Photo Gallery
 |
 |
PassiveTotal

Additional Info
| Company | RiskIQ |
| Company size | 150 employees |
| Website | http://www.riskiq.com |
NOMINATION HIGHLIGHTS
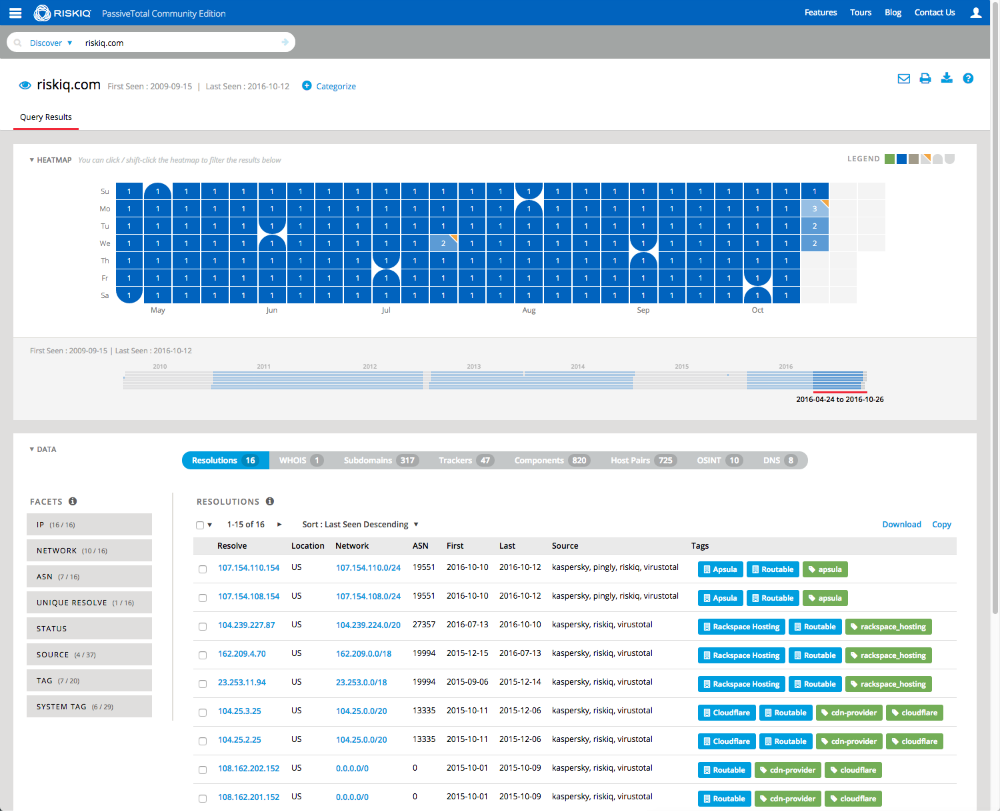
PassiveTotal uses vast data sets and predictive analytics to automate investigative processes to keep pace with the shifting threat landscape. Over 13,000 analysts, many from Fortune 500 companies, use it to pivot between data relationships to gain the offensive edge against an attacker by preventing their next move.
PassiveTotal automatically aggregates and correlates data about a security event that would otherwise take an analyst days or hours of manual analysis. Multiplying the force of each analyst gives junior analysts the ability to fulfill the output of a senior analyst. In fact, 100% of 320 surveyed PassiveTotal users reported that they save at least 1-3 hours a week by using the platform to collect data.
The platform includes data from passive DNS, email, SSL certificates, host pairs, web trackers, WHOIS, and comprehensive RiskIQ proprietary web crawling. This ever-expanding data provides new context to adversaries’ infrastructure. Of 320 surveyed PassiveTotal users, 84% find PassiveTotal more comprehensive than other security data sources.
With PassiveTotal, security teams can be alerted, in real-time, to changes in DNS and domain resolution via a heat map feature, WHOIS registration, and the appearance of other new keywords of interest. The latest release also includes a project workflow to quickly organize and group related threat infrastructure components found during investigations, which allows research teams to collaborate in their investigations.
With PassiveTotal, security teams can proactively address additional threats that are related to already observed events or alerts. The platform does this by uncovering other infrastructure associated with a bad actor that might be previously unknown or difficult to associate. Security teams can block these connected sources, and set up monitors to alert on changes to that infrastructure that could indicate an impending attack. Of 320 surveyed PassiveTotal users, 95% did not have full visibility into attack infrastructure before PassiveTotal.
How we are different
For over 13,00 users, PassiveTotal simplifies and accelerates event investigation and intelligently consolidates and analyzes data from multiple data sources into a single pane of glass. The world-class platform addresses a larger number of threats in less time than the traditional manual processes employed by investigators. The data that PassiveTotal aggregates and correlates is routinely used by analysts in investigations and can be integrated into other security platforms. Additionally, PassiveTotal supports out-of-the-box integrations with Splunk, QRadar, Maltego, and Phantom, with new integrations being regularly developed
One of the unique capabilities that sets PassiveTotal apart is its ability to alert analysts of infrastructure changes based on collected data sets and most recent scans. PassiveTotal has continued to build on this monitoring framework and now supports a new range of query types focused on newly observed host domains and WHOIS registrant data. PassiveTotal is the only platform in which users looking to monitor specific indicators or keywords can be alerted when changes are detected.
One of the primary byproducts from infrastructure analysis is almost always a set of indicators that tie back to a threat actor or group of actors. For years, PassiveTotal has provided analysts with tools to classify or tag infrastructure items. Now, it's the only platform offering full collaboration in threat hunting in the form of "projects," which give users the option to create public or private projects with names, descriptions, collaborators, and monitoring profiles. Visiting a project’s details shows a listing of all associated artifacts and a detailed history that retains all the context needed for one analyst to pick up where another left off. Threat actor profiles can be built within PassiveTotal and serve as a “living” set of indicators. As new information is discovered or found, it can be added to that project.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



