Photo Gallery
|


|
RiskIQ PassiveTotal
Additional Info
| Company | RiskIQ |
| Company size | 100 - 499 employees |
| Website | https://www.riskiq.com/ |
NOMINATION HIGHLIGHTS
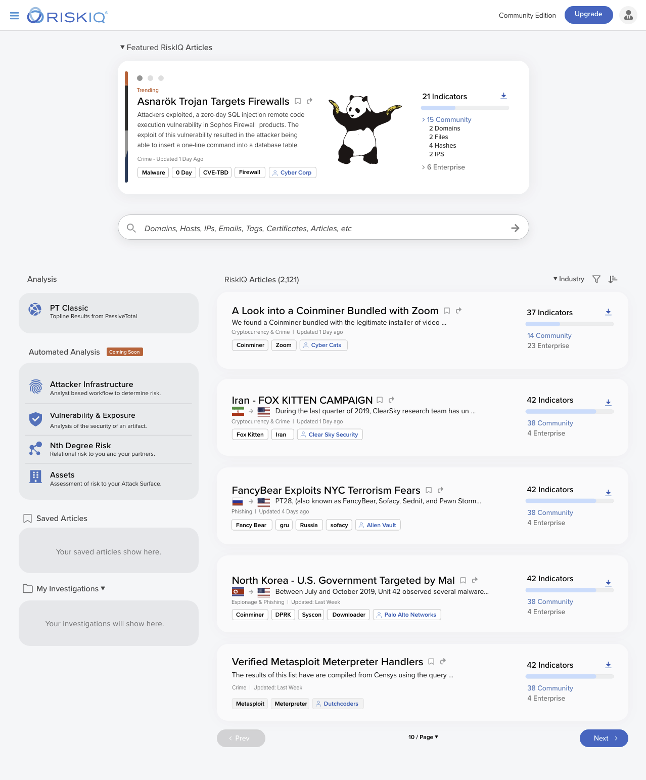
PassiveTotal provides access to the most comprehensive internet data sets available to map threat infrastructure and provide unparalleled context and intelligence to internal events and incidents, automatically aggregating and correlating data about a security event that would otherwise take an analyst days or hours of manual analysis.
For over 80,000 users, PassiveTotal simplifies and accelerates event investigation and intelligently consolidates and analyzes data from multiple data sources by connecting internal activity, event, and incident indicator of compromise (IOC) artifacts to what is happening outside the firewall—external threats, attackers, and their related infrastructure.
Of 320 surveyed PassiveTotal users, 84% find PassiveTotal more comprehensive than other security data sources.
PassiveTotal provides access to:
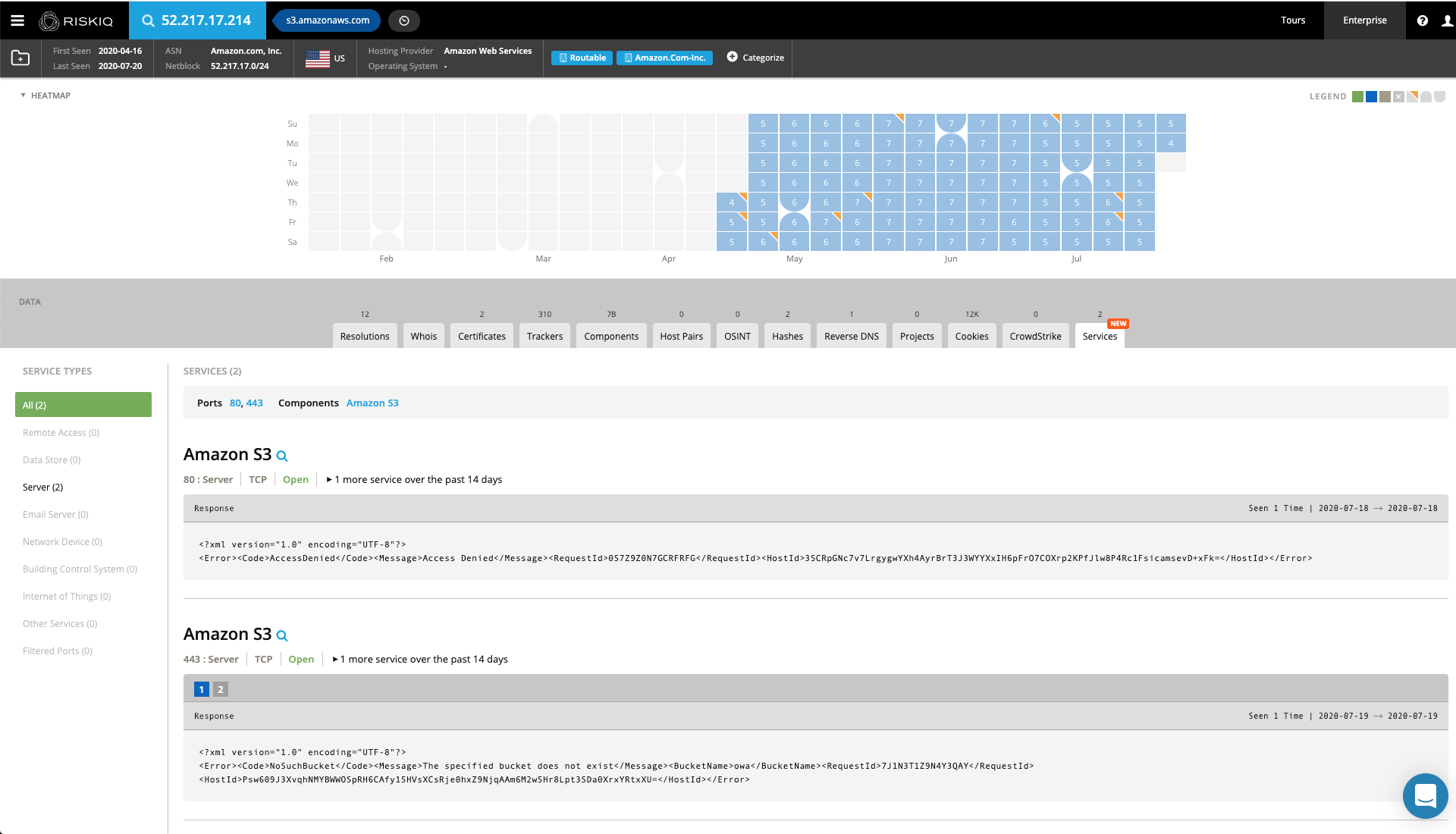
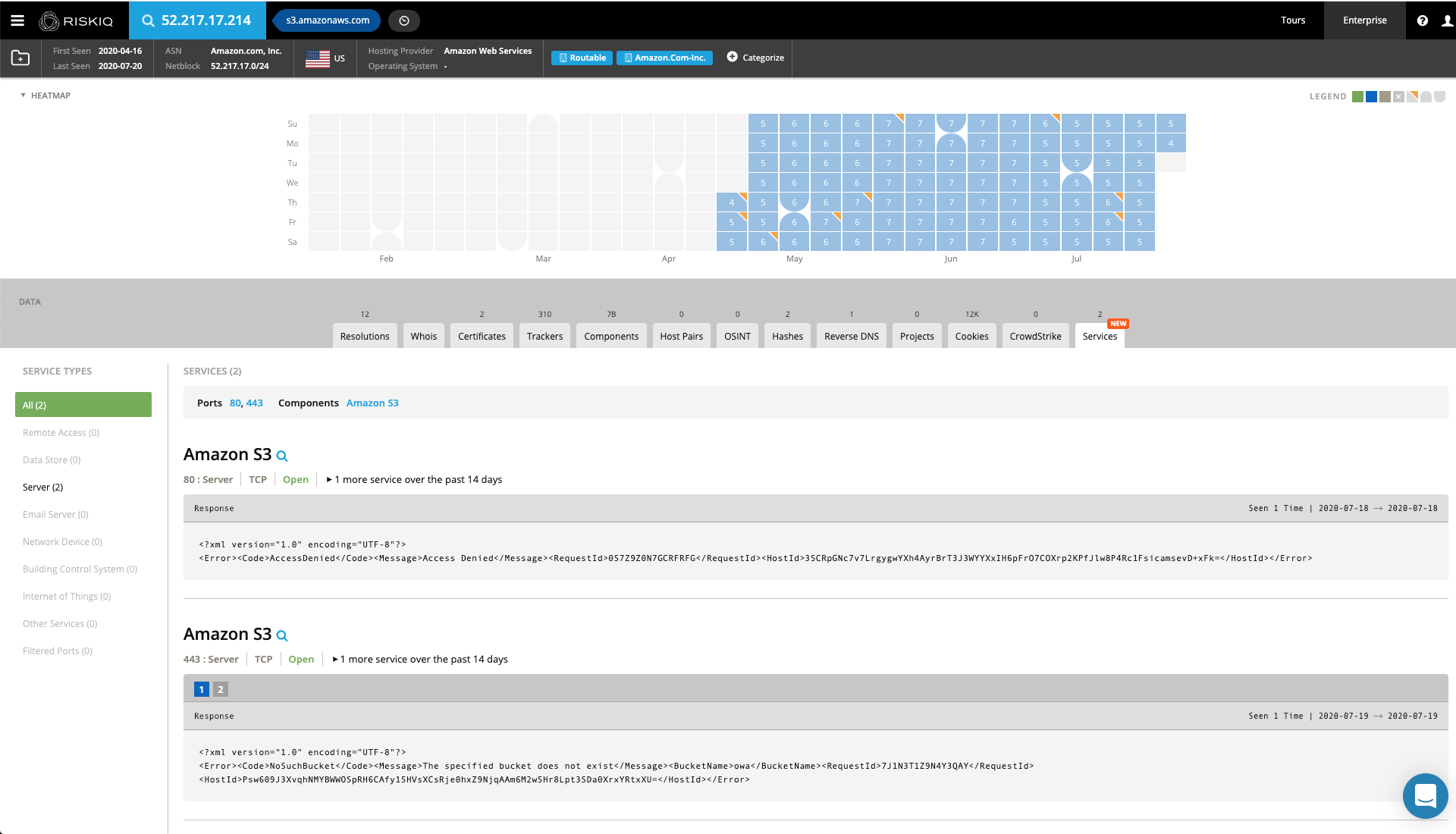
-Passive DNS resolution data
-WHOIS registrant and registrar details (current and historical)
-SSL certificate information
-Web tracker information found on pages — Google Analytics, Clicky, New Relic, and more
-Web component information — details about software and frameworks running on web servers
-Host pairs — connections between a web page and subsequent requests from that page
RiskIQ is trusted by:
-17 of the 25 largest banks in North America
-8 of the 15 largest global brands
-6 of the 20 largest high-tech businesses
-5 of the 10 largest U.S. healthcare institutions
-4 of the 15 largest U.S. media firms
-4 of the 20 largest U.S. manufacturers
How we are different
RiskIQ is the leader in Attack Surface Management with 10+ years of telemetry data, providing the most comprehensive discovery, intelligence, and mitigation of threats associated with an organization’s digital presence. RiskIQ’s PassiveTotal expedites investigations by connecting internal activity, event, and incident indicator of compromise (IOC) artifacts to what is happening outside the firewire. Additionally, PassiveTotal supports out-of-the-box integrations with Slack, Microsoft, MISP Threat Sharing, Splunk, QRadar, Maltego, and Phantom, with new integrations being regularly developed.
-For over 80,000 users and 300+ enterprises, PassiveTotal simplifies and accelerates event investigation and intelligently consolidates and analyzes data from multiple data sources. The world-class platform addresses a larger number of threats in less time than the traditional manual processes employed by investigators. In 2020, analysts routinely used PassiveTotal to investigate Covid-19 related ransomware attacks on hospitals and healthcare facilities.
-PassiveTotal is the only platform in which users looking to monitor specific indicators or keywords can be alerted when changes are detected. It has the ability to alert analysts of infrastructure changes based on collected data sets and most recent scans. PassiveTotal has continued to build on this monitoring framework and now supports a new range of query types focused on newly observed host domains and WHOIS registrant data.
- PassiveTotal is the only platform offering full collaboration in threat hunting in the form of "projects," which offer users the option to create public or private projects with names, descriptions, collaborators, and monitoring profiles. Visiting a project’s details shows a listing of all associated artifacts and a detailed history that retains all the context needed for one analyst to pick up where another left off. Threat actor profiles can be built within PassiveTotal and serve as a “living” set of indicators. As new information is discovered or found, it can be added to that project.

Community Choice Award Voting
Help This Nominee Win
Cast your vote by sharing this nominee’s profile on LinkedIn, Facebook, or X, using the buttons above. Each completed social share adds one Community Choice vote.
Voting closes July 18, 2026. Community Choice winners will be announced before Black Hat USA.
What is the Community Choice Award? →
The Community Choice Award is separate from the judged Cybersecurity Excellence Awards. It is determined entirely by public voting, so nominees can receive both jury recognition and Community Choice recognition.

