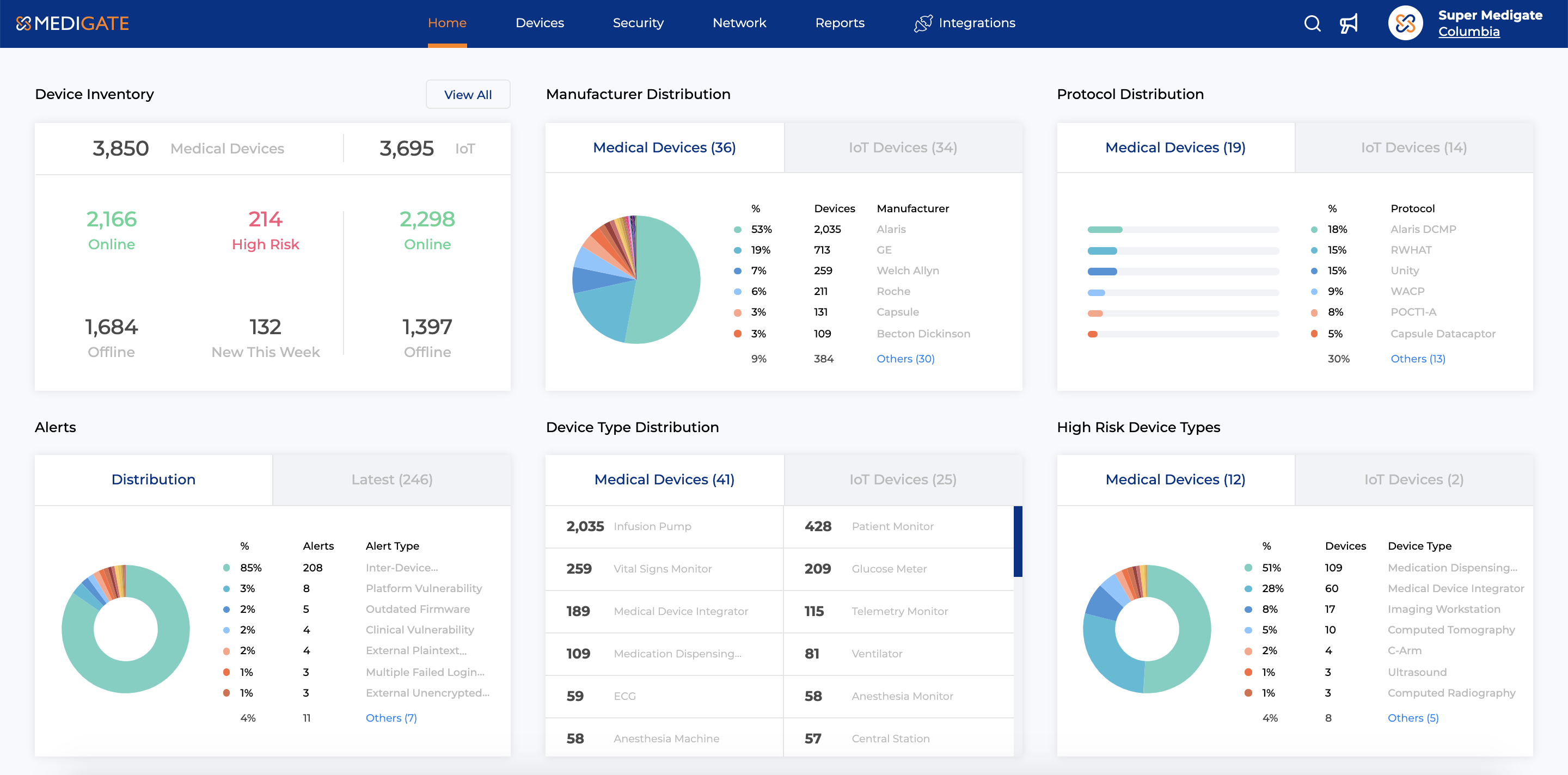
Medigate has disrupted the way assets connected to healthcare networks are managed and cyber-secured. We have created an entirely new capability – a clinically specialized platform that directly addresses the challenges of IoT asset management and notably, the security vulnerabilities of the most targeted attack surface across industry. Our innovations around the passive capture of data from devices connected to clinical networks deliver unprecedented visibility. The underlying data are enriched, contextualized for cross functional relevance and then orchestrated to the entire cybersecurity ecosystem. Essentially, we are delivering the common foundation that’s long been missing. This has allowed us to incorporate advanced security practice into established clinical workflows, automate outdated routines, drive new collaborations and close the loop through integrations with security enforcement and incident response systems.
Medigate’s industry-leading innovation lies in how the platform is:
– Healthcare Centric: With its 100% healthcare focus and deep domain expertise of more than two million medical devices, engineering clinical workflows, identification of use cases and technology development, Medigate’s team evaluates data and protocols to create customized solutions for hospitals.
– Granularity of Discovery/Profiling. Medigate is the only platform that uses deep packet inspection to identify thousands of devices and decode over 85 proprietary healthcare IoT protocols, for greater insight into network communication profiles.
This includes:
– Clinical-contextual Risk Management Framework and Integrated Threat Intel
Communication policy recommendations out of the box
– Robust Technology Integrations: R&D exceeds standard surface-level integrations with NAC, firewall, SIEM, vulnerability management and network administration products, and clinical asset management systems.
– Utilization metrics used by operational stakeholders
How we are different
As we move into 2021 and beyond, Medigate’s mission is to help healthcare delivery organizations (HDOs) more quickly recover from the challenges of COVID-19. And as HDOs adjust to new care delivery paradigms that prioritize remote care and telehealth, Medigate will play a pivotal role in helping IT leaders develop and maintain proper connected-medicine security protocols to ensure effective, safe, and patient-centered care.
Specifically, Medigate differentiates itself from competitors through its unique, healthcare-centric expertise. The Medigate platform is currently integrated with over 600 facilities worldwide and provides insights and capabilities that allow decision-makers to employ data-validated processes to their most pressing concerns– whether that’s securing devices on the hospital network or locating missing assets needed for patient care. No matter a health delivery organization’s (HDO) priority, Medigate is able to seamlessly enjoin workflow and security to work alongside clinicians and hospital staff, rather than hinder their progress.
As an example of these capabilities, a new customer was ready to submit a $1.7M purchase order for medical equipment in preparation for the influx of patients. After deploying Medigate, they confirmed they had the needed equipment, not visible through the former manual inventory processes and averted an unnecessary spend. As another example, Torrance Memorial Hospital deployed the platform to contend with Urgent/11 vulnerabilities. Using Medigate, Torrance was able to develop and implement strategies based on potential risk to patients, including these insights:
- 19% more connected medical devices were discovered and profiled than estimated;
- 26% more non-medical IoT devices were discovered and profiled than estimated;
- Consistent with Medigate's claims, device profiles included make, model, MAC and IP addresses, serial number, location, status and security posture.
- Notably, firmware-level-details, including configuration-specifics such as OS and application versions were provided;
- In addition to Urgent/11 questions, vulnerabilities across Torrance Memorial's entire connected inventory were identified and remediation recommendations implemented.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

