Photo Gallery

|

|
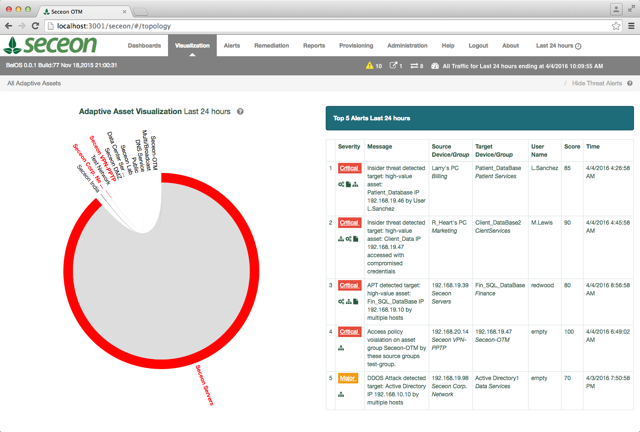
Seceon Open Threat Management Platform

Additional Info
| Company | Seceon |
| Company size | 43 employees |
| Website | http://www.seceon.com |
NOMINATION HIGHLIGHTS
In 2016 Seceon delivered the industry’s first and only fully automated real-time threat detection and remediation system to detect, analyze and eliminate cyber-threats in minutes. This is critical because today’s threats are causing a record number of breaches and data is being lost or compromised within a few hours of the breach.
Seceon’s Open Threat Management Platform is unique in the following ways:
1) It sees all types of threats: leveraging advanced data collection and analysis, machine learning, patent-pending predictive and behavioral analytics; it can detect traditional, as well as never seen zero-day threats.
2) It works using a big-fast data architecture that can process billions of inputs and generate correlated outputs of all related threat behavior in seconds. Allows for improved threat detection while minimizing false positives, it also reduces the number of threat activities that have to be analyzed.
3) It’s fully automated, utilizing dynamic rule sets, which means it never needs new rules to be added, never needs tuning, and never needs to be monitored – it does the analysis and reports the finding automatically in emails, texts. No need for a SOC team.
4) It stops the threat. It can dynamically write rules to firewalls and switches to stop connectivity of compromised devices to the outside world or to each other depending on the nature of the threat. It can disable a compromised or malicious insider’s credentials as well as isolate the device with exfiltrated data.
From breach to remediation in a matter of minutes – Seceon.
How we are different
Seceon’s Open Threat Management Platform is the first product to provide:
• An affordable: SoC-in-a-Box cyber security solution that automatically detects and stops all forms of cyber threats within minutes from the breach without human intervention.
• A solution that deploys in any environment: private, hybrid or public cloud in under 4 hours with untrained staff and never needs rule updates nor tuning.
• Immediate-ROI – by stopping attackers the same day they begin their active attack, Seceon can save companies tens of millions spent annually addressing data loss while dramatically reducing the number of cybersecurity tools and staff required.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

