Photo Gallery
|


|
Rapid7 InsightIDR
Additional Info
| Company | Rapid7 |
| Company size | 850 employees |
| Website | http://www.rapid7.com |
NOMINATION HIGHLIGHTS
Historically, incident detection and response solutions require security professionals to parse through hundreds of trivial alerts, manage an ever-growing mountain of data, and manually forward information from endpoints. In addition, these antiquated detection tools require investigators to have both log search expertise and incident response experience in order to retrace user activity across the network, endpoint, and cloud.
In February 2016, Rapid7 launched InsightIDR to specifically solve these problems, giving security professionals the visibility and confidence they need to move with purpose when suspicious activity is detected.
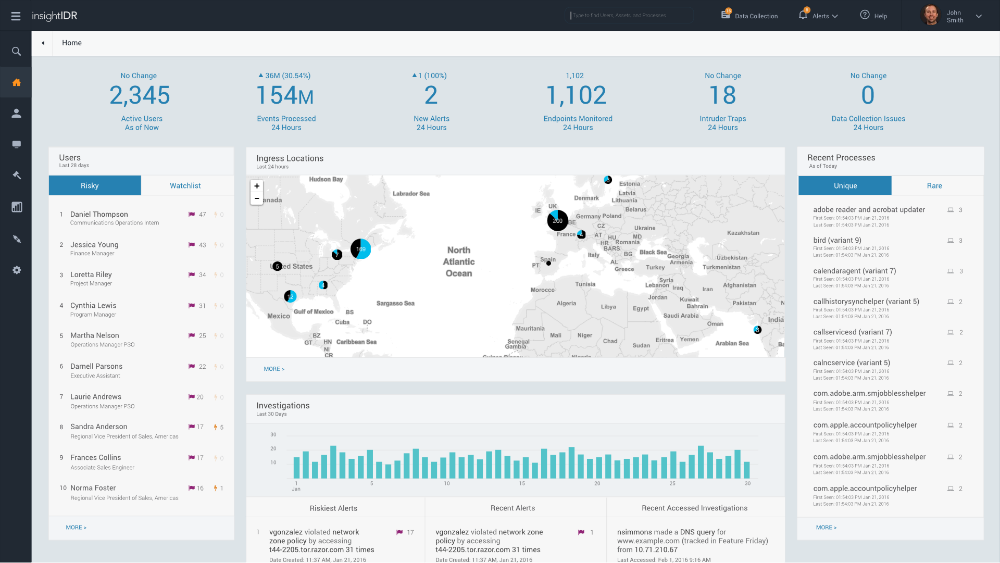
InsightIDR helps find unknown threats with User Behavior Analytics (UBA) and automated deception technology, provides SIEM capabilities to prioritize where to look, and combines the above with Endpoint detection and visibility to leave attackers with nowhere to hide. Customers report that their investigations are 20 times faster, as they can bring together real-time log search, user activity, and endpoint data in a single solution.
InsightIDR, running on a unique multi-tenant cloud architecture, comes with pre-packaged analytics and incident detections to deliver insight quickly. Security professionals are able to spend less time managing their security data, benefiting from fast search, constantly updated detections and the comfort that their log data is outside the hands of attackers.
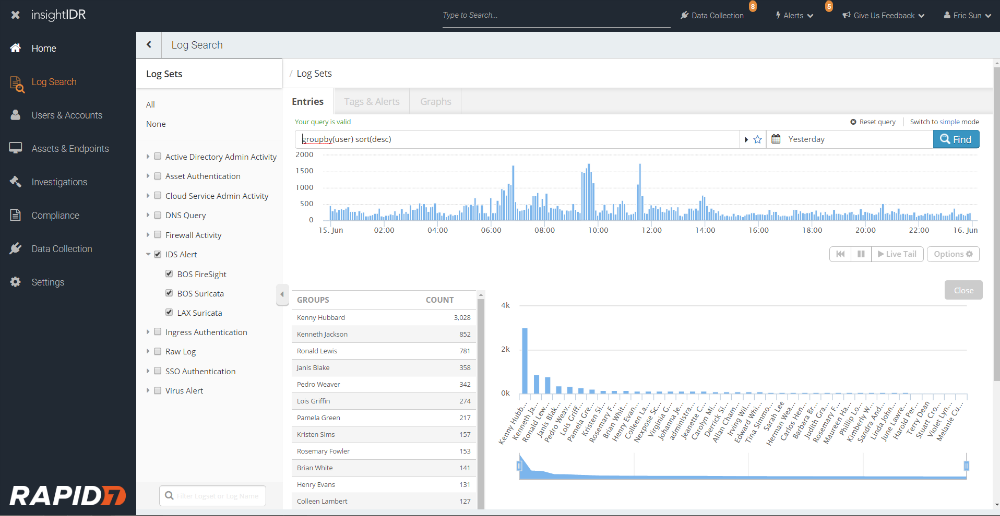
InsightIDR prioritizes where to hunt threats without a data degree. Traditional log search platforms waste time and money, requiring teams to manually retrace user activity across IP addresses, endpoints and cloud services. InsightIDR provides a complete record of relevant, contextualized behavior. No more writing queries or hiring certified data splunkers — InsightIDR reveals the answers hidden in user activity, logs, and endpoints.
How we are different
While everyone knows that security teams are strained, the vast majority of today’s solutions fail to ease the pressure on these teams. The solutions still generate vague, un-prioritized alerts, involve complicated deployments and tuning, and require customers to maintain a growing hardware farm. InsightIDR is able to help stressed teams the following ways:
●More than 60 percent of organizations get more alerts than they can feasibly investigate. Instead of alerting on every anomaly, InsightIDR comes with meaningful context and highlights network happenings the security teams want to know about. Not to mention that InsightIDR runs on a native cloud architecture, comes pre-built with incident detection, and takes around four hours to set up.
●Not all signs of the intruder are found in log files, which is where most SIEM and UBA solutions derive their alerts. InsightIDR also comes with automated deception technology tools – including Honey Pots, Honey Users, and Honey Credentials, built to reliably detect intruders earlier in the attack chain, before data is stolen.
●To date, InsightIDR has already helped companies and has the potential to help many more. One user, Tom Brown, IT Manager at Liberty Wines, noted the following: “Until InsightIDR was launched there really wasn’t anything on the market that could easily scale from an SME like us right up to a large Enterprise deployment… It’s a great system. It gives you that warm feeling inside by catching any suspicious behavior on the network months before you’d otherwise discover it. Most IT managers accept that something will get through – that there will be a hole somewhere. So it’s about finding out where it is quickly and being able to take action and that’s what InsightIDR gives you.”


