Recorded Future Cyber
Photo Gallery
 |
 |
Recorded Future Cyber


Additional Info
| Company | Recorded Future |
| Website | https://www.recordedfuture.com |
| Company size (employees) | 51-200 |
| Type of solution | Software |
Overview
Relevant and actionable threat intelligence updated in real time: Recorded Future technology harnesses the power of machine learning and natural language processing to analyze and visualize intelligence on emerging cyber threats, tactics, and indicators of compromise. Our patented Web Intelligence Engine continually analyzes the open, deep, and dark web across all languages.
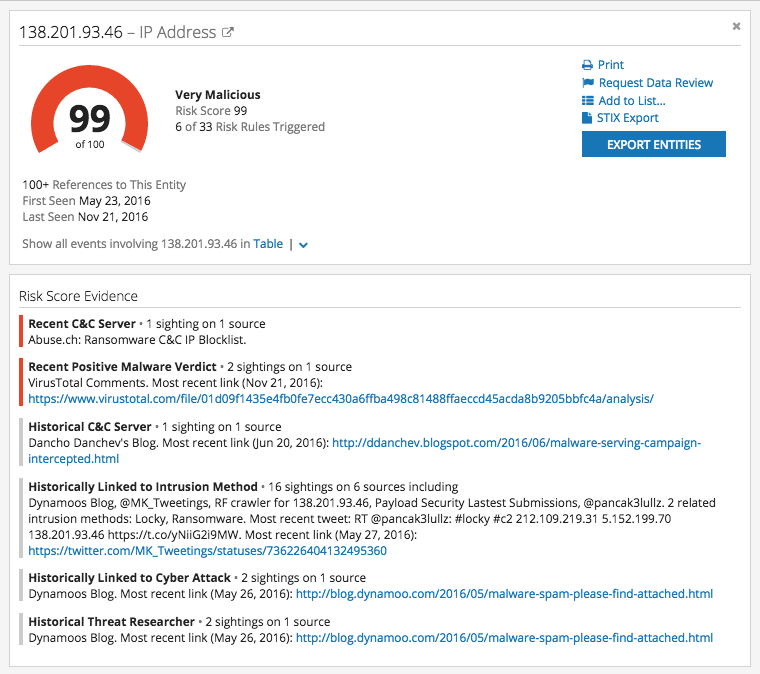
Consolidated view to increase analyst efficiency: Recorded Future Intel Cards present real-time threat intelligence in a single view, unifying thousands of data points — analysts gain instant context on associated methods or targets, with one click in their web browser.
Risk scoring to prioritize threats: Recorded Future risk scores enable analysts make fast and evidence-based security decisions. Risk rating increases based on evidence analyzed by the Web Intelligence Engine. For example, an IP address could be reported as command and control for malware; a hash could be the MD5 value of a malicious file; or a vulnerability “exploited in the wild.”
Additionally, we are continually enhancing our offering in these three areas:
1. Breadth of coverage: Our automated engine has already indexed over 20 billion (yes, “billion”) data points from the open, deep, and dark web, across all languages. Our engine continually analyzes new threat sources.
2. Relevancy of intelligence: Our data science team is continually enhancing our machine-learning and natural language processing (NLP) algorithms and cyber ontologies to ensure customers get more relevant intelligence to act quickly and confidently. See more: https://www.recordedfuture.com/web-intelligence-engine/.
3. Integration with existing security: Customers must be able to apply threat intelligence to their existing security products to get more out of them. Our current technology partners include Palo Alto Networks, Splunk, IBM, and smaller security vendors. We are continually expanding our technology partner ecosystem: https://www.recordedfuture.com/integrations/.
How we are different
Our customers are gaining measurable value from our real-time threat intelligence. Here are three metrics reported by our customers:
• 86% of the Fortune 100 uses Recorded Future
• 10x Productivity Gain From Real-Time Threat Intelligence for SIEMs
• 63% reduction in malicious traffic



