Photo Gallery
 |
 |
NC Protect

Additional Info
| Company | Nucleus Cyber |
| Company size | 10 - 49 employees |
| Website | https://www.nucleuscyber.com |
NOMINATION HIGHLIGHTS
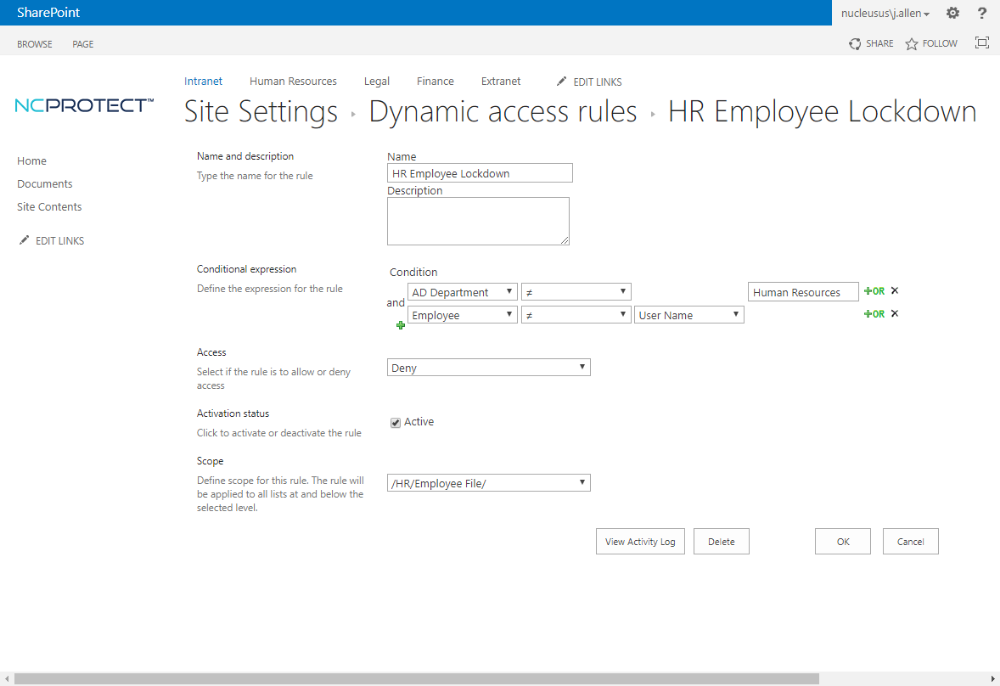
NC Protect is both content and context aware to automatically find, classify and secure unstructured data on-premises, in the cloud and in hybrid environments. It protects against breaches, sensitive data misuse and unauthorized file access enabling enterprises to fully take advantage of the intelligent workplace. NC Protect dynamically adjusts file security based on real-time comparison of user context and file content to make sure that users view, use and share files according to organizational regulations and policies.
With NC Protect enforce compliance and data security policies for privacy and confidentiality, intellectual property and trade secret protection, data loss prevention, enterprise social communications, PII and PCI compliance, HIPAA requirements, and other governance factors. It ensures data compliance and security by continuously monitoring and auditing data and documents against regulatory and corporate policies to protect against data breaches, unauthorized access and misuse.
NC Protect augments access controls using the unique identity a file builds over time from the moment it is first saved, with its content, name, authorship and date stamps. Through its lifecycle it gains additional transient context such as the file location or information repository, and classification levels. Real-time access controls reflect the user’s current context, blending traditional user permissions with granular business information such as security level or project team. Additionally, NC Protect leverages transient context such as location, IP address, device, browser or time of day.
The platform is fully integrated with Microsoft Office 365, SharePoint, files shares and more. It works natively with Microsoft products to restrict the use of certain Microsoft functionality, including elements of the SharePoint user interface, an application’s methods for viewing files, and encryption or restriction of attachments sent through Exchange Email. It requires no additional client-side application, reducing IT overhead and the risks involved in implementing new cloud services or BYOD policies.
How we are different
• NC Protect offers a centralized and cost-effective AI-driven data security solution to ensure compliance with regulatory and corporate policies and protect against breaches to mitigate risk.
• NC Protect takes an organizations’ data security policies and enforces them for each and every user and device and is completely transparent to the end user for a seamless security and user experience.
• With NC Protect, IT administrators can manage user access without creating more security groups, complex permissions sets, more collaboration sites, libraries or folders. Instead, IT administrators define access rules and usage rights to efficiently and dynamically control access and user actions.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



