Photo Gallery

|


|
RiskRecon

Additional Info
| Company | RiskRecon |
| Company size | 50 - 99 employees |
| Website | RiskRecon.com |
NOMINATION HIGHLIGHTS
RiskRecon’s continuous vendor monitoring solution delivers risk-prioritized action plans that enable precise, efficient elimination of customers’ most critical third-party security gaps, custom-fitted to their organization’s risk policy.
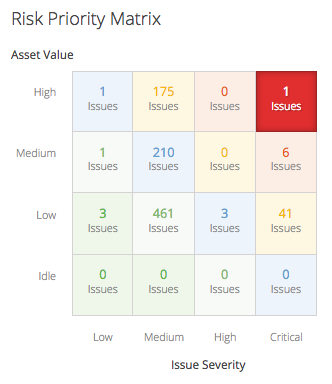
RiskRecon enables customers to instantly understand and rapidly act on their organization’s third-party risk. Solving risk requires two foundational elements: knowing the severity of the security issue and the value of the asset in which the issue exists. RiskRecon invented the algorithms that automatically and accurately determine asset value, completing the risk equation. In this way, RiskRecon provides companies with the world’s easiest path to understanding and acting on their third-party risk.
The company’s customers include the Global 2,000 and Fortune 500 companies, including some of the largest financial institutions, healthcare, and consumer brands in the world.
RiskRecon provides the following benefits to users:
Improved Efficiency:
Optimize analysts’ time and outside auditor resources; reduce review times by 25%.
Increase the amount of vendor coverage by a single analyst up to 300%.
Prioritize efforts based on vendor rating and identified gaps.
Proactively identify common exposures throughout your vendor portfolio.
Accelerate the evaluation of new (and potential) vendors.
Better Risk Outcomes:
Prioritize remediation activity based on real risk derived from asset value and issue severity.
Pinpoint critical vulnerabilities instantly.
Monitor performance changes continuously.
Identify other risk factors, such as fourth-party risks.
Enhanced Accountability:
Confirm that vendors are adhering to their own documented practices.
Verify vendor progress against corrective action plans.
Highlight exposures for board and executive management.
Demonstrate risk control quality to regulators and standards bodies.
Actionable Measurement:
Receive an actionable risk recommendation for each vendor.
Pinpoint potential exposures and root causes for 50+ security criteria.
Benchmark among your vendors and compare to industry best practices.
Track historical trends for your overall portfolio and each individual provider.
How we are different
Asset Valuation Algorithms.
RiskRecon invented the ground-breaking asset risk valuation algorithms that are critical to how enterprises manage third-party cyber risk. RiskRecon is the only firm in the world that can automatically determine the inherent risk value of systems by identifying indicators of risk value through analysis of system code, content, configurations, and characteristics. The company’s asset valuation algorithms automatically assign a value to cyber assets such as systems, domains, and networks. The algorithms also tag each asset with value indicators, including the system’s functionality and the data types it collects; these indicators enable risk professionals to immediately understand any asset’s value. This essential capability enables customers to easily understand how well their vendors are managing cyber risk and to know how to act on that risk.
Risk-Prioritized Action Plans:
Only RiskRecon can automatically determine the risk priority of issues, providing customers with action plans prioritized by risk. That’s because solving risk requires two foundational elements: the severity of the security issue and the value of the asset in which the issue exists. Because RiskRecon invented the algorithms to automatically determine asset value, RiskRecon provides customers with the world’s easiest path to understanding and acting on their third-party risk.
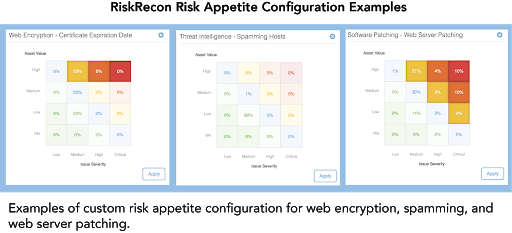
Custom Risk Policy Configuration:
RiskRecon’s automated risk appetite configuration capability enables enterprises to automatically produce assessments and action plans based on their unique risk requirements. Customers can set their own risk policy for each security criteria through a graphical user interface by selecting the combinations of asset value and issue severity to identify issues important to their organization. In addition to automatically creating custom-fitted risk assessments and action plans, organizations can similarly tune RiskRecon’s continuous monitoring to surface only the material risk issues that violate their risk policy.

Community Choice Award Voting
Help This Nominee Win
Cast your vote by sharing this nominee’s profile on LinkedIn, Facebook, or X, using the buttons above. Each completed social share adds one Community Choice vote.
Voting closes July 18, 2026. Community Choice winners will be announced before Black Hat USA.
What is the Community Choice Award? →
The Community Choice Award is separate from the judged Cybersecurity Excellence Awards. It is determined entirely by public voting, so nominees can receive both jury recognition and Community Choice recognition.

