Photo Gallery
 |

 |
Sonrai Security’s Sonrai Dig

Additional Info
| Company | Sonrai Security |
| Company size | 50 - 99 employees |
| Website | http://www.sonraisecurity.com |
NOMINATION HIGHLIGHTS
Identity and data access complexity are exploding in your public cloud. Tens of thousands of pieces of compute, thousands of roles, and a dizzying array of interdependencies and inheritances. First-generation security tools miss this as evidenced by so many breaches. Sonrai Dig de-risks your cloud by finding these holes, helping you fix them, and preventing those problems from occurring in the first place.
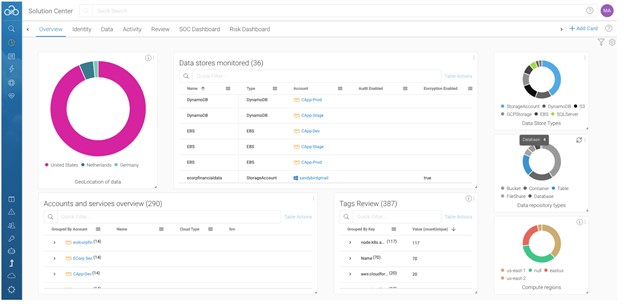
Sonrai Dig is built on a sophisticated graph that continuously identifies and monitors every possible relationship between identities and data that exists inside your AWS, Azure, and GCP cloud environments. Dig’s Governance Automation Engine automates workflow, remediation, and prevention capabilities across cloud and security teams to ensure end-to-end security.
Powered by a cloud identity graph, Sonrai Dig combines Cloud Security Posture Management (CSPM), Cloud Infrastructure Entitlements Management (CIEM), and data security in one platform. This enables enterprise companies to enforce compliance, achieve and maintain least privilege, enforce separation of duties, and lockdown critical data: all ways to minimize exposure to threats in the cloud. Best practices, workflow, advisors, and automation supports cross-team cloud security operations.
How we are different
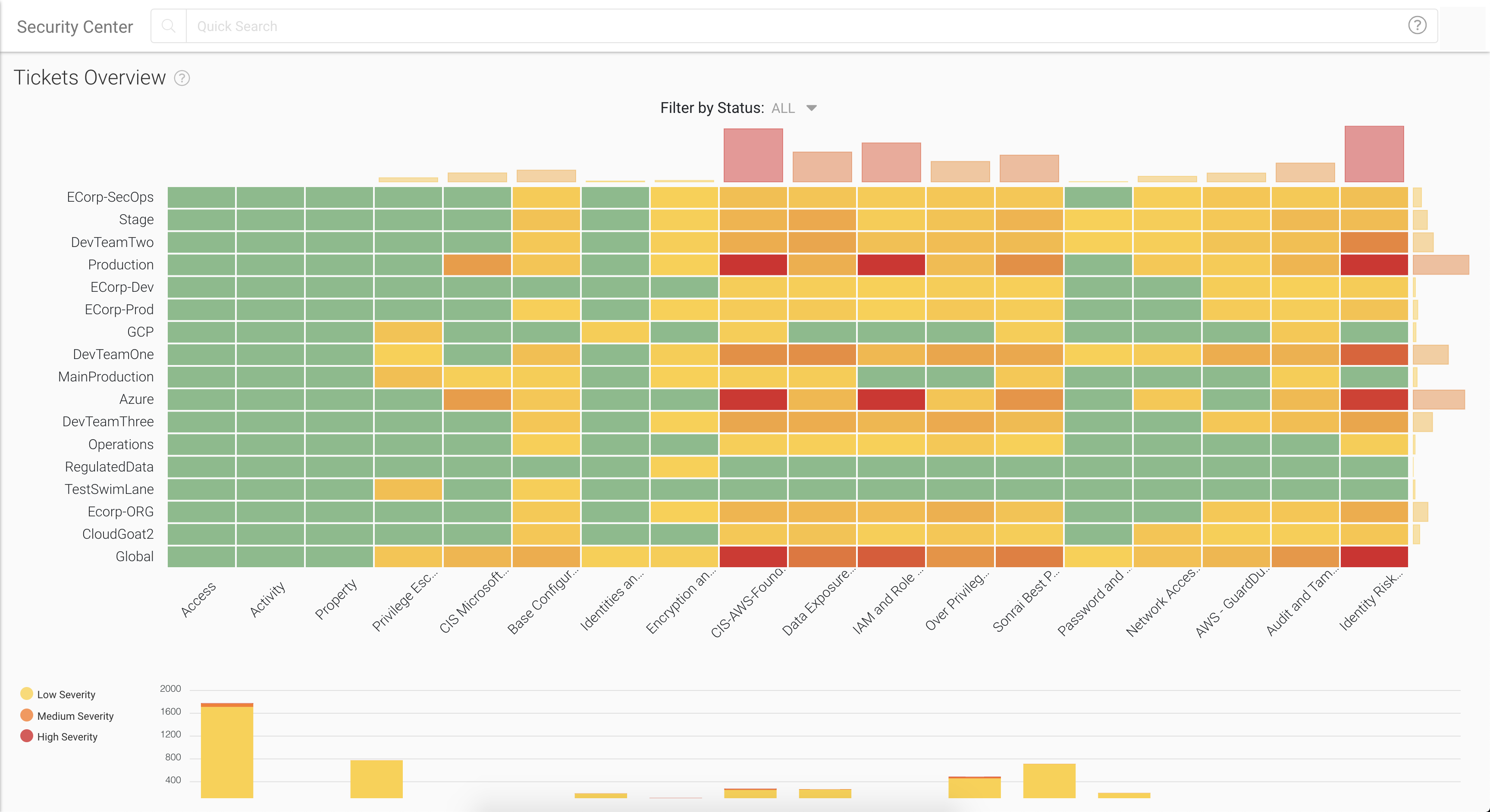
*Eliminates all identity risks -- Sonrai Dig uncovers all identity and data relationships between people and non-people identities (admins, roles, compute instances, serverless functions, and containers) across multi-cloud accounts and third-party data stores. Sonrai Dig, our identity and data security platform, graphs all access paths to enforce Least Privilege, and workflow enables certification of identities.
*Discovers, Locks Down, and Monitors “Crown-Jewel” Data --Inside Sonrai Dig, our Crown Jewel Monitoring capabilities relentlessly monitors critical data sitting inside object stores (e.g. AWS S3, Azure Blob) and database services (e.g. CosmosDB, DynamoDB, RDS). Suspicious access activity or undesirable changes in access rights are immediately flagged.
*Governance Automation Engine --Sonrai Dig’s Governance Automation Engine helps companies shift left and integrate teams via organized analysis, alerts, and actions that align with how organizations use public cloud. The platform allows customized monitoring and views for development, staging, or production workloads and an API architecture that can be integrated into a CI/CD process.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



