Proofpoint Insider Threat Management
Recognized in the Category:
Photo Gallery
 |

 |
Proofpoint Insider Threat Management

Additional Info
| Company | Proofpoint |
| Company size | 1,000 - 4,999 employees |
| Website | https://www.proofpoint.com/us |
NOMINATION HIGHLIGHTS
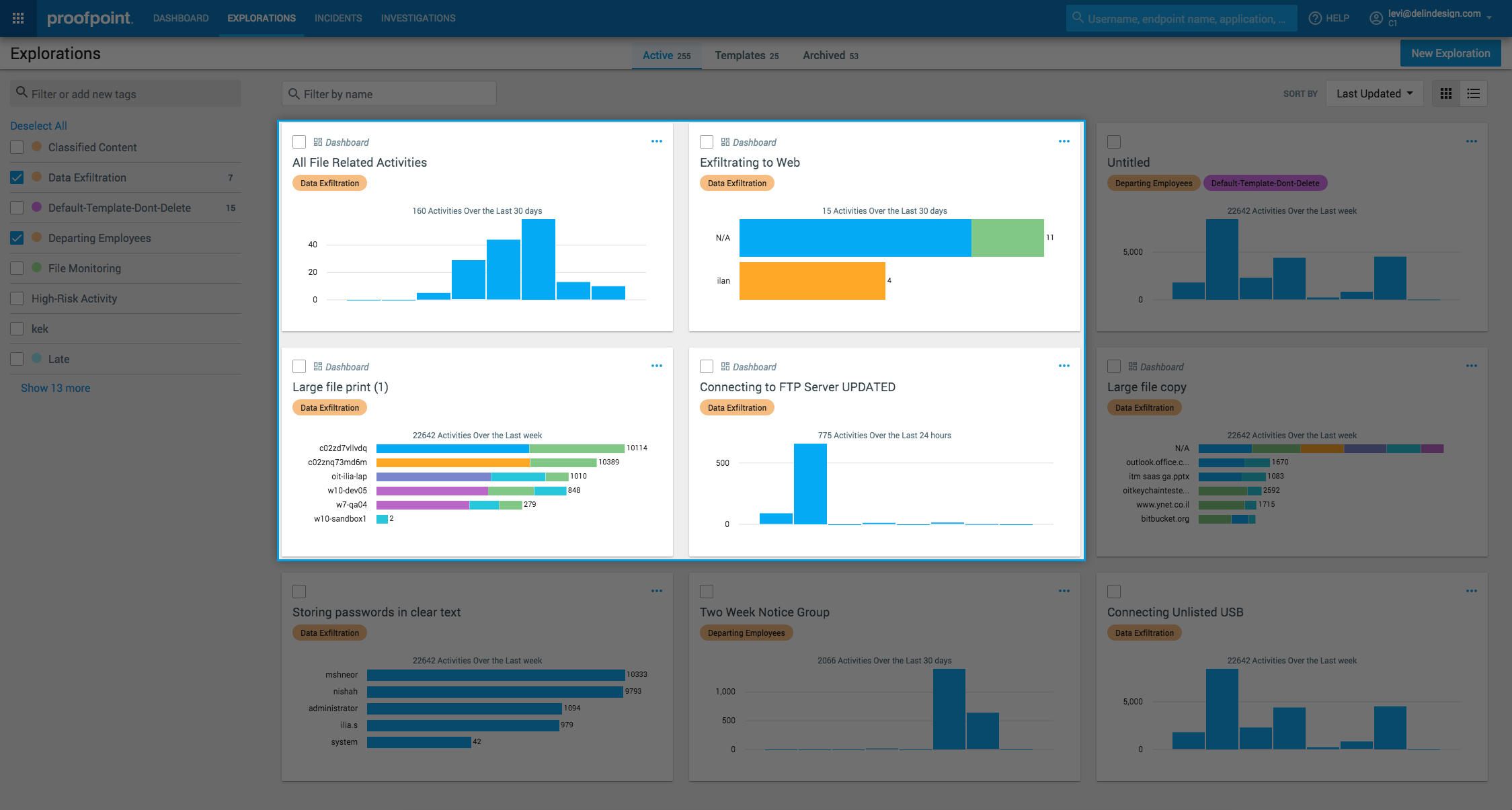
The powerful forces of the cloud and mobility have spurred greater collaboration and more distributed workforces. At the same time, the 2020 Verizon DBIR report found that 30% of all data breaches involved an insider. Proofpoint Insider Threat Management (ITM) provides the leading insider behavior and analytics solution with more than 1000 customers globally. We help organizations protect against data loss, malicious acts, and brand damage involving insiders acting maliciously, negligently, or unknowingly.
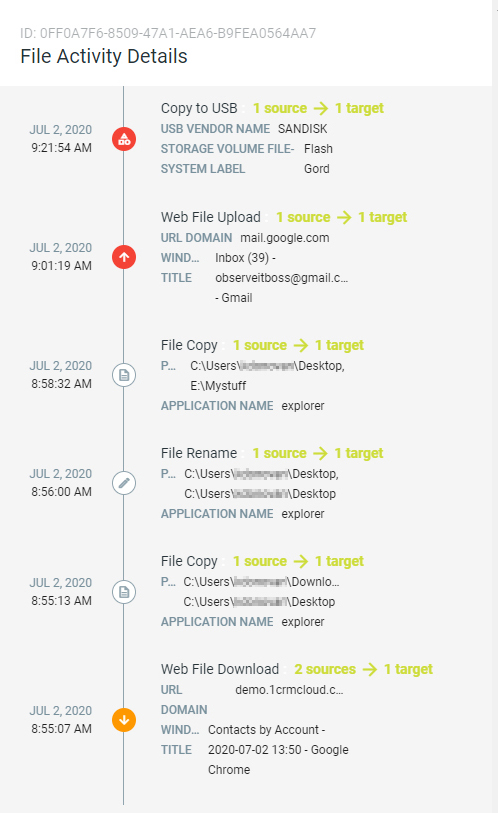
ITM correlates user behavior and data movement that empowers security teams to detect, investigate, and respond to potential insider threats by delivering real-time alerts, contextual intelligence on users, data and threats and easy to understand evidence of wrongdoing.
ITM delivers five key capabilities necessary for managing risky behavior on the endpoint:
1. Deliver visibility and context on user behavior and data activity
2. Detect and alert on risky user behavior and data interaction in real time.
3. Accelerate incident response and investigations
4. Simplify deployment with a pure SaaS platform and lightweight endpoint agent architecture
5. Protect user privacy unless clear and obvious evidence of wrongdoing
How we are different
- Rapid time to value: Proofpoint ITM collects its own telemetry on user activity across applications, files, data, servers, desktops and applications, whether the applications are hosted in the cloud, on the endpoint or on-premises. This provides visibility as soon as the data is collected, which can be trusted coming from one source. Instead, most legacy UEBA solutions take months to provide visibility. They don’t collect any telemetry, instead relying on the integrity of the data through integrating with other technologies.
- Real-world insider threat detection: Proofpoint ITM detects risky insider behavior across unauthorized activity and access, risky accidental actions, system misuse and out of policy data movement. We use out of the box and easily customizable rules based on the expertise of 1000+ customers and research institutions such as CERT Insider Threat division, NIST and NITTF. In comparison, legacy UEBA solutions mostly focus on finding anomalies from normal behavior, which lead to significant false positives and lost security team time.
- Context: Instead, Proofpoint ITM correlates all activity by user and visualizes in an activity timeline. In effect, we paint a clear picture of the context of “who, what, where, when and why” that is understood by cybersecurity and non-cybersecurity teams alike, without any jargon. In comparison, due to the reliance on other technologies for visibility, legacy UEBA solutions often have gaps in visibility when it comes to investigating specific incidents or alerts.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



