Randori — Authentic, Automated Attack Platform
Recognized in the Category:
Photo Gallery

|


|
Randori — Authentic, Automated Attack Platform

Additional Info
| Company | Randori |
| Company size | 10 - 49 employees |
| Website | https://www.randori.com/ |
NOMINATION HIGHLIGHTS
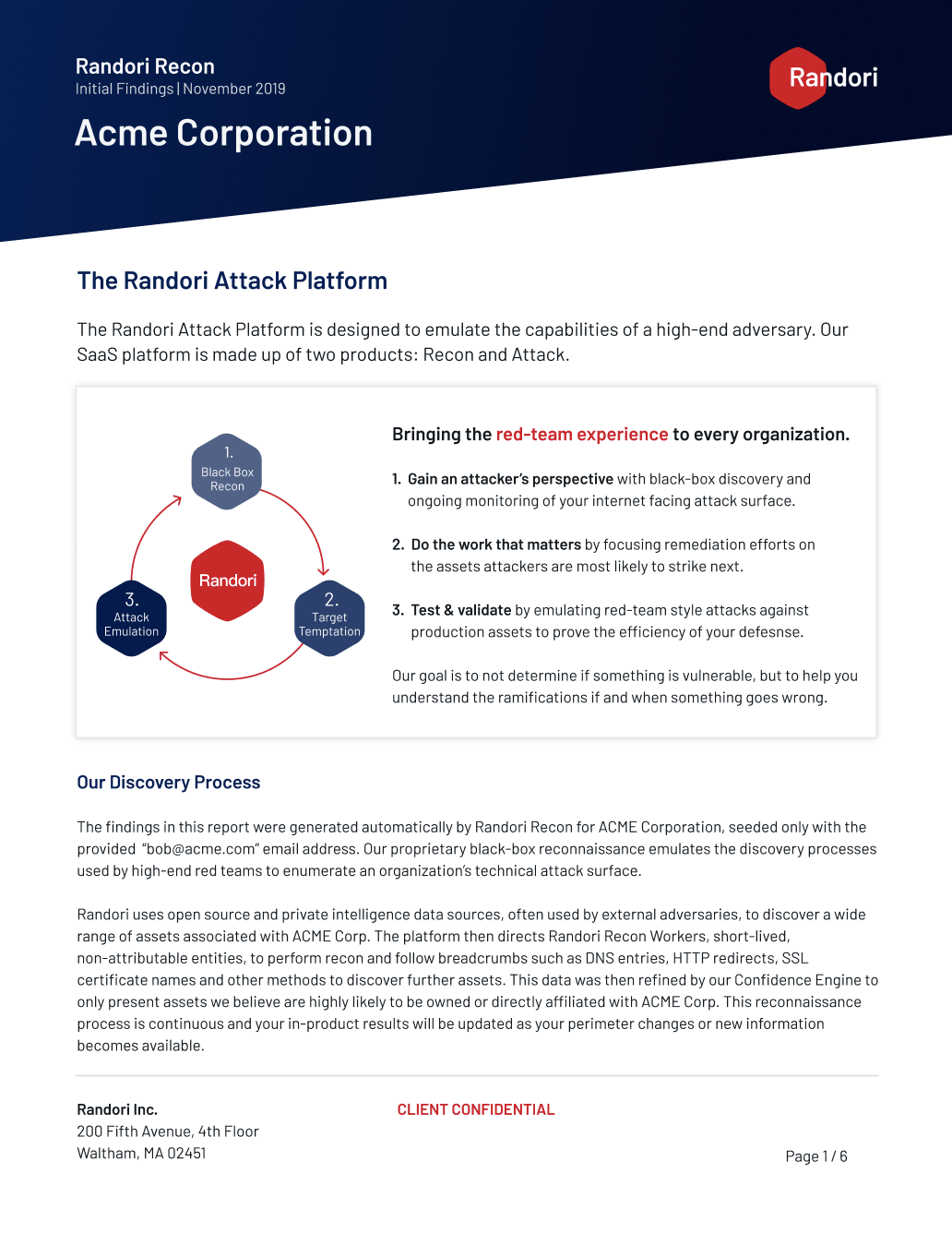
Randori’s mission is to build the world’s most authentic, automated attack platform, to help security teams “train how they fight”. Founded in 2018 by a former Carbon Black Executive and leading red teamers, Randori provides a SaaS platform to allow security teams of all maturity to spar against an authentic adversary. Customers are testing their incident response, identifying weaknesses (not just vulnerabilities), and as a result, producing justifiable ways to ask for further investment.
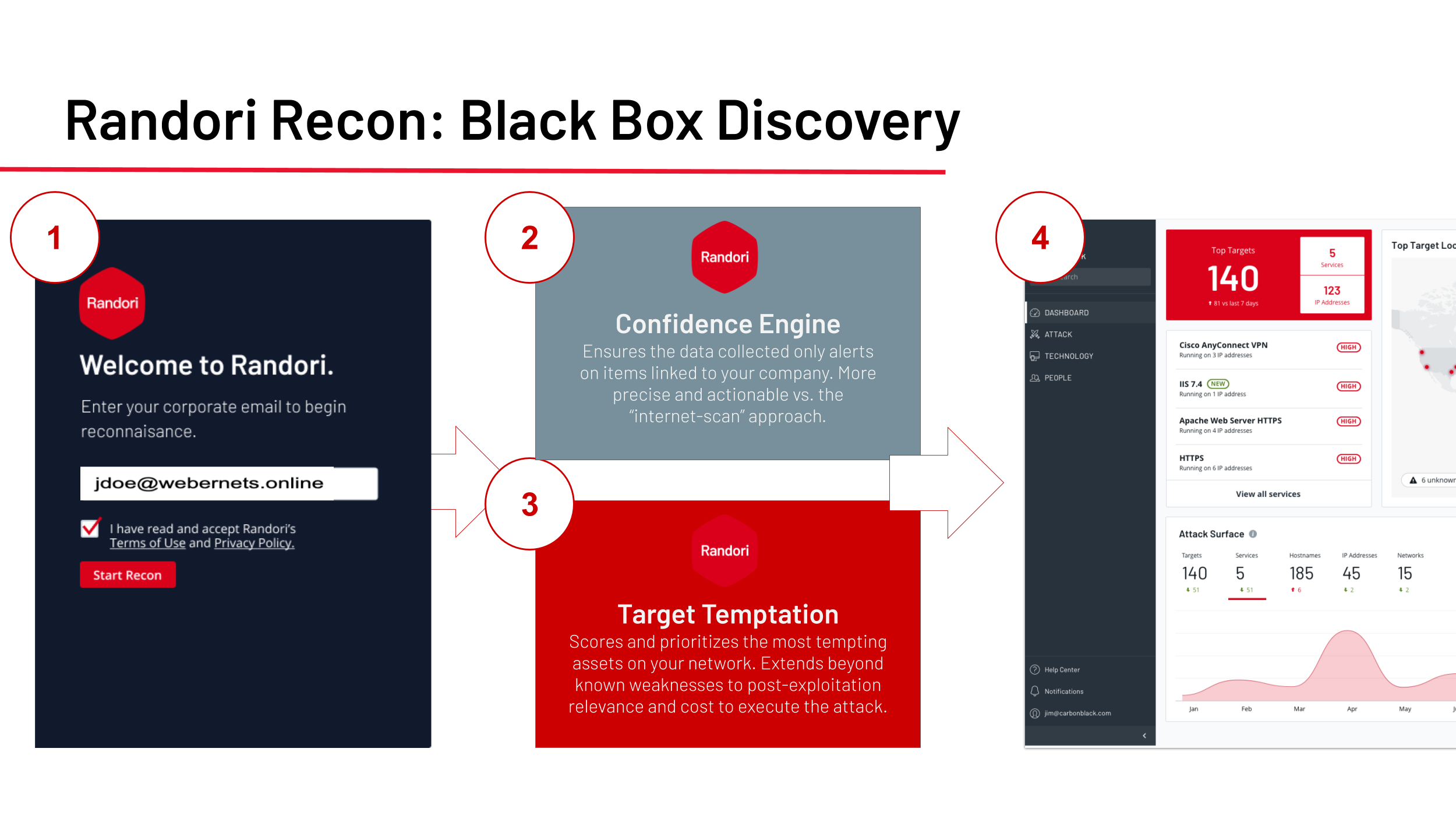
The Randori platform consists of two products, Recon and Attack. Recon provides comprehensive attack surface management powered by black-box discovery. Customers can “see” how attackers perceive their company from the outside. This is especially useful for enterprise organizations with a changing network footprint, such as M&A, high seasonality, or undergoing cloud migration. Their approach differs from “internet-wide scan” methods, which can produce false-positives and are not actionable. Recon results are prioritized using a Target Temptation engine, which takes into account factors like known weaknesses, post-exploitation potential, and the cost of action by an attacker. Recon is available for free trial; a complimentary Recon report can be provided to any company over 1000 employees.
Attack provides authentic adversary emulation across all stages of the kill chain. Customers choose from objective-based runbooks that the platform will use to gain initial access, maintain persistence, and move laterally across the network. Risk is assessed across vulnerabilities, misconfigurations, and credentials—the same ways attackers breach companies. Attack is available to select early access partners and will broaden access in 2020.
How we are different
• No configuration or setup: You only need to provide a single email address to discover your entire Internet-facing attack surface. No agents or configuration required.
• Authentic attacker mindset: The Randori platform is built on technology used to penetrate some of the world’s largest, most secure businesses. The platform seeks not to “validate existing controls” or “detection of MITRE ATT&CK techniques”, but help security teams train against a real adversary.
• Continuous and evolving: As new tempting targets surface across your network, you’ll get automatic notifications that can integrate with your existing security stack. As the Randori platform expands, its Target Temptation prioritization model and Attack runbooks continue to expand in-line with new adversary trends.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

