Photo Gallery
 |

 |
Resecurity Context™
Additional Info
| Company | Resecurity |
| Company size | 50 - 99 employees |
| Website | https://resecurity.com |
NOMINATION HIGHLIGHTS
The appearance of new threats and security challenges requires effective tools for their timely identification and in-depth analysis.
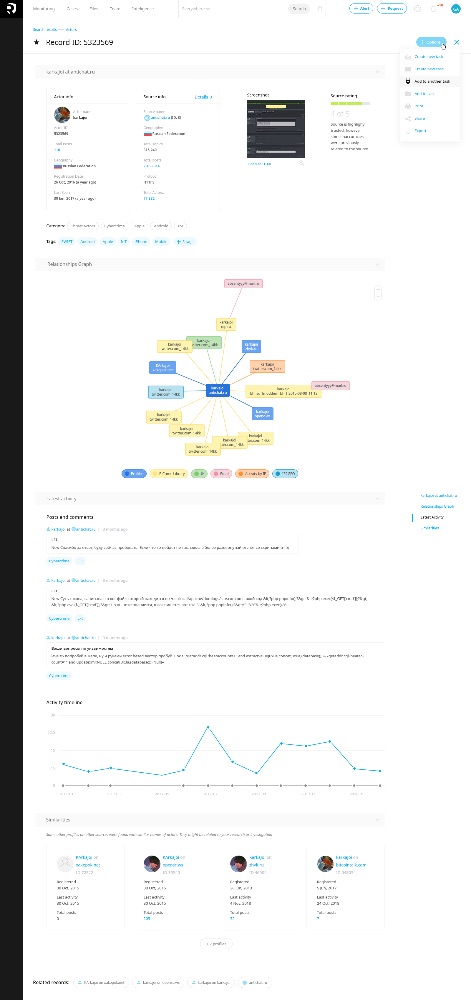
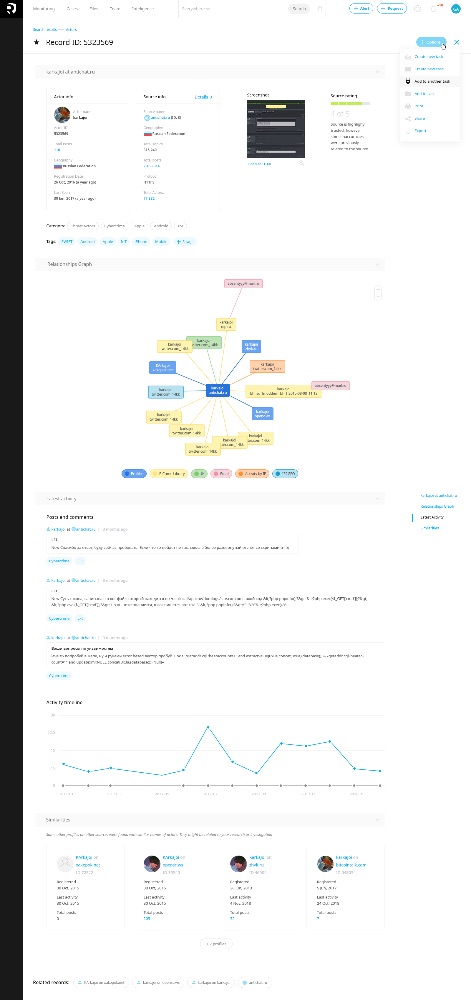
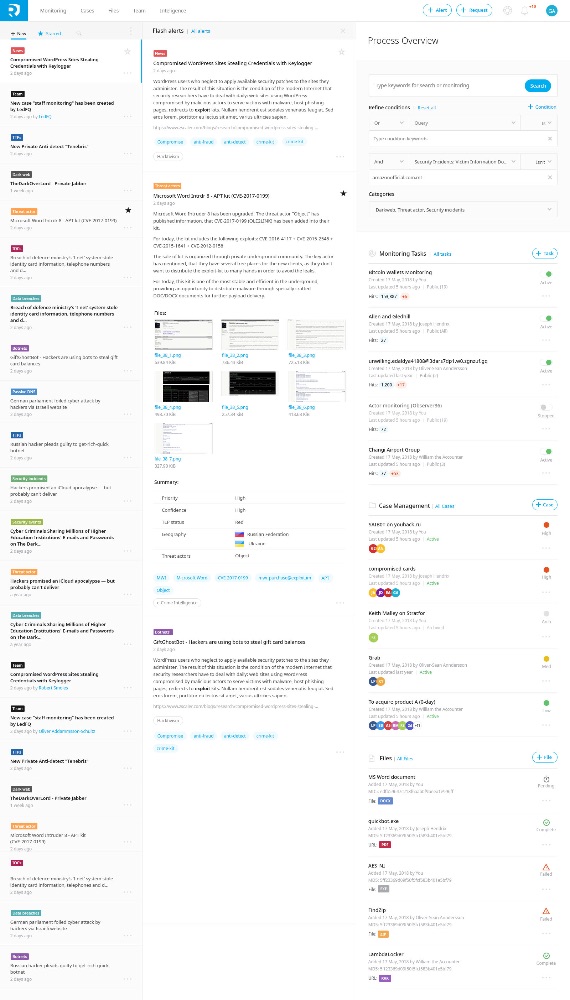
Resecurity Context™ – is a Cyber Threat Intelligence Platform (CTIP) enabling enterprises and governments to accelerate analysis, prevention and investigation workflows with the goal of discovering valuable insights, and supporting better decision-making using AI, data science and unique threat and risk intelligence streams coming from variety of data sources.
Too many organizations leverage advanced threat intelligence merely to detect indicators of compromise (IOCs). Resecurity wants to help them mine actionable threat intelligence to truly bolster enterprise defences.
IOC-based detection approach is a fundamentally flawed solution to the problem of stopping a sophisticated adversary, that’s why the industry needs advanced threat intelligence solutions providing comprehensive visibility into the actual threat landscape globally.
The product is oriented towards intelligence analysts, investigators, SOC/DFIR teams, cyber threat intelligence teams, risk management and C-level security executives.
The development of the product has been started 4 years ago based on the feedback and design requirements received from several leading Cyber Threat Intelligence Centers of Fortune 500 companies and government agencies.
The idea of the platform’s name – Context™ was born from an understanding of the vital role of contextualization in cybercrime investigations and threat
intelligence tasks. Without proper contextualization, an overload of raw intelligence can become a burden, leading to lack of actionable data and incorrect resource planning, which may increase the probability of risk and negative outcome.
Context™ helps to research the entire kill-chain by examining the source data (domain name, IP, threat actor, IOCs, malware artifacts, security incidents details) and produce enriched high quality intelligence reports with detailed historical contextual information, significantly speeding up the reaction time of security and threat intelligence teams.
How we are different
- Context™ is a Cyber Threat Intelligence Platform enabling enterprises to accelerate analysis, prevention and investigation workflows with the goal of discovering valuable insights, and supporting better decision-making.
-Context™ combines tactical, technical, operational and strategic threat intelligence and allows tracking of multiple subjects of interest (SOI) enabling definition of complex criteria. Context™ harnesses a constantly-expanding cloud of indexed threat artifacts and associated adversaries meta-data. Context™ helps to optimize time consuming operations on threat intelligence collection, processing, production, and dissemination (CPED) stages.
-Context™ leverages a broad arsenal of AI/ML mechanisms to provide the most relevant and adequate results.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



