Photo Gallery
 |
Proofpoint Insider Threat Management (ITM)
Additional Info
| Company | Proofpoint |
| Company size | 1,000 - 4,999 employees |
| Website | https://www.proofpoint.com/us |
NOMINATION HIGHLIGHTS
With the transition to remote work, visibility to user and data activity on the endpoint has become an imperative for security organizations. A survey conducted by Ponemon in 2021 found that 26% of data breaches involved a malicious insider. Proofpoint provides the leading Insider Threat Management (ITM) solution with more than 1000 customers globally. We help organizations protect against data loss, malicious acts, and brand damage involving negligent, malicious and compromised insiders.
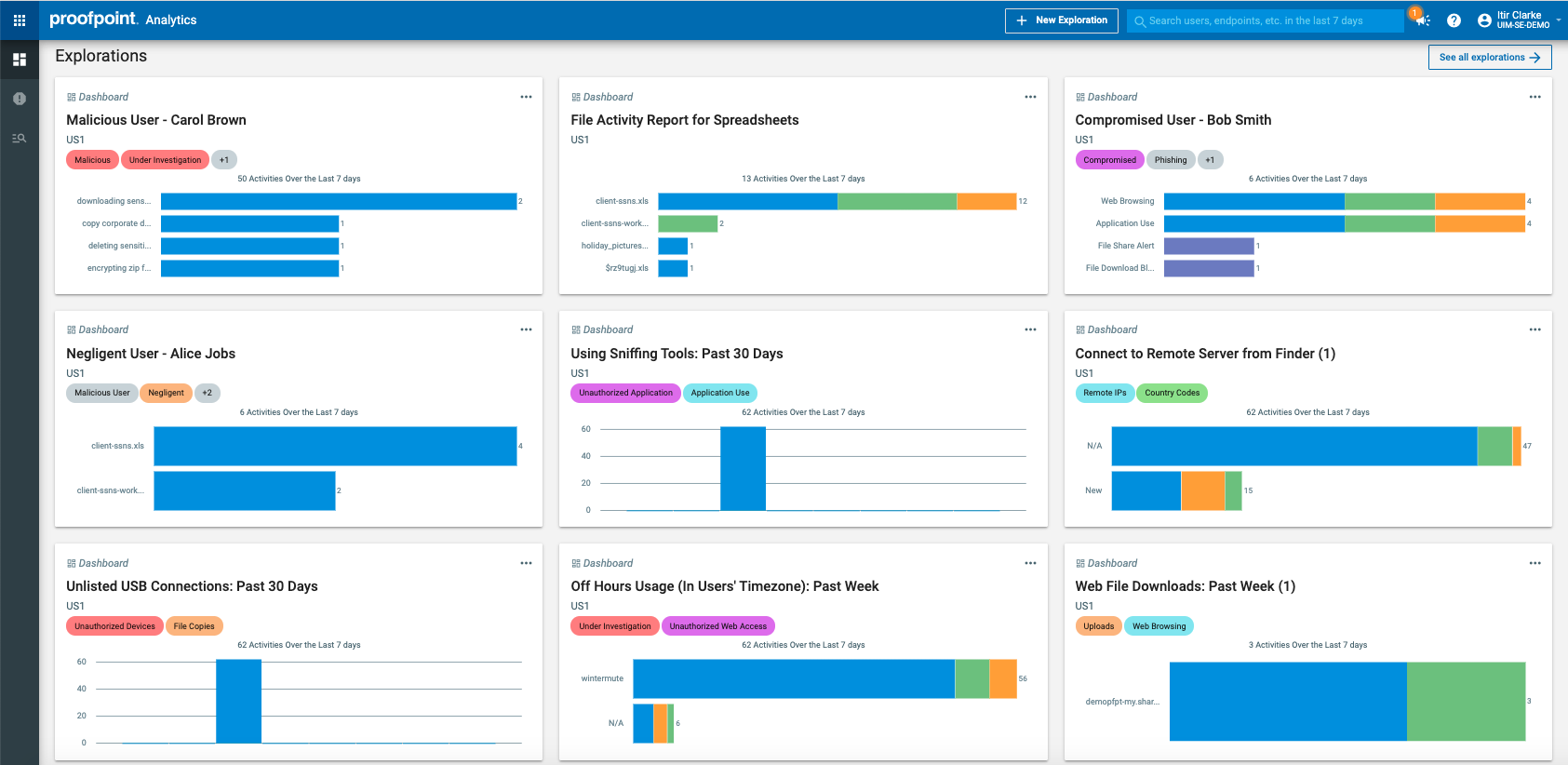
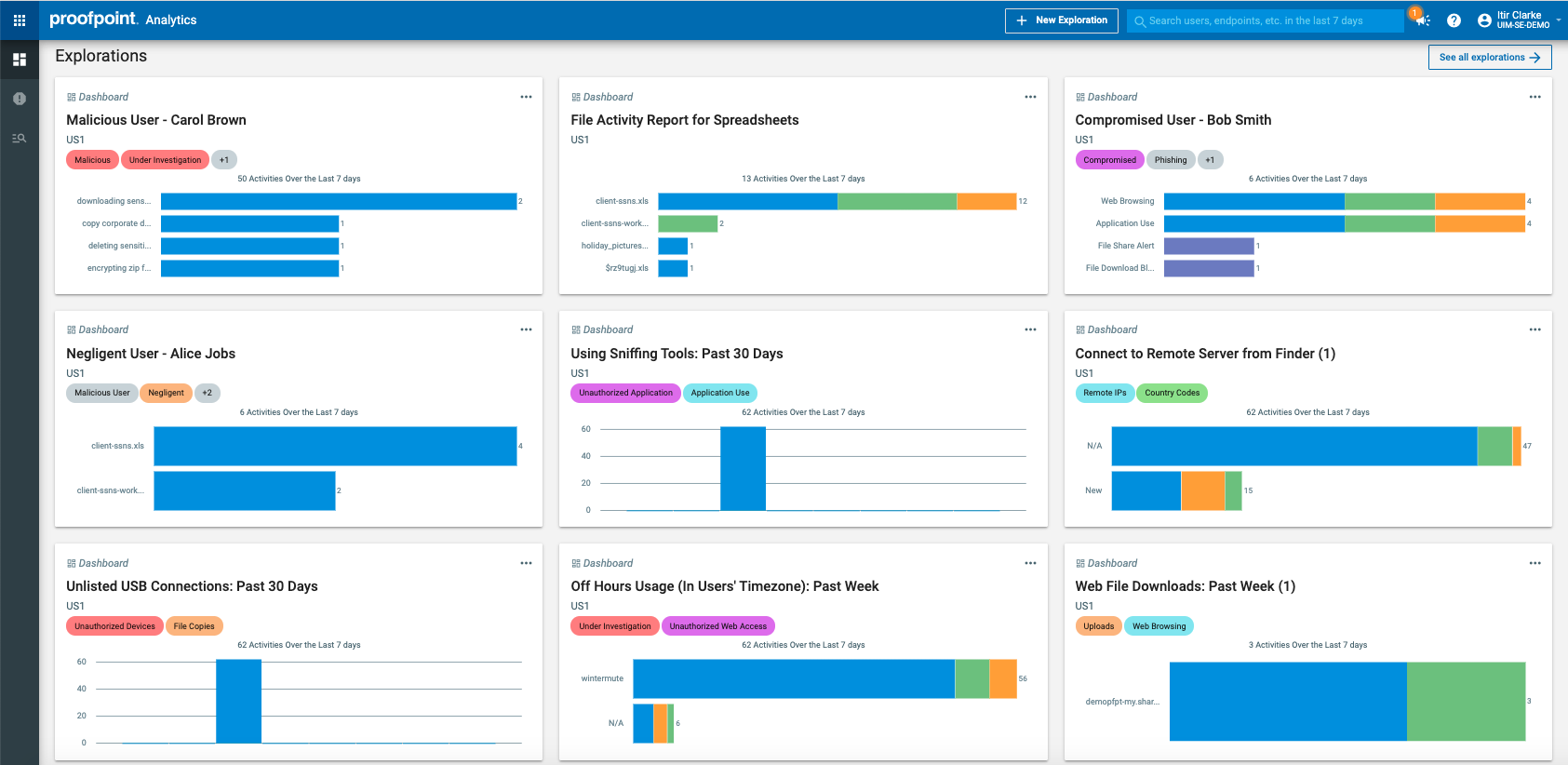
ITM correlates user behavior and data movement that empowers security teams to detect, investigate, and respond to potential insider threats by delivering real-time alerts, contextual intelligence on users, data and threats and easy to understand evidence of wrongdoing.
ITM delivers six key capabilities necessary for managing risky behavior on the endpoint:
Deliver visibility and context – user behavior, file activity and file content in a clear timeline
Detect and alert on risky user behavior and data interactions in real time
Prevent data loss through common endpoint channels such as print, cloud synch folders, USB connected devices, etc.
Accelerate incident response and investigations
Simplify deployment with a pure SaaS platform and lightweight endpoint agent architecture
Protect user privacy unless clear and obvious evidence of wrongdoing
How we are different
● Rapid time to value: Proofpoint ITM collects its own telemetry on user activity across applications, files, data, servers, desktops and applications, whether the applications are hosted in the cloud, on the endpoint or on-premises. This provides visibility as soon as the data is collected, which can be trusted coming from one source. Instead, most monitoring solutions are focused on specific technologies, requiring more manual work for security teams. Or they require integrations with many other technologies to provide any visibility, which creates unclean and noisy telemetry.
● Real-world insider threat detection and endpoint data loss prevention (DLP): Proofpoint ITM detects risky insider behavior across unauthorized activity and access, risky accidental actions, system misuse and out of policy data movement. We use out of the box and easily customizable rules based on the expertise of 1000+ customers and research institutions such as CERT Insider Threat division, NIST and NITTF. ITM also prevents sensitive data exfiltration through common endpoint channels such as USB connected devices, print, cloud synch folders, etc. We detect sensitive data using out-of-box data classifiers and Microsoft Information Protection sensitivity labels. In comparison, most monitoring solutions simply create logs and have rudimentary insider threat detection capabilities.
● Context: Proofpoint ITM correlates all activity by user and visualizes it in an activity timeline. In effect, we paint a clear picture of the context of “who, what, where, when, and why” that is understood by cybersecurity and non-cybersecurity teams alike, without any jargon. You can search through security events with keywords and filters across all the collected metadata and screen captures. The sophisticated analytics, role-based workflows and reports accelerate investigations and response. Security monitoring solutions provide logs on the collected activity, while leaving the correlations and analysis to the manual efforts of the security teams.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



