Photo Gallery

|
|
ReSecure Endpoint

Additional Info
| Company | ReSec Technologues |
| Company size | 20 employees |
| Website | http://www.resec.co |
NOMINATION HIGHLIGHTS
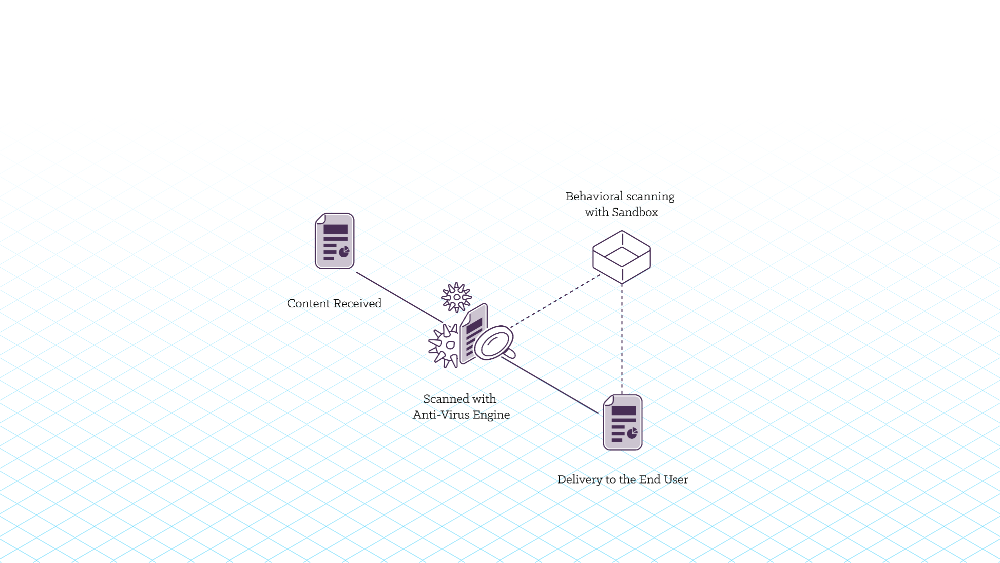
The ReSecure Endpoint patented solution is deployed directly on end-users’ computers and integrated with all common device control. Files that are loaded onto the endpoint from external devices (e.g., USB, mobile phone) are intercepted and sent directly from the external device to the ReSecure platform and threat-free replicas are placed back on the desktop or predefined folder.
The Content Disarm and Reconstruction (CDR) technology featured in ReSecure Endpoint works by breaking files into their individual components, removing all files that have not been whitelisted by the end user, and then creating an identical copy of the file to present to the end user, all in real time. ReSecure Endpoint protects users from both known and unknown threats because the CDR process uses a whitelist to filter out possible threats, only allowing approved content into the network. Users also have the ability to control the level in which they receive content because they set the whitelist parameters.
How we are different
• The CDR process happens in real time, as quick as an anti-virus scan, and can process thousands of files in just minutes. This keeps the flow of productivity in the workplace and ensures that everyone is able to compete their job securely and safely.
• Through a highly automated process, the ReSecure Endpoint solution allows for easier user interaction with the solution compared to many traditional security products. This allows a company’s security and IT professionals to focus on other pressing issues without having to worry about whether their endpoint security is keeping the company safe.
• Many organizations have been breached through the use of external devices connected to an organization's endpoint and, until now, organizations were only offered a blocking solution. ReSecure Endpoint enables organization to allow access to an external device’s information without compromising security. ReSecure can prevent these types of attacks because the technology relies on prevention, not detection. Instead, the solution proactively protects against both known and unknown threats through a whitelisting process that is set by the user.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

